I’m sure everyone has been infected with a computer virus at least once. Most of the viruses you encounter will cause some mild trouble, just installing anti-virus software or reinstalling Windows will fix it. But there are some computer viruses that can destroy data including causing hardware damage that turns your computer into a brick.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
Here is a list of the 10 most notorious malicious computer viruses in history. These malware caused massive harm, amounting to billions of dollars, and disrupted critical infrastructure in real life.
1. ILOVEYOU
ILOVEYOU is considered as one of a kind most harmful computer virus ever created. It wreaked havoc on computer systems worldwide with about $10 billion worth of damage. 10% of computers in the world are believed to have been infected with viruses. The bad thing is that governments and large corporations have taken the mail system offline to prevent infection.
The ILOVEYOU virus was created by two Filipino programmers, Reonel Ramones and Onel de Guzman. What it did was used social engineering to get people to click on attachments. The attachment is actually a file command save as TXTbecause windows at the time hide the file extension (extension).
Once clicked, it will automatically send to everyone on the user’s mailing list and proceed to overwrite other files with the virus itself, causing computer cannot start Okay. Both virus authors are not legally responsible as there were no malware laws at the time. This led to the enactment of the Law on E-Commerce to solve the problem.
2. Code Red
Code Red first appeared in 2001 and was discovered by two employees of eEye Digital Security. It was named Code Red because the two were drinking Code Red Mountain Dew (energy drink) at the time of discovery.
The virus targets computers with web servers installed Microsoft IIS , exploiting buffer overflow in the system. It leaves very little trace on the hard disk as it can run entirely on RAM, with a size of 3,569 bytes.
Once infected, it will proceed to create hundreds of copies of itself but due to a programming error, it will clone more and end up eating more system resources.
The virus then activated DDOS on a number of IP addresses, the most famous of which was the attack on the White House website. Red Code also creates a backdoor for hackers to break into the server.
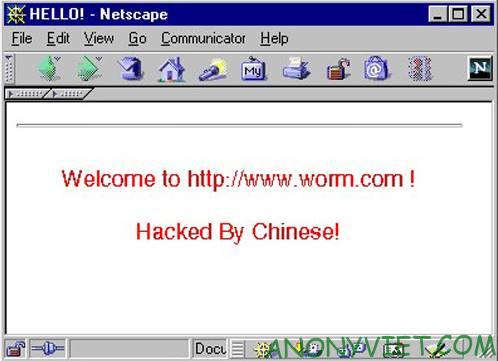
The most memorable is the message that the virus left on the hacked Website is the words “Attacked by the Chinese!” which itself has become memes. A patch was later released and it is estimated that it caused $2 billion. A total of 1-2 million servers were affected, which is staggering considering there were only 6 million IIS servers in the world at the time.
3. Melissa
Named after a dancer from Florida, it was created by David L. Smith in 1999. Melissa is an infected Word document posted on the usenet group alt.sex, self-referred to as a list of passwords for porn sites. This got people curious, and when it’s downloaded and opened, it will enable macros inside and activate the virus.
The virus will automatically send mail to the first 50 people in the user’s email address list and this causes an increase in email traffic, disrupting email services of other governments and corporations. Sometimes it does corrupt documents by inserting malicious code into the file.
Smith was eventually caught when they traced the first Word file, law enforcement had arrested him less than a week since the outbreak of the Melissa Virus.
Smith cooperated with the FBI in arresting other virus creators, famous among them virus creator Anna Kournikova. For his cooperation, he served only 20 months and paid a $5000 fine for his 10-year sentence. According to reports, the virus has caused $80 million in damage.
4. Sasser
A Windows virus first discovered in 2004, it was created by computer science student Sven Jaschan, who also created the virus. Netsky.
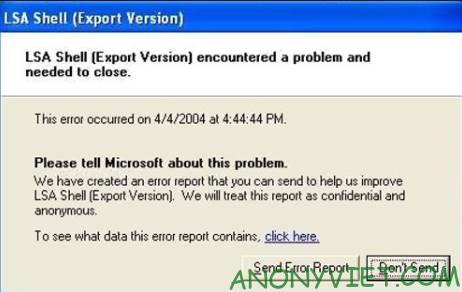
The Sasser virus took advantage buffer overflow vulnerability in the Local Security Authority Subsystem Service (LSASS), the service that controls the security policy of the user accounts that cause problems for the computer. It also uses system resources to transmit itself to other machines via the Internet and automatically infect others.
The impact of the virus was widespread because in Windows patching vulnerabilities, many computers were still not up to date. This has led to more than a million infected devices, destroying important infrastructure such as airlines, news agencies, public transport, hospitals, public transport, etc. Overall, the damage is estimated at 18 billion USD. Jaschen was tried as a juvenile and received a 21-month suspended sentence.
