Seekr is a versatile toolkit with an intuitive web interface for collecting and managing OSINT data. Seekr’s Backend is written in Go and provides many features/tools for data collection, organization and analysis. This is a very suitable tool for you to do OSINT as it will make it easier for you to find and manage the data you need. In this article, I will show you how to install and use this tool.
| Join the channel Telegram belong to AnonyViet ???? Link ???? |
Features of Seekr
Seekr combines note taking and OSINT into a single application. Seekr can be used in conjunction with your existing tools. Seekr is designed for OSINT and optimized for real-world use cases.
Main features:
- Has a computer interface
- OSINT targets are stored in the database
- Integrate many popular OSINT tools (e.g. phoneinfoga)
- GitHub for emailing
- There is a target tag used to manage each target in the database
- Detect other targets integrated in the target tag
How to install Seekr
Step 1: Before installing Seekr, you must make sure your system, here I use Ubuntu, has git and go installed.
You can install go with the command:
sudo apt install golang-go
And install git with command:
sudo apt install git
Step 2: Download Seekr’s repo with the command:
git clone https://github.com/seekr-osint/seekr
Step 3: Go to the repo you just downloaded and start Seekr with the command:
cd seekr go run main.go
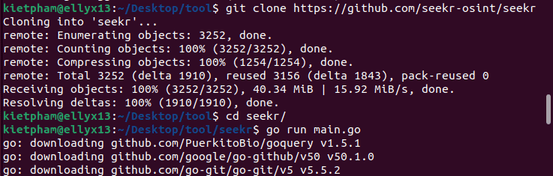
So you have successfully installed and started Seekr. Next we will learn how to use Seekr.
How to use Seekr
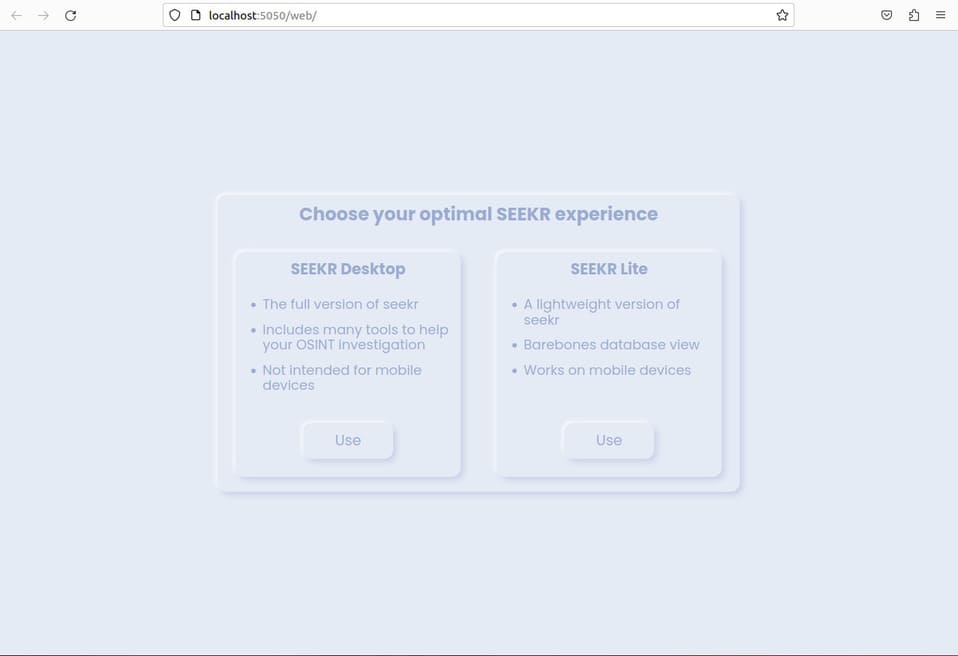
When you launch Seekr, the program will automatically open the browser and access the web interface. I will choose SEEKR Desktop.
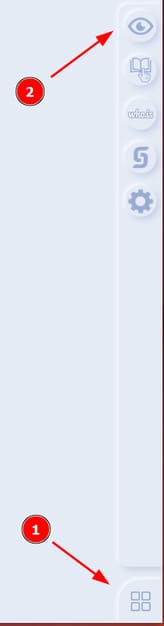
In the lower left corner is Seekr’s tools menu. You choose the first tool to open the target card.
