The world of Cybersecurity is divided into two opposing schools, Red Team and Blue Team, one side specializes in protection and the other specializes in attacking. If you are a Hack – Security enthusiast, you can’t ignore a test attack toolkit for Red Team called RedTeam Toolkit. Today I will show you how to use one of the security error scanning tools that I often use! This tool is called RedTeam – toolkit, a tool that Redteam needs to know. Then let’s proceed to learn its functions!
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
RedTeam Toolkit is a collection of tools that make up a piece of software and are deployed on the interface as a Web-App using Django. This toolkit supports a lot of tools for security professionals to learn and discover errors of a software, a Web site or a tool to find security-related errors of the operating system.
This tool has functions including:
- FullScan: Look for security flaws from ports and check for CVEs from the target
- Livehosts: Check the target’s live host
- DirScan: Check the target’s directories
- CVE description: Find information about CVE . errors
- SSH Dictionary Attack
- RDP BruteForce
- WebApps:
- F5 BIG-IP PoC ( CVE-2022-1388 )
- Apache Path Traversal PoC ( CVE-2021-41773 )
- Automatically search for XSS
- Web Crawler
- Extract Target’s SubDomain
- HTTP Verb Tampering
- SQLi (In development)
- Windows:
- Microsoft Exchange ProxyShell PoC (CVE-2021-34523, CVE-2021-34473, CVE-2021-31207)
- Linux: Check for Linux CVEs (Under maintenance at time of writing)
Note: this software only works on linux. In this article, I use Kali Linux 2022.2
Setup Guide
Step 1: You need to download Python3 on your machine. You can download it with the following command
sudo apt-get install python3.x (x là phiên bản mà bạn muốn cài đặt)
In this article I use python3.10.4. If you already have python then check what python version it is. With the Redteam toolkit, python 3.x is required. You can check with the command
python --version hoặc python3 --version (Trong trường hợp trả về lỗi tức là máy bạn hiện đang không có python)
Or you can download the python package here
Step 2: You need to install docker and docker compose, enter the following command to install them
sudo apt install -y docker.io && sudo apt-get install docker-compose-plugin
Step 3: You proceed to install the package files of Redteam Toolkit and run it through docker
git clone https://github.com/signorrayan/RedTeam_toolkit.git && cd RedTeam_toolkit docker-compose up -d --build && docker-compose exec webapp python manage.py createsuperuser #Lưu ý: Sau khi chạy sẽ mất 1 khoảng thời gian chờ khá lâu #Lưu ý 2: khi chạy câu lệnh này, bạn sẽ được hỏi tiến hành tạo tài khoản để đăng nhập thì hãy đặt tên và mật khẩu theo ý thích. Nếu không có thì hãy chạy lại câu lệnh này 1 lần nữa #lưu ý 3: Service của Redteam Toolkit đã được để trong Startup software nên không cần chạy lại lệnh sau khi khởi động lại
Instructions for accessing Redteam Toolkit
Step 1: You can access through your browser. In the address bar you enter 127.0.0.1:4334

Step 2: You proceed to log in through the account and password you just created at Step 3 part setup. You click Login > Enter your account and password > login
 Instructions for using Redteam Toolkit
Instructions for using Redteam Toolkit
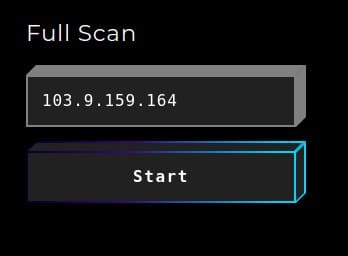
Step 1: You access the Full Scan section

Step 2: You enter the hostname or ip address of the target and wait for a while. Please note this process is fast or long depending on your home network
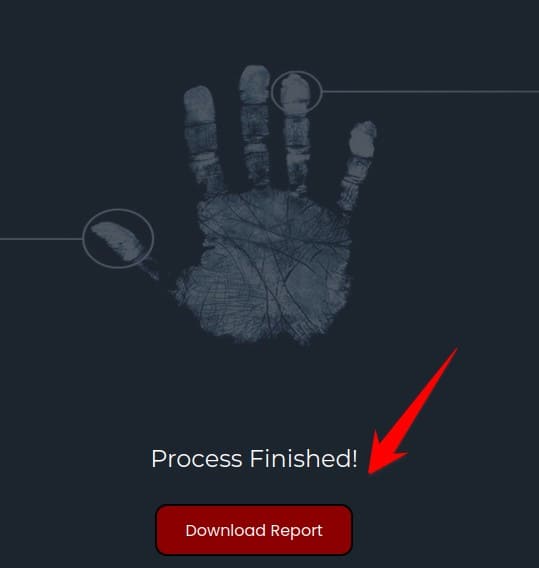
Step 3: After a period of time it will finish and allow you to export the file as a PDF. You click Download Report to proceed to download the report file about your goal
And below are the results reported by Redteam Toolkit. As you can see here shows the things that it has fully scanned on the target. The returned results include error codes CVEs too
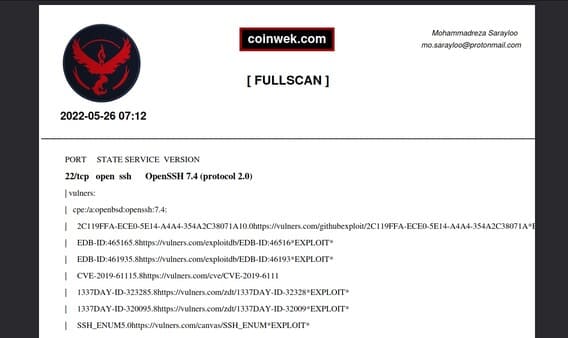
Below is a Demo of the entire process of Full Scan

Maybe you also want to read: How to install Nuclei to scan Website security holes











