Product information:
- Capacity: 10.4 MB
- Release date:
- Update day:
- Request: Windows 2000/XP/Server 2003/Vista/7/8/8.1/10
Prey – Anti-theft and locator for computers
Currently, in the age of technology, owning a laptop is no longer a distant thing for the vast majority of technology users. Serving work, entertainment and study; There are many things users can do with a laptop. But after all, the value of a laptop is still quite large compared to the average income of the Vietnamese people. If you spend a large amount of money to buy and have it stolen, it must be heartbreaking. But how does PREY fix this? Read the article below and you will understand!
| Join the channel Telegram belong to AnonyViet 👉 Link 👈 |
Some key features of Prey . software
- 100% accurate geolocation: Prey: Locate by GPS or via the nearest Wifi network to localize and fix your device’s location.
- Automatically connect to Wifi: If enabled, this software will try to connect to the nearest Wifi network.
- Low capacity and low use of computer resources: This software is almost independent of other software and leaves no trace in memory until activated.
- Identify the thief: This tool can even help you take pictures of computer thieves with a webcam. Through this image, you can identify the thief and find out his location.
- Activity tracking: This software captures some activity on the screen. So, if you’re lucky, you might even know the thief’s email and Facebook account.
- Keep information safe: This tool helps to hide Outlook or Thunderbird data and click the option to clear the password kept.
- Block unauthorized access: If you do not enter the correct password, you will not be able to open the computer.
- Auto update: Prey supports automatic update of new points, so users will not need to reinstall every time a new version is updated.
PREY INSTALLATION INSTRUCTIONS:
You go to the homepage at the link at the beginning of the article to create an account (very simple):
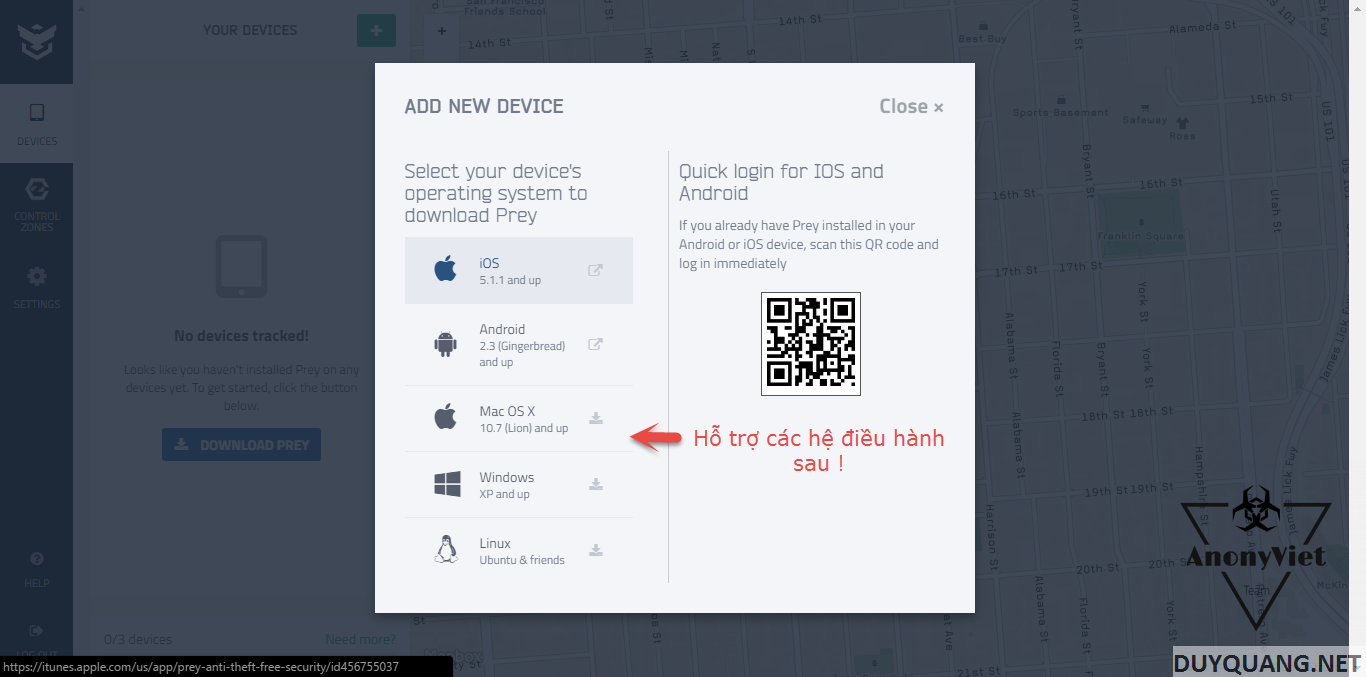
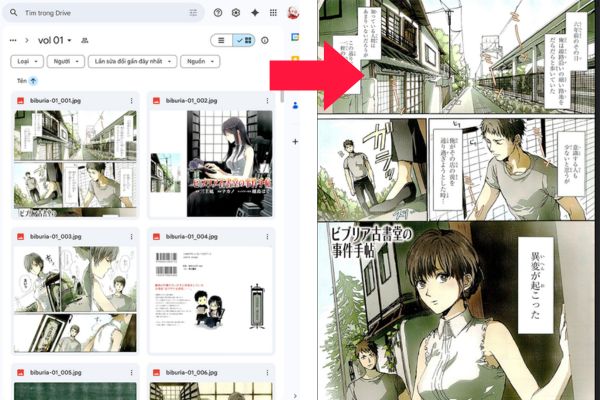
PREY supports a wide range of operating systems both for computers and phones.
