Shifting left is an evolving principle that states that security should move from the right (or end) of the software programming life cycle (SDLC) to the left (beginning). In other words, security should be designed and integrated into all stages of the development process. This new change requires developers to take ownership of security and understand security principles. The good news is that there are many tools available to help developers with this process.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
In this article, we’ll break Application Security into key areas and explore some of the free and open source solutions that help developers and organizations ensure every stage of SLDC, these changes help them improve the overall quality and security of their software.
Shifting left is like adding extra work to a developer’s software, but in reality it allows developers to learn more about security practices, which reduces debugging time and takes a bit more time. More time to build great apps.
Application security during software programming
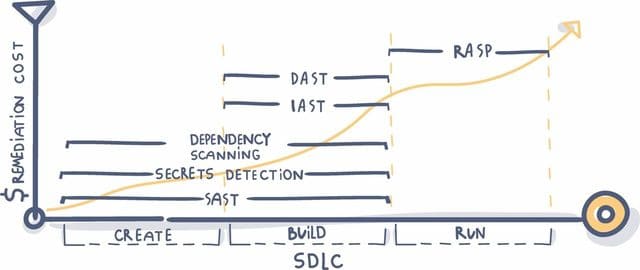
The most important thing is that you must realize that all application security vulnerabilities cannot be fixed by a single piece of software. Successful security requires a layered approach with multiple lines of defense for the different stages of SDLC.
The tools we will learn about include:
- SAST – Static Application Security Testing
- DAST – Dynamic Application Security Testing (Dynamic Application Security Testing)
- IAST Integrated Application Security Testing (Integrated Application Security Testing)
- RASP – Run-time Application Self Protection
- Dependency Scanning
- Secrets Detection
While it is true that vulnerabilities selected for early testing are cheaper and easier to fix, you cannot find all vulnerabilities in the early stages of development. Security needs to be spread out and taken care of throughout the SDLC process.
SAST
Static Application System Testing – also known as “white box testing”, is the earliest and most common type of automated application security. SAST scans the application’s source code for any known vulnerabilities. Since SAST does not require the application to compile or run when finding vulnerabilities (unlike DAST), it was implemented very early in SDLC.
It also implements coding guidelines and standards without executing the underlying code. This app testing portfolio has a lot of solutions available, so when deciding to use one, make sure it’s supported and regularly updated. Here are some of the best free SAST tools.
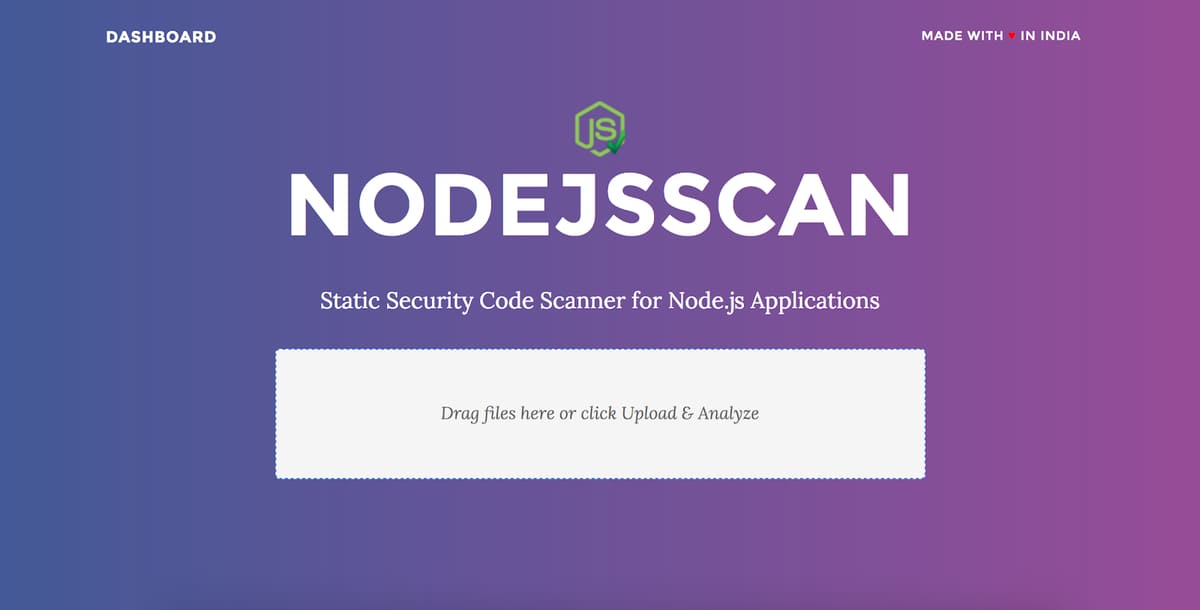
NodeJsScan
NodeJsScan has a command line interface for easy integration with DevSecOps CI/CD pipelines and generates the results in JSON.
