Cyber Security is supposed to be a very difficult subject to learn, but I’ll show you that anyone from any field can learn it, including you! This article will help you get started in the security field on the most standard route.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |

Cyberspace is the fastest growing industry in most sectors in the world. Growing awareness of well-known cyberattacks has resulted in recruiters scrambling to find candidates, often to create security departments that weren’t available before. This has created a huge gap in information security, where unemployment is close to zero (not in Vietnam :v) making this one of the best times to enter the industry. As a newbie, you will find that the InfoSec community is great, especially if you are self-taught and ready to learn and explore. Throughout this article, I’ll break down how to get started and where you can go in this field.
Know where to start
The journey to learning cybersecurity is not too difficult, however, it is often a bit overwhelming for many newbies. Information security is a vast field with a lot of knowledge. Hacking is really a brain game, you have to learn each area of knowledge. One thing you need to know is that this process does not involve learning and mastering knowledge, rather, it is just a process of summarizing and “knowing what can happen”.
To hack something, you first need to understand how and why it works; Understanding the fundamentals is really important.
TryHackMe is a great place to start and can easily accelerate your learning through the available learning paths.
Each learning path uses a guided approach to learning cybersecurity and includes hands-on and lab exercises, along with video instruction. You’ll get the complete beginner’s route, learning the basics of linux, networking, and programming until you hack your first machine.

Next you will be given a choice between 2 paths of offense and defense, you will discover the skills needed to enter penetration testing or SOC Operator/defensive roles in the industry.