Download in progress Setting as usual (Select Run Administrator )
Select Finish to switch the window as below
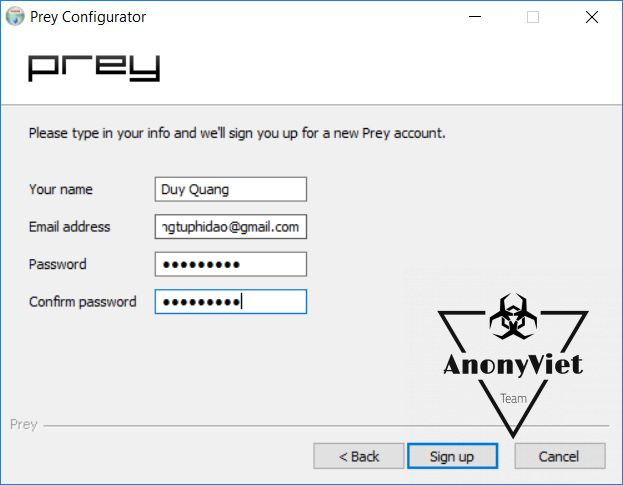
Line 1: New User => Create an account if you don’t have one yet
Line 2: Existing User => Already have an account
- In this case I choose line 1: New User to create a management account for Prey
After completing this process, it means that a tracking software has been running in the background on your computer and you can only control it through the homepage!
Then there will be a Email sent, and you log in to start managing the remote computer
INSTRUCTIONS FOR USE PREY:
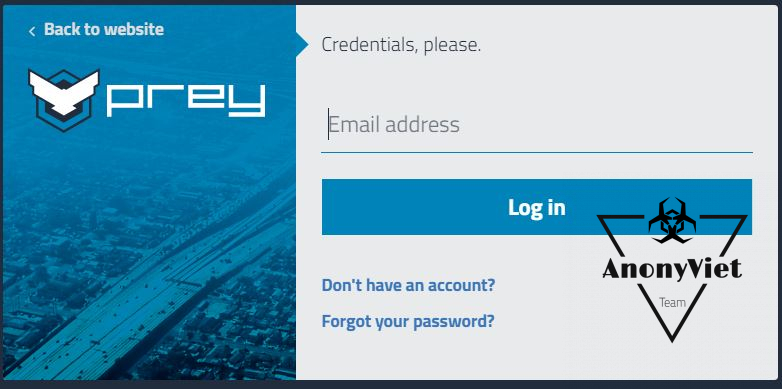
All operations using Prey are Web-based, you are required to log in to your Prey account on the Website to monitor your computer.
