Hackers always monitor and collect victim information before attacking them. For information stored on websites or computers that cannot be eavesdropped. Hackers will use the support virus to collect information on the victim’s computer.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
You want to gather information faster and more complete, but it doesn’t take long. Then you need to use Tool Hack to help you do this safely and quickly. That’s why today I write this article to share with you Mercury Tool – Hacker’s collection tool.
This program will help you to collect extremely important information of the victim. This information will make it easier to attack them. You can even use the information to threaten someone.
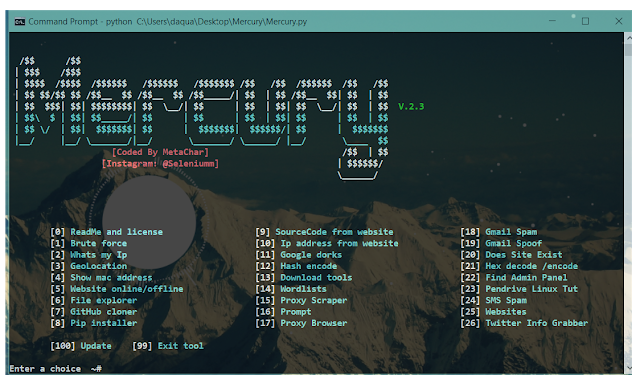
This is the user interface of Mercury Tool
System Requirements
Mercury is an information gathering program written and operated on the Linux kernel operating system. Works well on Linux environments and Linux Distros. Here are the commands to Clone Repo and install the program to use.
apt-get install python2 git clone https://www.github.com/MetaChar/Mercury pip install -r requirements.txt
Features of Mercury
BruteForce
Mercury uses Selenium to autofill password into the website.
GeoLocation
Gelocation allows users to pin the exact location of an IP address.
From there, you can trace the subject’s home address or the area in which the subject lives.
SMS Spam
Spam spam to the victim’s Gmail.
Email Spoof Email
Send anonymous emails to victims.
Check out Website Exist
Mercury checks if the website is real
Check if the site exists or not
Check if the website is online or not. Exist or not?
Encrypt text into Hash
Convert the text you want into a Hash code.
Hex Encode/Decode
Hex encoding and decoding.
What’s Ip & Mac
Displays the Mac address and IP address.
Download Additional Tools
Support downloading 16 more tools like hydra, metasploit and nmap
Github Cloner & Pip Intsaller
Install Pips and Github repos.
Website Cloner
Clone (get) the source code of any website.
IP Address From Website
Check IP address from website.
nmap
Nmap must be pre-installed.
DOS
Dos attack with packets
Anon Webbrowser
Download or post to Chrome with a proxy
Google Dorks
Look for sites that are easy to hack.
Admin Panel
Support tracing the admin page if it is in the victim’s browsing list.
Download Mercury
Good luck
Lmint.