Looking for a sample of it all while just trying out the site with free content? Check out the awesome free path. You can check out that blog post here! Link
Once you’ve got the basics down, I recommend posting blog posts about your experience or a particularly interesting topic you’ve learned. Blog posts are a great way to consolidate knowledge and refer back to it in the future if forgotten.
Those articles can greatly benefit you during the interview process, allowing interviewers to get a glimpse of your expertise. In addition, such articles can demonstrate writing and reporting skills, a very important skill in InfoSec.
Last but certainly not least, real-world challenges can be a great test of the skills you’ve learned. The challenges on TryHackMe are varied, from virtual machines that are hard to hack to digital forensics puzzles to keep you thinking. Similar to blog posts, reporting on these challenges can showcase your critical thinking skills. Once you complete the challenge, showing off your skills and giving back to the community is a great way to develop yourself and land in interviews.
Fields in Cybersecurity
Cybersecurity encompasses many sub-sections, from attack to defense and much more. Let’s break down some of the areas where you can research:
Penetration testing – Pentesters are usually responsible for performing penetration tests on protected systems. Unlike red teamers, pentesters usually don’t care about getting caught, instead, they try to find as many problems and vulnerabilities to attack the system as possible. The general requirements of this array include: basic knowledge of programming (you can learn these languages), basic pentesting skills and critical thinking.
Red Team – Often confused with penetration testing, the red team takes on the role of attacking the system. These people often simulate APTs, threats and risks when the system is attacked. However, the red team often becomes the blue team’s clue because their role is to train the skills to recognize and act appropriately in the face of APT. General requirements include: Strong programming skills, malware development, penetration testing knowledge, etc. The people on the red team have an extremely diverse and specialized skill set to suit the environment. the school in which they operate. People in red teams usually start out as penetration testers.
SOC Operator – Similar to the DFIR role (see below), SOC, Systems Operations Center, Operator is a fortified defensive position. SOC operators use SIEM and various environmental monitoring systems. Have you ever watched a spy thriller where one of the supporting characters watched a giant screen containing everything? The job of the SOC is often like that. General requirements include: basic programming knowledge, basic knowledge of attack patterns, and some light handling skills.
DFIR – That is, digital forensics and incident response (Digital Forensics and Incident Response). Take this as your chance to become Sherlock Holmes. Traditionally, DFIR’s work is done after an attack has occurred, they work to decrypt malware or clean up a business that has been ransomed. General requirements include: basic knowledge of programming, basic knowledge of threat agents, and the ability to work under pressure.
Cybersecurity job
The gap in cybersecurity skills is growing every year, and the demand for personnel has never cooled down. I have collected a few sample job postings that you can refer to below.
Vacancy 1: Pentester
Usually, candidates who meet all of the listed requirements will be deemed overqualified and unsuitable for the current position simply because the company will not have enough budget to pay for the capacity. your. For example: if you want to hire a chef for a restaurant, will you hire a normal chef or a 5-star chef? I will break down the requirements as follows:
- Security expertise in at least one of the following areas…. – this means you already have experience in the areas listed.
- A good understanding of system-level security concepts and best practices – This is a great example of a more specialized pentester position, where the work environment is more closely linked to systems.
- Code Testing Skills – Requires you to feel comfortable reading code and recognize problems in it.
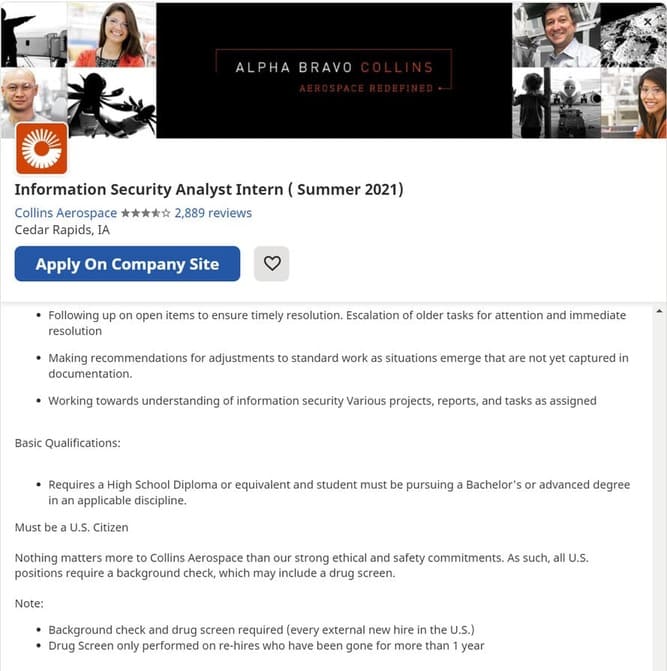
Vacancy 2: Security Intern
The requirements are quite basic and usually suitable for those who want to find a part-time job while studying. Because this position does not need highly specialized people, the employer will not ask too much of you. You just need to know the basics of defense and attack.
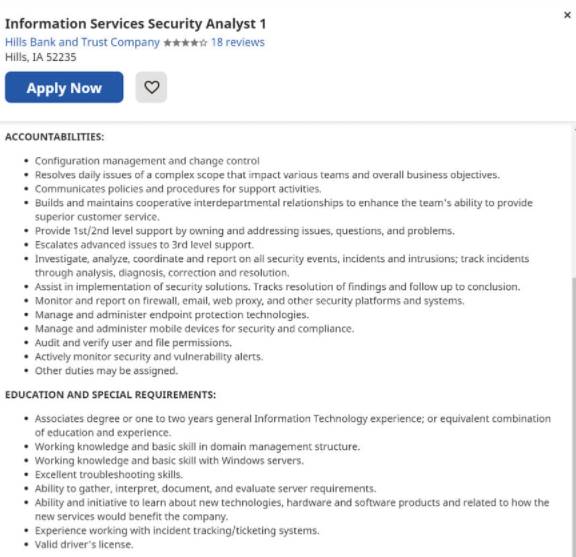
Posted position 3: SOC operator
Last but certainly not least, the SOC location. This is what is generally considered required by SOC or NOC applicants. There are some confusing requirements here:
- Configuration management and change control – get comfortable with tweaking security appliance configurations (firewalls, the like)
- Communicate policies and procedures for support activities – Strong communication skills with the ability to break down complex topics into actionable items
- Provide 1/2 level support by owning and resolving issues, questions and issues – Troubleshoot and provide support from basic questions to complex security issues than
- Test and verify user and file permissions – Knowledge of best practices and the ability to recognize places where user permissions may not be implemented correctly
Cybersecurity salary
In addition to being an educationally rewarding field, cybersecurity can also be incredibly beneficial financially. Here is an example of the average earnings per position. Note, your salary may vary, however, this is the average salary of people in this field.
- Cybersecurity Analyst (Think SOC Operator) – $98,987 USD1/year
- Penetration tester – $118,174 USD/year
- Security Engineer – $107,993/year
In Vietnam it is much lower, you can see the report of TopDev here.
Certificate in Cybersecurity
All in all, certifications can be a complicated subject as their value can vary from employer to employer. In general, a certificate represents the experience you have.
While there are many different certification bodies, the two most recognized by employers are CompTIA and Offensive Security (OffSec) with some of the most popular and valuable certifications being Security+ and Offensive Security Certified. Professional (OSCP). That said, certifications vary from employer to employer and you should ask your predecessors what companies look for in their employees. Also, you should research the certifications you want to study and read the reviews accordingly.
Conclusion
Cybersecurity is an incredibly rewarding field and now is one of the best times to get into it. Online training enhancement sites like TryHackMe make learning fun and easy.