-
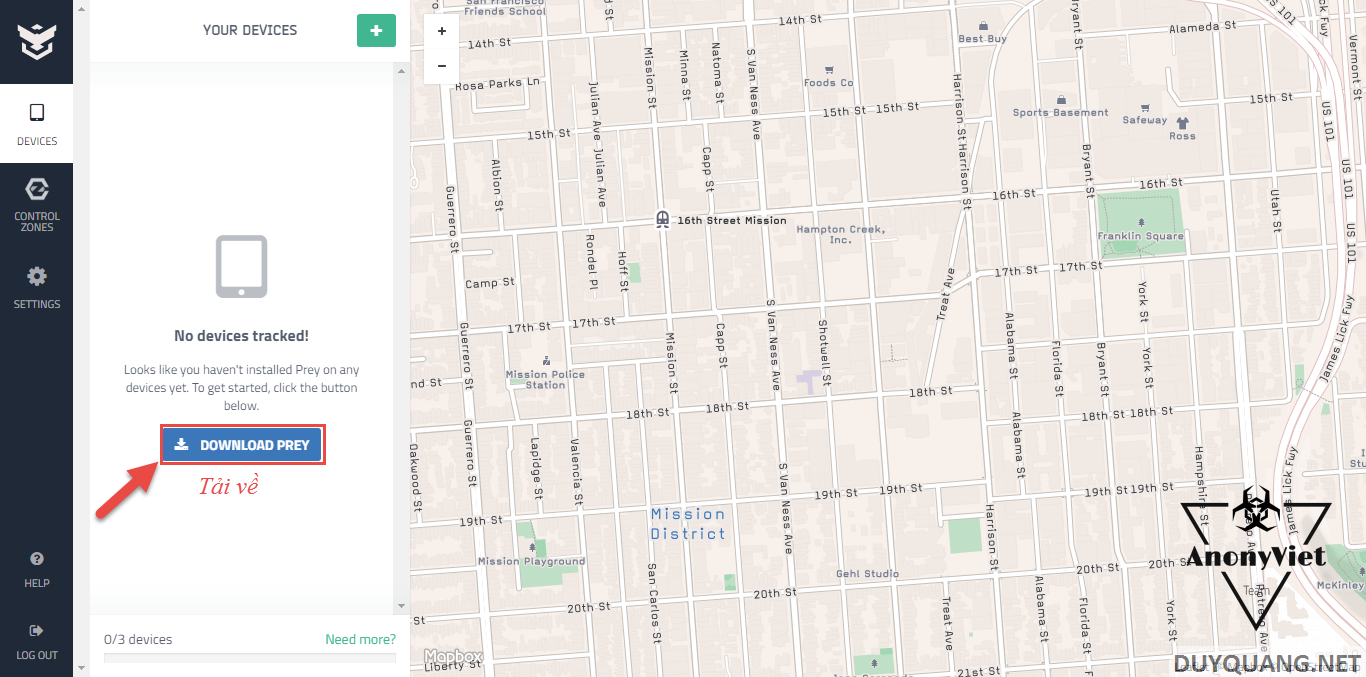
After the installation is complete, go to the PREY homepage to enter the control system by Log in (Picture below) !
After logging in a console will appear for you like picture below
- If the device is installed, it will display your device’s photo and name, if correct, click on your device to determine the GPS location of the device.
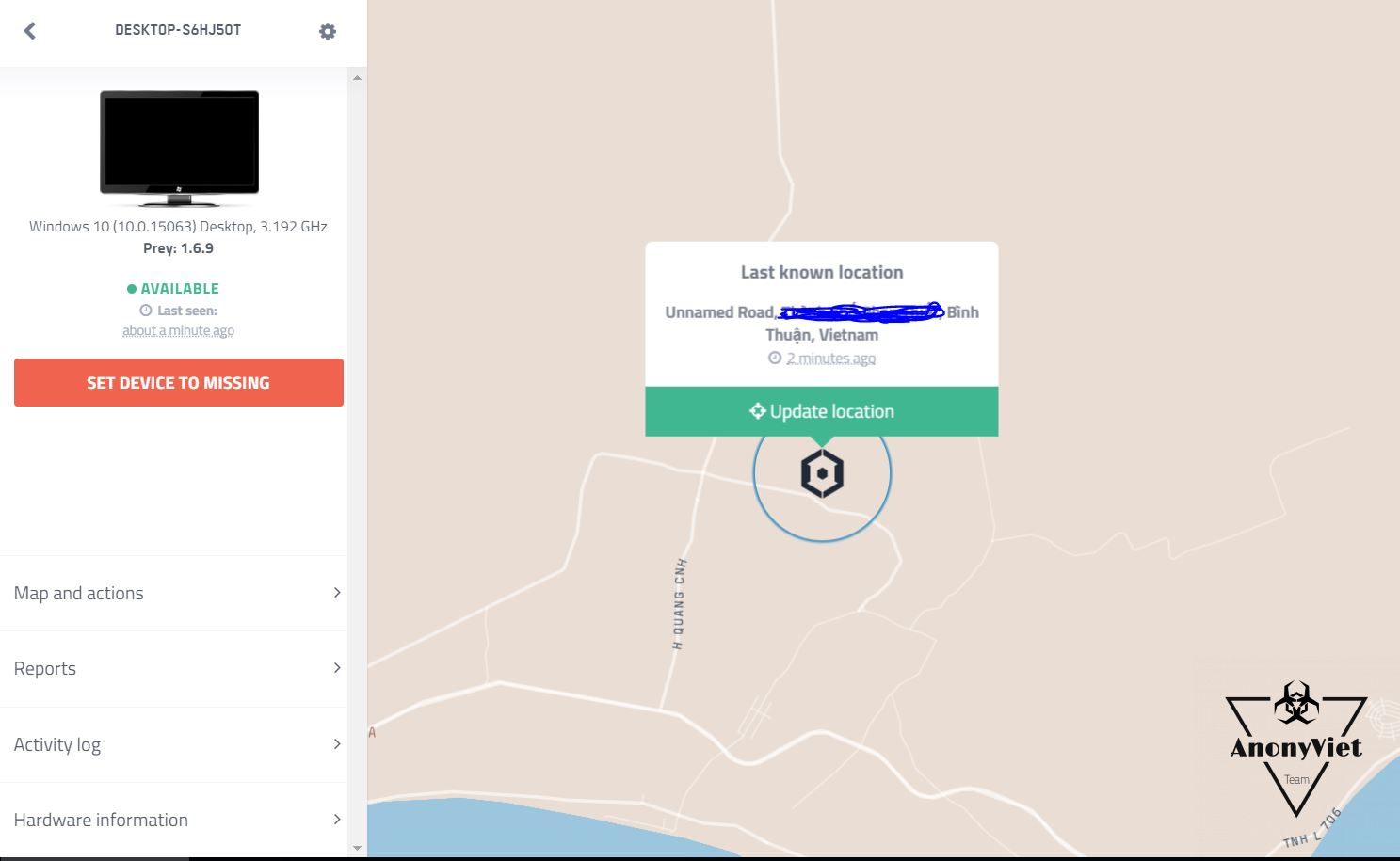
Below is a screenshot when I have successfully located it
- Although it is a little bit different from my house, but it is not more than 500m, you can zone and investigate if you want.
If you want to report theft, click the button like the image below on the right side of the screen.