5. Zeus
Zeus is a Trojan created to infect Windows computers. The most popular is Zeus act as a Keylogger to record keyboard logs to steal passwords. Most computers have been infected through phishing sites
First identified in 2009, Zeus has compromised thousands of FTP accounts and computers from large multinational corporations and banks such as Amazon, Oracle, Bank of America, Cisco, etc. Botnet operators Zeus used it to steal social media logins, emails, and bank accounts.
In the US alone, it is estimated that more than 1 million computers are infected with viruses, in the US 25%. The whole operation is very sophisticated, involving people from all over the world acting as scammers to smuggle and transfer cash to the ringleaders in Eastern Europe.
About $70 million was stolen and in possession of the ring. 100 people have been arrested in connection with this activity.
6. Conficker
Also called Downup or DownadupConficker infects computers using vulnerabilities in the OS to create a botnet.
Malware has been able to infect more than 9 million computers around the world, affecting governments, businesses and individuals. It was one of the largest viral infections ever, causing an estimated $9 billion in damage.
Conficker works by exploiting a network service vulnerability that has a security hole of Windows. Once infected, this Conficker will reset account policies, block access to Windows update sites and anti-virus program websites, disable some services, and lock user accounts.
After that, the virus installs software that will turn the computer into a botnet and scare software to trick users. Microsoft later provided a fix and patch with many antivirus vendors providing updates to remove the malware.
7. Stuxnet
Supposedly due to Israel Defense Forces together with the US Government createdStuxnet is an example of a virus created with the intent of cyberwarfare, as it aims to disrupt Iran’s nuclear research and development efforts. It is estimated that Stuxnet has destroy 1/5 of the nuclear centrifuges of Iran, and nearly 60% of infections are concentrated in Iran.
Stuxnet is designed to attack industrial Programmable Logic Controllers (PLCs), allowing automation of processes in .
Stuxnet specifically targets the devices of Siemens company and distributed via infected USB drives. It changes the speed of the machine, causing the machine to fail. If the infected computer does not contain Siemens software, it will lie dormant and infect the machine quite well. Siemens has finally found a way to remove malware from their software.
8. Mydoom
Appeared in 2004, Mydoom is a virus for Windows, becoming one of a kind fastest spreading email virus since ILOVEYOU. The author of the Mydoom Virus has not been found and it is believed that the creator was paid to create it because it contained the message: “andy; I’m just doing my job, nothing personal, sorry ”.
Mydoom spreads itself by appearing as email transmission error and contains its own attachment. Once executed, it sends itself to the email addresses contained in the user’s email contacts and copies itself to any folder of the P2P program to propagate itself through that network.
Mydoom first opens a backdoor to allow remote access and then it launches a denial of service attack on the controversial SCO Group. It is believed that this worm was created to sabotage SCO due to a conflict over ownership of some Linux code. Mydoom caused an estimated $38.5 billion in damage, and the worm is still active in some form to this day.
9. CryptoLocker
CryptoLocker is a form of ransomware Trojan that targets computers running Windows. It uses several methods to spread itself, such as email, and once a computer is infected, it encrypts the data on the hard drive and any cryptographically connected storage devices. RSA public key.
Although malware can be easily removed from a computer, the file will still be encrypted. The only way to unlock the files is to pay the ransom ahead of time. If the deadline is not met, the ransom is greatly increased or the decryption keys are deleted. The ransom is usually up to $400 in cash or prepaid bitcoin.
The ransom operation was eventually halted as law enforcement agencies and security companies managed to take control of part of the network. CryptoLocker and Zeus botnets .
Evgeniy Bogachev, the mastermind, has been charged and encryption keys have been released to the affected computers. From the data collected from the raid, the estimated number of infections was 500,000 people, with the number of ransom payers being 1.3%, up to 3 million USD.
10. Flashback
Although the ability is not as harmful as the above 9 viruses, Flashback is one of the few Malware on Mac because it shows that the Mac is still infected with the virus. Flashback was first discovered in 2011 by anti-virus company Intego in the form of a fake Flash settings.
In its newer version, users only need to enable Java. Flashbacks propagate themselves using hacked websites to attach malicious JavaScript code. Once installed, your Mac becomes part of a botnet of other infected Macs.
More than 600,000 Macs were infected at the time, including 274 in the Cupertino area, where Apple is based.
Oracle announced the fix and Apple released an update to remove Flashback from everyone’s Mac. Flashbacks are still on the Internet, with an estimated 22,000 Macs still infected in 2014.