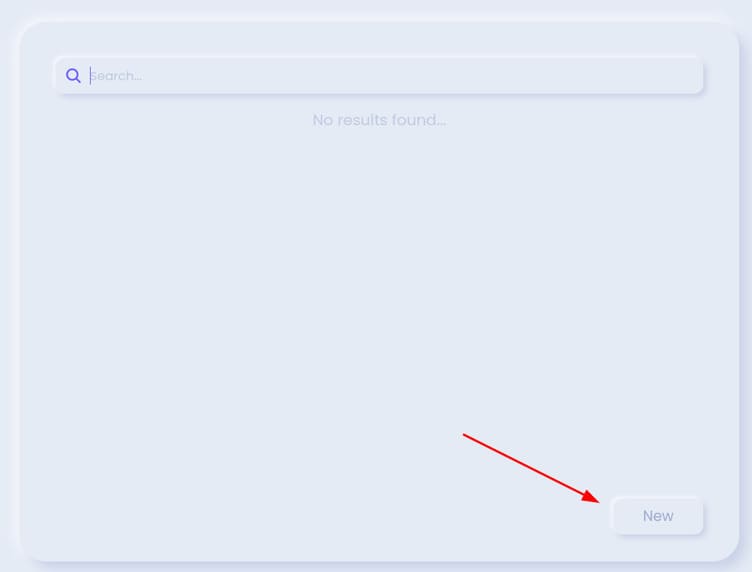
You press new.
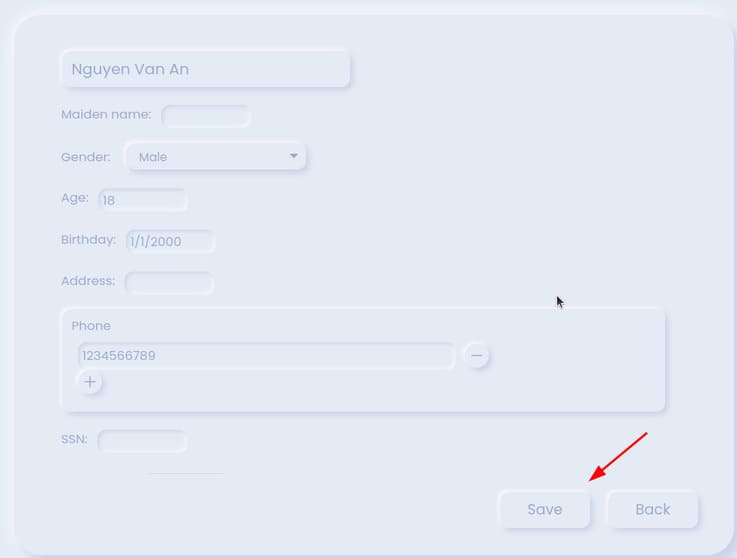
Here, you can enter a lot of information of the target such as full name, gender, address, …. After entering the information, press Save.
Click the avatar icon of the newly created target.
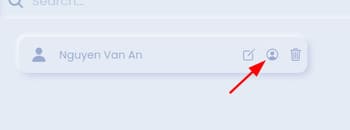
Here, you can enter the target’s username to find other accounts that use this information. If that’s the account you need then press Accept to add to the target tag.
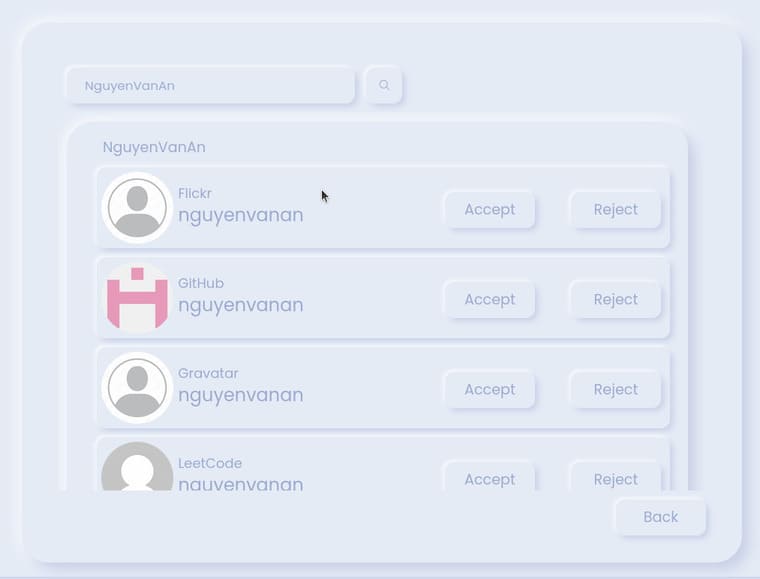
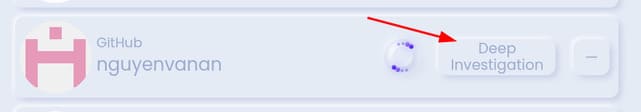
In the target tab, you can further investigate the newly added accounts of your target by pressing Deep Investigation.