- PREY will update the device information and send the location to your email at a preset interval. Include a screenshot of the object (if the device has a webcam).
On the right side of the screen are support tools such as:
- Sound alarm: Make your computer emit a continuous warning sound, so that everyone around can recognize and catch the thief
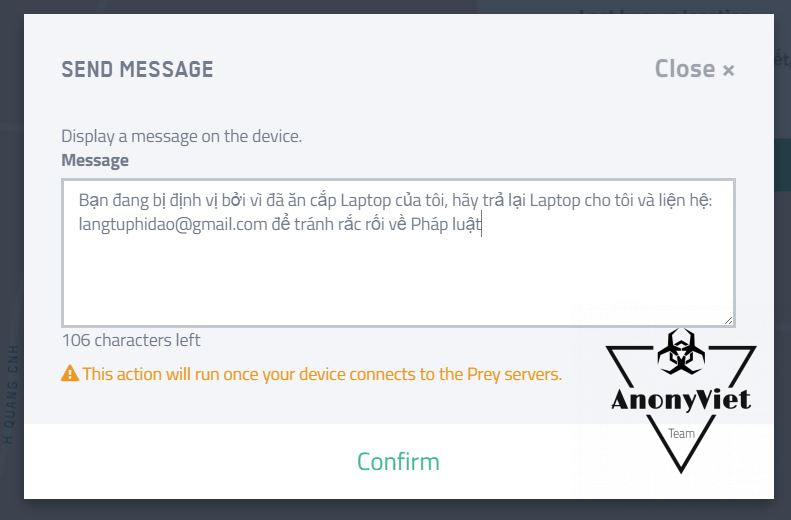
- Send message: Open a notification interface with a message displayed on the screen to warn the object that is using the device.
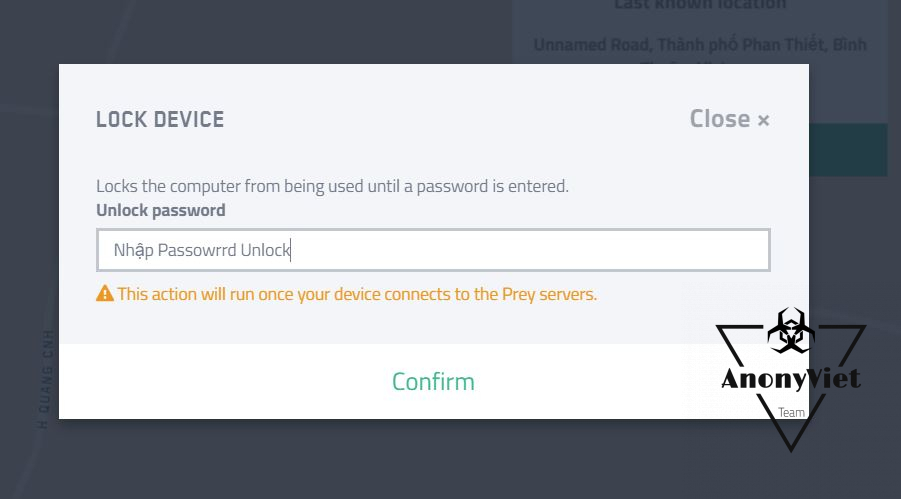
- Lock device: Lock the device with an extremely high security system and if you enter the wrong password, it will capture the screen and email it to you. (just activate and set the password the machine will automatically lock).
