Gunt is a tool OSINT helps you track objects with Gmail. When you know someone’s Gmail email address, you can completely check what Google services that gmail account is using, thereby tracing the object, see who the email owner is. Ghunt will help you quickly automate the search for people by email.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
Uses of Ghunt
Ghunt is an open source tool that helps you find active Google IDs, YouTube channels and Google services that users are using.
Ghunt allows you to analyze your target’s “trace” based on existing emails. This OSINT tool, can extract the account owner name and Google ID, YouTube channel and active Google services, including Photos and Maps.
Ghunt may also reveal public photos, phone model, make, firmware and installed software, and possibly the user’s physical location.
Currently Ghunt can extract information including:
- Gmail owner’s name
- The last time the profile was edited
- Google ID
- If the account is a Hangouts Bot
- Google services enabled (YouTube, Photos, Maps, News360, Hangouts, etc.)
- YouTube channel
- Username may be different
- Public photo (P)
- Phone models (P)
- Phone software (P)
- Installed software (P)
- Google Maps Reviews (M)
- Possible physical location (M)
- Events from Google Calendar (C)
(P) requires the target account to have default settings Allow the people you share content with to download your photos and videos on Google Album Archive or if the “subject” used to use Picasa linked to their Google account.
(M) requires Google Maps reviews to be public (they are set by default).
(C) requires the user to make Google Calendar public (default is Private Calendar).
How to use Ghunt to find information using Gmail
To use Gunt you first need cookies of the Google account. You can create a spam Google/Gmail account to track other accounts.
Log in with your Google account to the page https://accounts.google.com/.
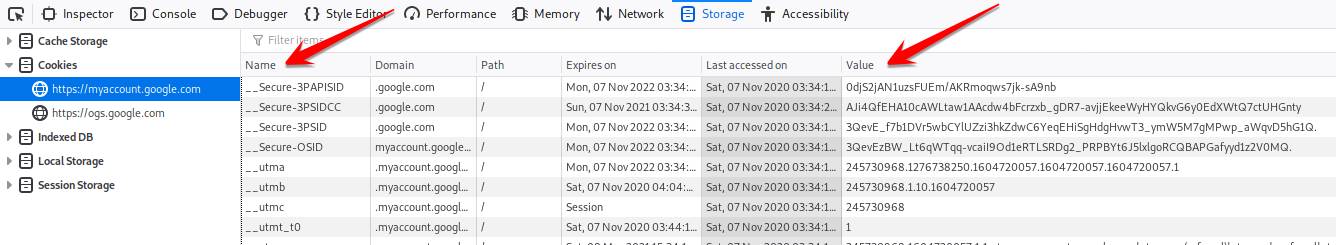
- If using Chrome: press F12 -> select via tab Application -> Storage -> Cookies.
- If using Firefox: press Shift + F9 -> Storage -> Cookies. (recommended to use Firefox on Kali linux to get cookies too)
Copy the parameters in cell Value of the:
- __Secure-3PAPISID:
- APISID:
- SAPISID:
- HSID:
Next on Kali linux 2019 and above (installed python3), open Terminal and type the command:
git clone https://github.com/mxrch/GHunt.git cd GHunt pip3 install -r requirements.txt python3 check_and_gen.py
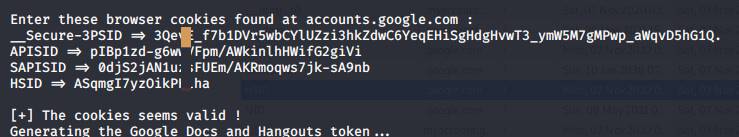
Enter the parameters of Google Cookies as in the above step:
If you see the message seems valid is success!
Now we will proceed to trace the gmail account owner. Use command:
python3 hunt.py email-cần-truy-vế[email protected]
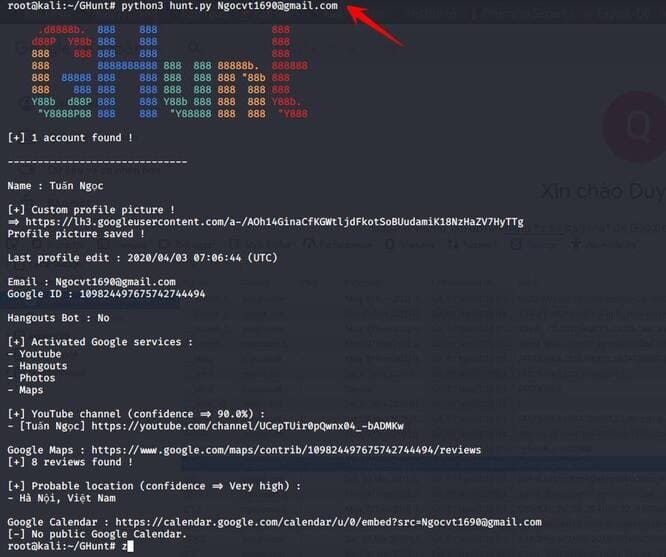
For example, I will find the owner of the email [email protected] What Google services are you using, then we will type the command:
python3 hunt.py [email protected]
Wait for Ghunt to scan for a while, we will have the results of the owner of the above email account:
According to the search results, you will see that the owner of this email is: Tuan Ngoc, living in Hanoi, using Youtube, Photos, Maps services. This account has a review on Google Maps and a Youtube channel
Thus, with public information, we can easily collect anyone’s personal information when we know that person’s gmail. This is one of the OSINT tools I find quite useful.