Abusing the way Office 365 Outlook allows file attachments on the Cloud to disguise malicious code as a harmless file. In this article, we will explore how to abuse the Cloud file attachment feature Office 365 to make the executable (or any other file type) appear as a harmless attachment.
| Join the channel Telegram belong to AnonyViet ???? Link ???? |
File attachment method
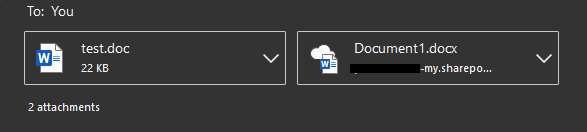
Office 365 allows you to upload attachments in one of two ways:
- Direct Attachments – Traditional way of uploading files. Severe restrictions on allowed file types.
- Cloud Attachments – Attach files available on the Cloud (OneDrive/SharePoint). File types are not restricted.
The image below shows how attachments appear to target users. The difference between these 2 types of attachments is the icon and link of the Cloud attachment below
We have seen the difference between the two methods above, now we will use the technique of attaching malicious files to the Cloud.
Condition
There are a few things you should do before proceeding:
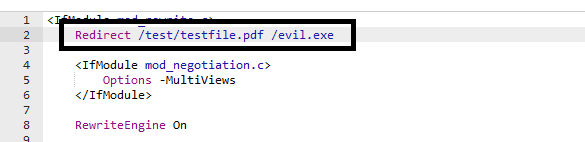
1. Set up the domain and HTTP server. Since Cloud attachments show a partial association, you should create a subdomain like onedrive.microsoft. * To make attachments look less suspicious.
2. Store files on the server
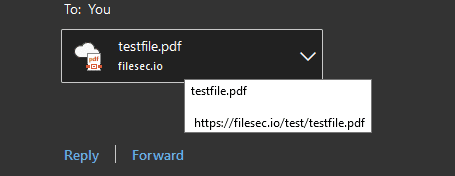
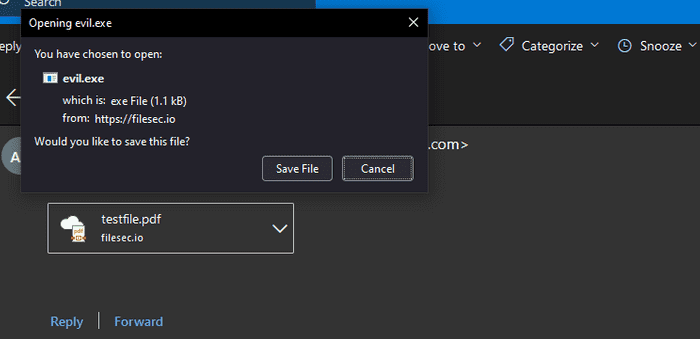
3. Set up HTTP to redirect a path ending with a harmless extension (.txt, .pdf, .docx, etc.) to your malicious executable. This is extremely important because as we will see Office 365 chooses the icon of the attachment based on the file extension of the link. In my case, I will set up a redirect from /test/testfile.pdf to /evil.exe.
Attach malicious files
Compose an email to the victim, click the attachment icon > Browse Cloud Locations.
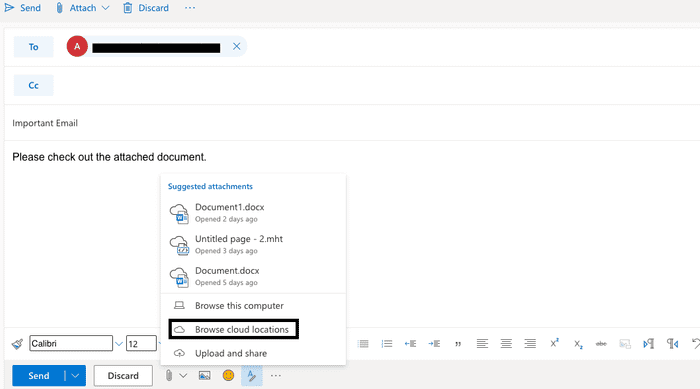
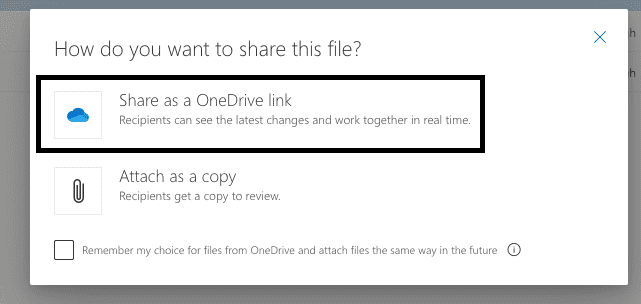
Next, choose any random file to attach. This file can be anything.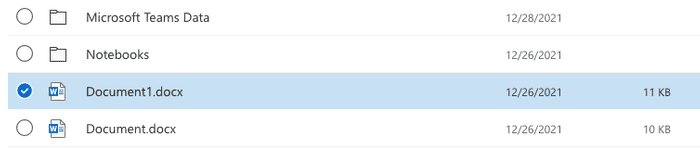
Make sure you select the ‘Share as a OneDrive link’ option. This is the option to attach files as cloud attachments.
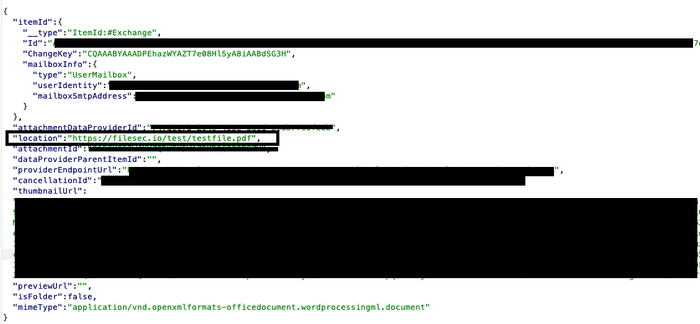
Immediately intercept requests and modify location URLs. Set it as a harmless extension URL that redirects to a malicious file, in this case /test/testfile.pdf.
When the email is sent to the victim, all they see is a PDF attachment and they will have no reason to assume it’s malicious. But when the attachment is clicked, the malicious file is downloaded.
Conclude
This is a really useful technique when trying to gain initial access. An added benefit of using this technique is that the link is not scanned and thus increases the likelihood of the email reaching the victim’s inbox.
In addition, you can also attach the Virus contract to the Word file here.