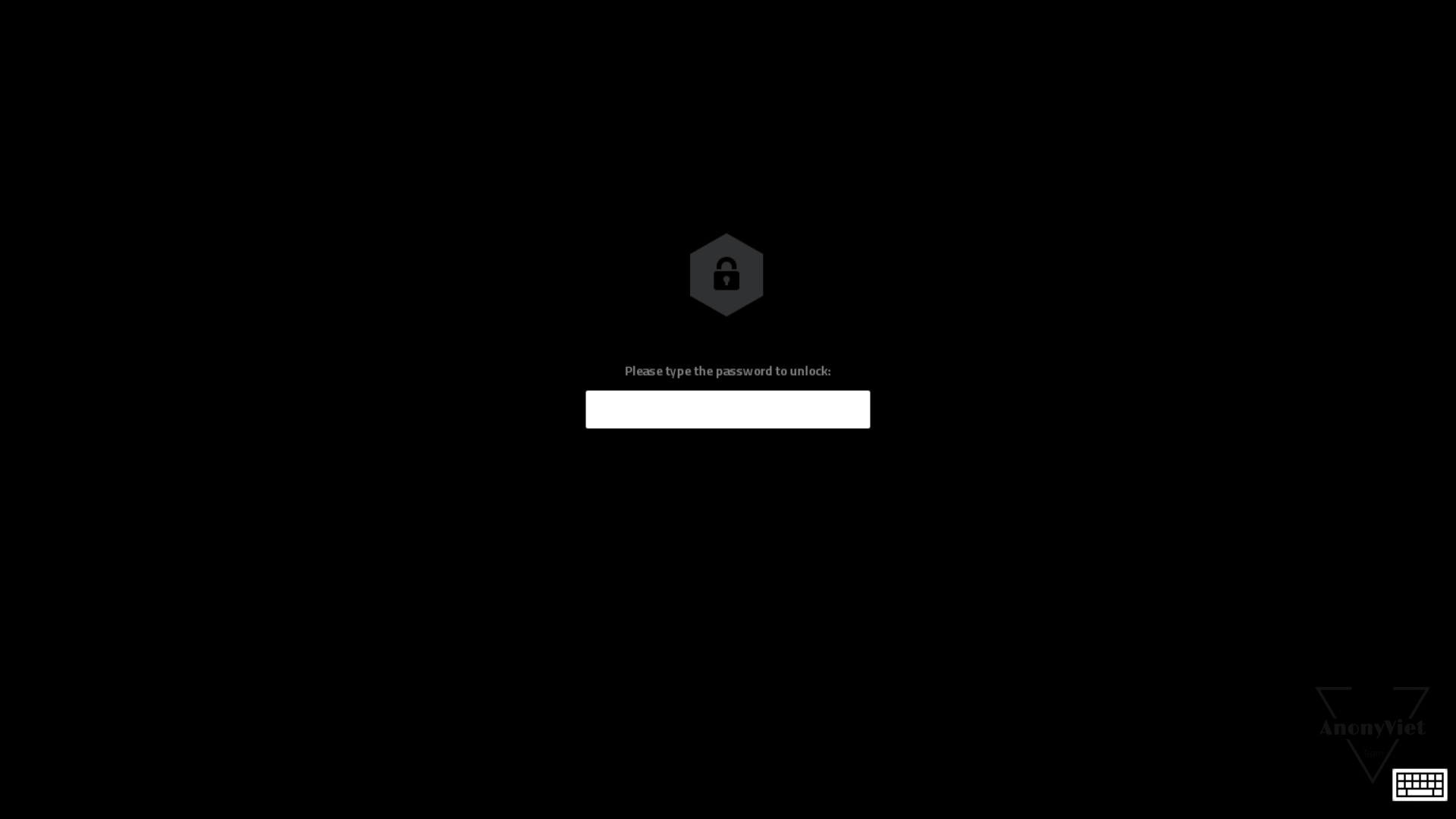
Screen after locked
As for the toolbar on the left, readers will surely understand! It’s easy
Download Link:
-
If the instructions with pictures are difficult to understand, you can watch video tutorial below!
Good luck !
Author: Lmint