A virtual private network or VPN is an encrypted connection that protects your internet connection and your privacy online. It does so by creating an encrypted tunnel and then transmitting your data. While using a VPN service, it will hide your real IP address and keep you safe on public networks.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
Typically, VPN technology is used to establish a private network over the internet to share the resources of the corporate intranet with remote users and other corporate locations. People can also use a VPN to access their home network remotely.
A VPN is like your own private lounge on the Internet, where you can hang out without anyone taking a seat :v. They allow access to your home network or your company’s corporate network even when you are in another part of the world.
Popular VPN Service
NordVPN and Private Internet Access, all of these VPNs are popular in QoS and security, providing private connections.
Cyber Ghost, Surf Easy, Tunnel Bear are some of the free VPN services you can use if you want to save money. But because it’s free, there will be little features, download limits or ads. Also, these free services can’t beat the paid ones.
How does a VPN work?
However, the working principle of Virtual Priavate Network (VPN) is not a complicated matter. You need to understand the following concepts:
SSL (Secure Sockets Layer) / TLS (Transport Layer Security): It uses 3-way handshake to ensure proper authentication between client and server. A cryptographic-based authentication process in which certificates, which act as cryptographic keys that have been stored on the client and server side, are used to connect.
IPSec (IP Security): This protocol can operate in transport mode or tunnel mode so that it can do the job of securing Virtual Network connection. The two modes differ in that the transport mode only encodes the payload in the data, i.e. only the message is present in the data. On the other hand, tunnel mode encrypts all transmitted data.
PPTP (Point-To-Point Transfer Protocol): It connects users in some remote location to a private server in the VPN network and also uses tunnel mode for its operations. Low maintenance and simple working make PPTP a widely accepted VPN protocol.
L2TP (Layer Two Tunnelling Protocol): It facilitates the transmission of data between two geographical locations over a VPN network, often used in combination with the IPSec protocol, further supporting the security layer of the communication.
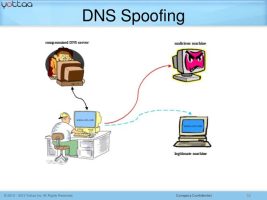
You now have a rough understanding of the different protocols used in VPNs. We’ll find out how they work. When you connect to a public network, such as the free WiFi network at airports, all your data is flowing through a large tunnel along with the data of other users.
Anyone who wants to spy on you can easily sniff your data packets in the network. When a VPN comes along, it gives you a secret tunnel inside that big tunnel. In other words, all your data will be encrypted so that no one can exploit it.
Why do you need a VPN service?
Surfing the web or making Online payments on an unsecured network means that your personal information may be exposed. Therefore, to be safe, a VPN should be a must for everyone who wants to keep their information secure.
For example, if you are in a public place and use WiFi, you risk exposing your sensitive information while surfing the internet. Users on the same network can access any data transmitted over that network.
By using a VPN, your data is always encrypted and anonymous.
How a VPN Protects You Online
As explained above, a VPN encrypts your data so that you can stay anonymous from any trackers or eavesdroppers while connecting to the Internet. By using a VPN, no one can access what you do on public and home networks.
Encryption is the best way to stay anonymous on the Internet, and data security is also a big concern.
Setting up a VPN connection involves three stages
Accuracy: In this step, the first data packets will be encapsulated, basically the data is wrapped inside another packet along with some headers and other things attached. Doing so is to conceal the identity of the data packets. Now, your device initiates the connection by sending a Hello request to the VPN server, which will respond with confirmation and request credentials to verify the user’s authenticity.
Tunnel: After the authentication phase is complete, a tunnel is created to provide a direct connection through the internet. We can send any data we want through that tunnel.
Encode: After successfully creating the tunnel, it can transfer any information we want, but that information is still not safe if we use a free VPN service. That’s because other people use it too. So, we encrypt data packets before sending them through the tunnel, thus preventing any other users from peeking into those data packets. They will only see some unrecognizable junk data passing through the tunnel.
Now, if you want to access a website, your device will send an access request to the VPN server, which will then forward the request to the website using the VPN’s identity and receive the data as well. so. The VPN then transmits this data to your device. Here, the website will think that the VPN server is the user. It will not find your trace or device as a real user unless you transmit some personal information over the connection. For example, your identity will be revealed if you visit a social networking site like Facebook or Twitter using a VPN connection.
Uses of VPN: What is the function of a VPN?
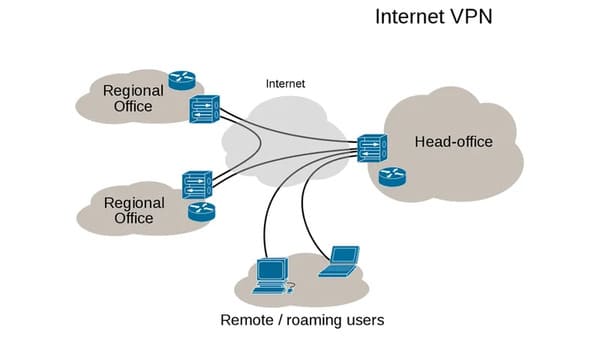
A VPN connection provides direct access to the corporate network for users who are not within the physical coverage of the network. Logically, the remote user is connected like a regular user sitting in the company.