The second tool in the menu is a page that aggregates all the OSINT tools you need for your target’s crawling.

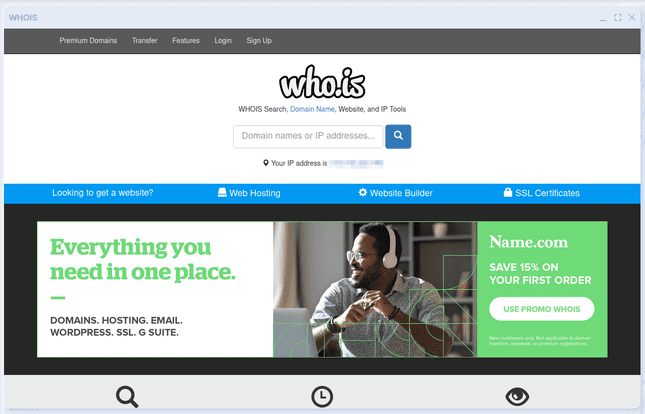
The 3rd tool in the menu is Whois. You can exploit a lot of related information of the domain and ip you want. However, at the time of testing, this feature is faulty.
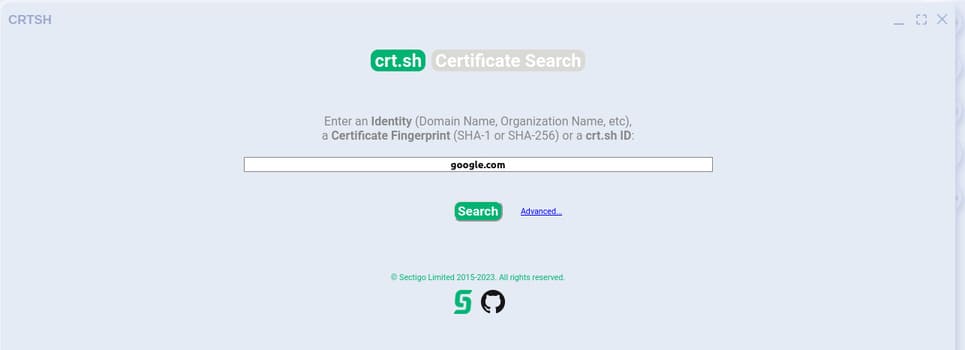
The 4th tool in the menu is CRTSH. You can use this tool to search for certificates related to the domain you want.

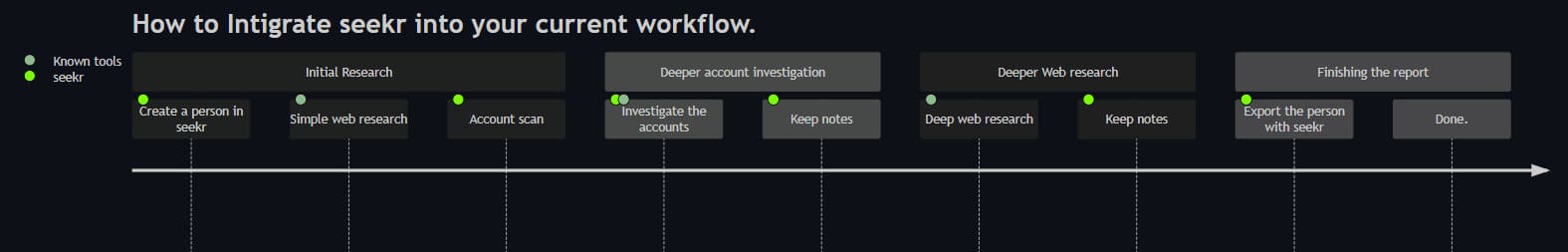
To get the most out of Seekr, you can use the following procedure.