Returning to the Rat Series, today Anonyviet will bring you a Rat named the father of Rats, LimeRat, which was developed by a group of authors called NyanxCat and shared on Github. Why is it called the father of the mouse, please join me in analyzing it below.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
LimeRat Features
- .NET
- Coded in Visual Basic .NET
- Connection
- Use pastebin.com as ip:port, Instead of DNS noip.com
- Plugins
- Use a plugin system to reduce size and reduce AV detection
- Encode
- Communication between server and victim is encrypted with AES
- Spreading
- Infect all files and folders on USB drivers
- Bypass
- Low chance of being scanned by virus, can start with windows undetected
- Light
- The generated rat size is about 25KB
- Anti-Virtual Machine
- Self-uninstall if virtual machine to avoid scanning or analysis
- Ransomware
- Encrypt files on all HHDs and USBs with the .Lime . extension
- XMR Miner
- High Performance Monero CPU Miner with Idle User \ Operation Optimization
- DDoS
- Create a powerful DDOS attack to make an online service unavailable
- Crypto Stealer
- Stealing sensitive crypto data
- Lock screen
- Prevent users from accessing their Windows GUI
- And more
- Auto connect
- Using RDP
- File management
- Steal Password
- Remote control
- Bitcoin Miner
- Download File from victim
- Keyloggers
That is just a small part of the utilities integrated into this LimeRat v0.1. The use and interface are also very simple and beautiful, making LimeRat a rat with a relatively high number of users compared to other Rats at the same time.
How to download and use LimeRat
To download you can click the link below. Remember to turn off your antivirus before doing so to avoid deleting important Rat files.
If you want to play with the Source, download it above and use it to download the Debug version to use.
After downloading the Debug version successfully. You proceed to extract to the computer screen for easy operation.
Run the LimeRAT.exe file to open the tool.
Then there will be a notice board. Please add the NAT port on the modem (Key AES is nyancat)

After entering the Rat interface, go to the Builder tab and then go to the web Pastebin.com Create a new paste with the following content:
your ip:port ->> 127.0.01:8080 (example)
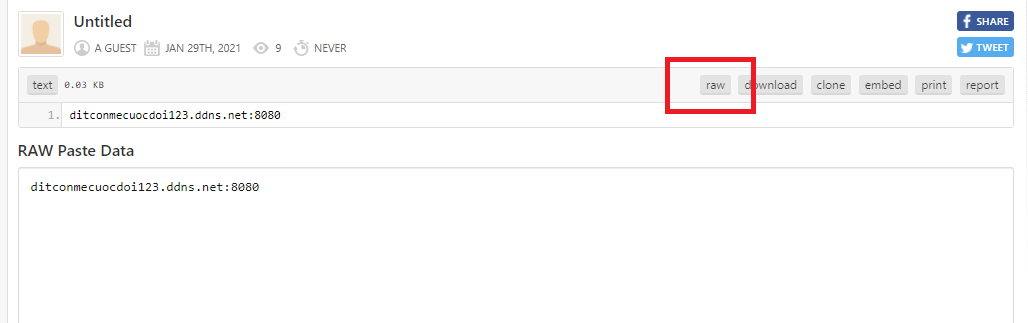
Then save and get the Raw url and paste it into the Pastebin Url section in LimeRat.
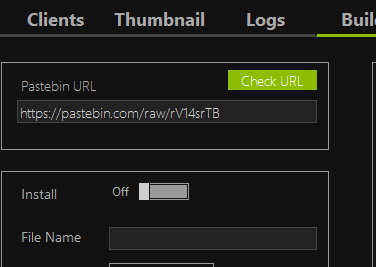
Adjust the parameters of Rat to suit your liking and then click Build to proceed with creating the rat.
After the victim is poisoned, you can easily control the victim at will
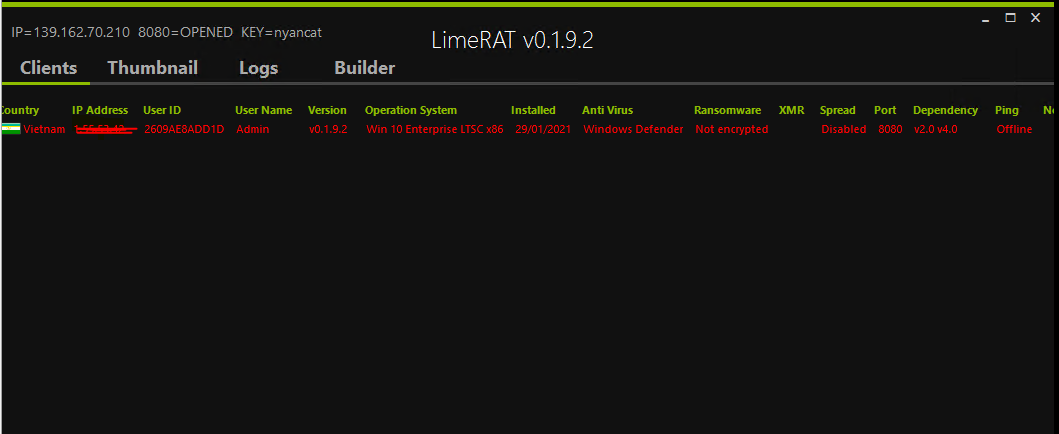
Get data files, RDP, crypt all files of the victim with ransomware… You can do whatever you want on this LimeRat.
Good luck
TMQ.