It is also used to provide a uniform network environment for an enterprise company with office locations around the world.
Other uses of a VPN include accessing services on the internet that are not available in a particular country or region, accessing censored content, or if the user simply wants to remain anonymous on the web.
VPN on Android and iOS
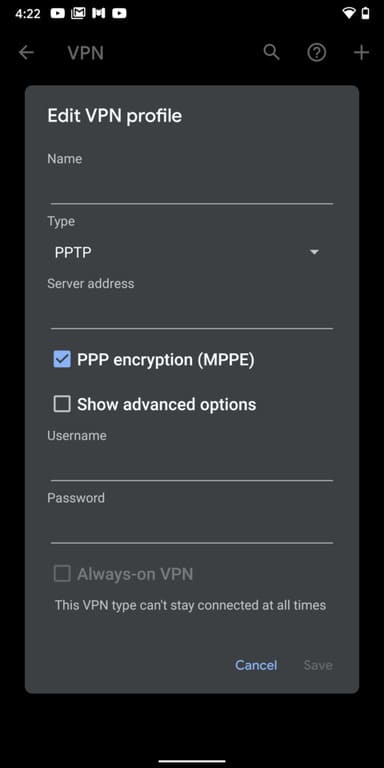
You can also set up a VPN connection on your Android phone. It allows you to access your company’s private network right on your Android device. A VPN also allows network administrators to control your device, add or remove data, and monitor your usage.
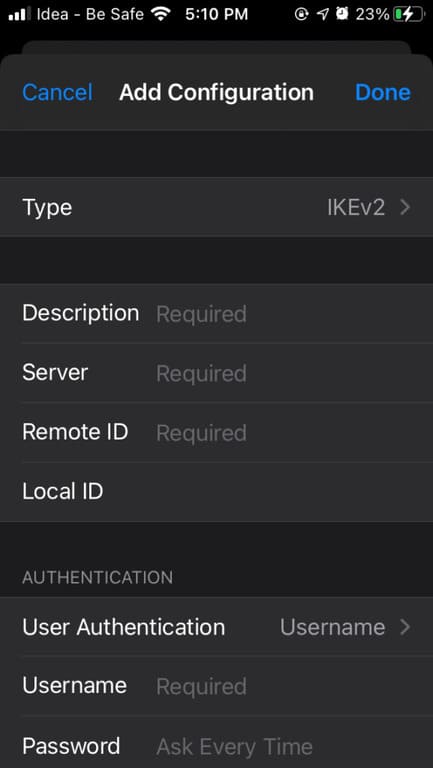
Likewise, Apple devices including iPhone (iOS) and iPad (iPadOS) have built-in support for VPN. You can go to the Settings app and create a new VPN profile using the credentials provided by the VPN.
Types of VPNs
There are basically two types of VPNs, namely Remote Access Virtual Network and Site-to-Site VPN. The second type, site-to-site VPN, comes in many more varieties.
VPN Remote Access (VPN Remote Access)
This VPN will give someone access to an existing private network over the internet. A private network can be a network set up by several corporate organizations equipped with databases and networking hardware related to the organization or any of their projects.
There’s a remote access VPN, so employees don’t need to connect directly to the company’s network. They can do so with the help of the necessary VPN software and authentication data provided by the company.
Remote access VPNs aren’t just for the corporate sector; Home users can also use them. For example, you can set up a virtual private network at your home and use the credentials to access it from somewhere else. This way, the websites you visit will see the IP address of your home network, not your actual IP address.
Furthermore, most of the VPN services you see on the market are remote access VPNs. These services mainly help people to remove geo-restrictions on the internet. These restrictions could be due to government blocking or if a website or service is not accessible in a particular area.
VPN Site-to-Site
The word ‘site’ in this case refers to the physical location where the private network exists. It is also known as LAN-to-LAN or Router-to-Router VPN. In this type of VPN, two or more private networks in different parts of the world are connected together, all acting as a single virtual private network on the internet. There are currently two types of site-to-site VPNs.
Intranet Site-to-Site VPN
We call it an intranet site-to-site VPN when the various private networks of an organization are linked together over the internet. This type of VPN can share resources across various corporate locations. An alternative would be to place separate cables in different office locations, but that would be difficult to implement and could incur high costs.
The need to connect corporate networks belonging to different organizations. They may be collaborating on a project that involves resources from both organizations. Such virtual private networks are created called site-to-site VPN extranets.
Advantages and disadvantages
The biggest advantage of using a VPN is that it provides a cost effective way to create an individual network compared to renting and setting up a network line.
In addition to the benefits VPN gives us, it also has its weaknesses. Not having a streamlined process to ensure Quality of Service (QoS) over the internet is the biggest weakness of VPN technology. Furthermore, a level of security and authenticity outside of a private network is beyond the reach of VPN technology. And also incompatibility between different vendors.
What you should look for in a VPN
It totally depends on what you actually use the VPN for. Before choosing a provider, ask yourself three questions: How fast is it? Will a VPN keep data safe? Will it respect the user’s privacy? Similarly, these are the key factors that you should look for when choosing a VPN provider.
Alternatively, you can also use a VPN with Tor for extra privacy and security here.