A configuration file is available for each language that can be modified for search. An overview of the files, as well as the entire codebase, can be displayed through statistics and pie charts. The program can detect buffer overflows and errors in Java code that may contain OWASP security risks.
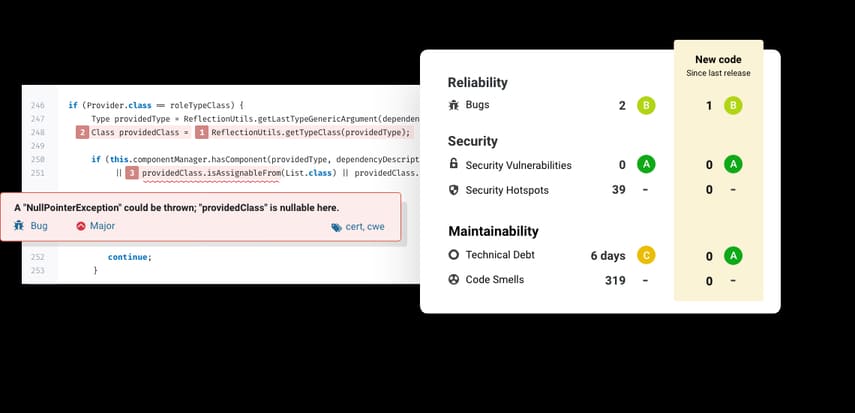
SonarQube
Considered one of the best automated code review tools available in the market. SonarQube has thousands of automatic Static Code Analysis (Static Code Analysis) rules. SonarQube also supports 27 modern and outdated languages (old-fashioned but still has a lot of value) so that SonarQube can cover your entire project and its development.
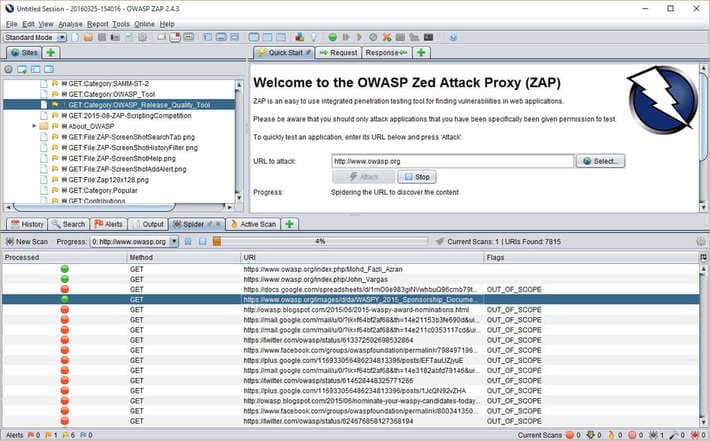
Dynamic Application Security Testing – Also known as “black box testing”. This technique does not find vulnerabilities in the source code like SAST, but rather finds vulnerabilities while the application is running. It does this using injection techniques on the application. DAST can identify common security vulnerabilities, such as SQL injection and XSS. DAST also addresses issues such as runtimes that cannot be determined by static analysis, server configuration and authentication issues, and vulnerabilities that are only visible when the user is logged in.
OWASP ZAP
OWASP ZAP is a free, open source DAST tool that is fully featured, including automatic vulnerability scanning and tools to support manual web-app pentesting. ZAP has a large list of vulnerabilities that it can exploit or identify.
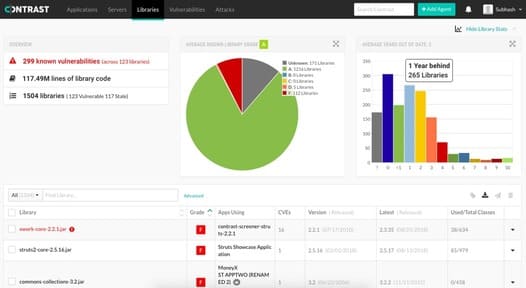
Interactive Application Security Testing – Also known as “grey box testing”, is a technology that combines elements of both SAST and DAST. It is often deployed as an agent during the test runtime (e.g. a device for the Java virtual machine[JVM] or .NET CLR) to observe activity or attacks and identify vulnerabilities.
Contrast is the first product for developers who have the ability to dig deeper into vulnerabilities without knowing the application’s runtime context such as controllers, application logic, data layers, modes view, user libraries, source code components, and application servers.
Runtime Application Self Protection – configured on a server and will start when the application runs. It is designed to detect attacks on an application in real time. Once the application starts running, RASP can protect the application from malicious input or behavior by analyzing both the application’s behavior and the context of that behavior. By using the app to continuously monitor its own behavior, attacks can be instantly identified and mitigated without the need for human intervention.
