A critical vulnerability in WinRAR – the most popular file compression software for Windows used by millions of people today, can execute commands on the computer just by opening the .rar archive.
| Join the channel Telegram belong to AnonyViet ???? Link ???? |
Recently, a new security vulnerability was found in WinRAR, with code CVE-2023-40477, CVSS score of 7.8. This vulnerability allows remote attackers to execute arbitrary code on computers with WinRAR installed. Malware attached to the compressed file can gain control of the computer if the user opens the compressed file from winrar.
The cause of the problem stems from the lack of data validation provided by the user. This lax validation can lead to a situation where memory access exceeds the buffer allocated for file compression, creating a favorable environment for hackers to attach malicious code to the compressed file.
WinRAR quickly patched this dangerous vulnerability shortly after. In the latest version, WinRAR 6.23, vulnerability CVE-2023-40477 has been successfully patched. Users need to quickly update to the latest version to avoid hackers spreading Viruses through compressed files.
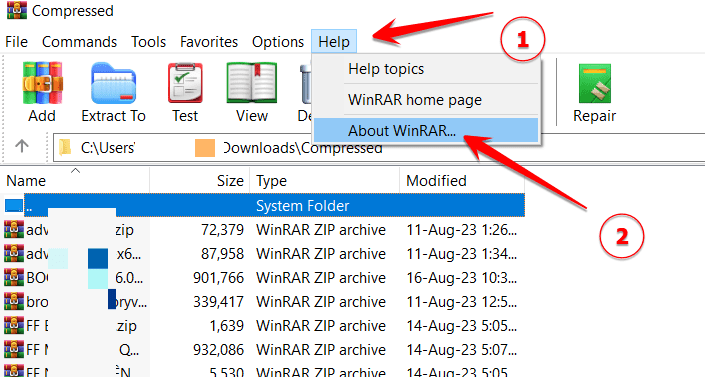
To check the version of Winrar you are using, open Winrar and select Menu Help -> About
Check Winrar version if lower than 6.23 then need to update to the highest version.
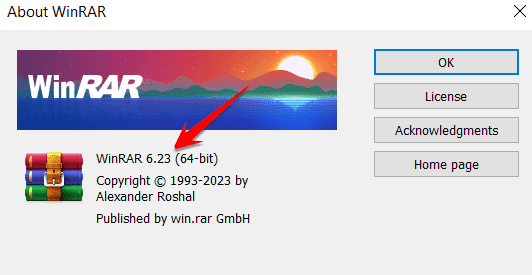
To update Winrar, download the software from the official Web site rarlab.com to install.
If you want license activation forevercan use Key in this paragraph.
If you do not trust Winrar, you can use 7-Zip software or wait for Windows 11 to upgrade RAR, 7-Zip and GZ compression and decompression in an upcoming update.