Square
Sqreen Runtime Application Self-Protection identifies attacks that exploit vulnerabilities in the product by taking full advantage of the context of requests.
Sqreen covers all top 10 OWASP vulnerabilities such as SQL injection, XSS and SSRF. What makes Sqreen so powerful is its ability to leverage the execution logic of requests to block attacks with a much lower failure rate than other existing solutions. Sqreen can also adapt to your specific application-specific stack, so you don’t have to redeploy and configure while your app is set up simply and quickly.
Denpendency Scanning helps you automatically find vulnerabilities while you are developing and testing your application, for example when your application is using a vulnerable (open source) library.
Snyk
Synk is the developer’s first organization with the best maintained open source solutions for developers. Synk provides cost-effective enterprise solutions available to larger organizations.
Snyk has a bunch of great features that make security a part of development like the ability to detect vulnerabilities from within your IDE and scan navigative git to check out projects in the repository your. Snyk also provides a security portal to prevent new vulnerabilities from passing through the build process, and the product environment to check your runtime environment to ensure that existing vulnerabilities are not exposed.
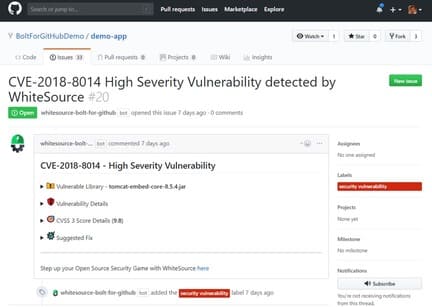
WhiteSource Bolt for GitHub
WhiteSource like Snyk also has some great free tools for developers as well as enterprise solutions for large organizations. WhiteSource Bolt for Github is a free application that continuously scans your repos, detecting vulnerabilities of components in the source code and providing fixes. It supports private repositories and public repositories.
More than 200 programming languages are supported and continuously monitored from many open source vulnerability databases such as NVD.
Secrets like API keys, database credentials, and security certificates are the jewels of organizations as it can provide access to sensitive systems.Secrets detection can scan source code , logs and other files to keep finding other secrets. This is a special service because most secrets are usually always high entropy sequences (strings designed to appear random), but most high entropy sequences are not secrets, so they are very difficult to obtain. was discovered. It requires advanced classification algorithms to detect secrets with a high degree of accuracy and recall.
Secrets detection is often confused with SAST because both scan source code. But unlike SAST, which concerns only the current version of the application, Secrets detection concerns all versions of the project. Version control systems, like git, will track and store all changes to a project. If previous versions of the source code contained hardcoded secrets inside, which were removed in the final stage, code review and tools like SAST would miss these secrets, so it could may be in a git repository and be compromised. This is why Secrets detection is different from SAST.
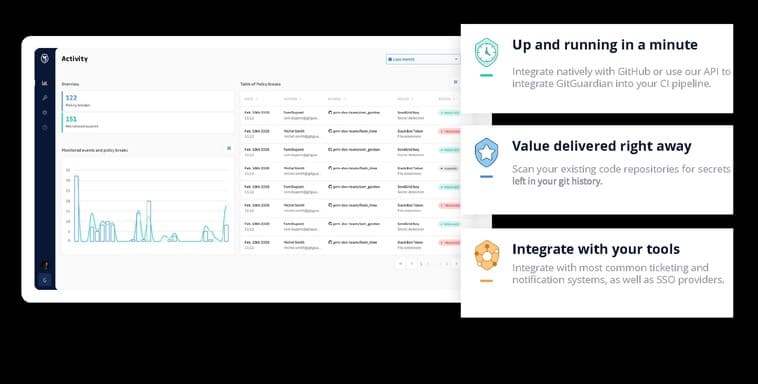
GitGuardian
GitGuardian’s technology works by scanning developer repositories for evidence of sensitive data.
GitGuardian includes more than 300 different types of sensitive data from database connection keys, SSL certificates, to usernames and passwords. These data are discovered through a combination of algorithms, including sophisticated pattern matching techniques. GitGuardian can be integrated with your Github account and configured within minutes, so developers can use the GitGuardian API to detect data in any service, including in directories, applications. using email or a Slack channel.
summary
With so many solutions available, you may find it difficult to decide which tool to choose from in this article. But remember, always consider the use of each tool to fit your current workflow because even great tools can become useless if they are too difficult to use.
Every application is different, and the tools outlined above should be considered the bare minimum of protection, if you and your organization may not need more detailed solutions. Security is one of the most prized skills for developers, and while security may seem like a daunting task, it’s a worthwhile investment to understand and implement. these systems throughout the entire application development lifecycle.