*** Surely among us, many people have heard no less than 1 time the concept of “Keylogger”. Although it can be vaguely perceived as dangerous, a powerful tool can help bad guys steal the information we enter from the keyboard. But can you confidently say that you completely understand this tool?
Let’s take a look at learning about Keyloggger, from which to draw the most effective self-protection experience.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
How does the keylogger penetrate the machine?
A keylogger is usually a small piece of software (a form of covert channel for Trojans) – or sometimes more dangerous even a hardware device – with the ability to record every keystroke the user presses on the keyboard. Combining the results of these keystrokes, the keylogger installer can obtain private messages, email content, credit card numbers and, most dangerously, any type of user password.
In most cases, keyloggers are “silently installed” by malware on users’ computers after successfully infiltrating them. Some other less common cases are when parents want to control the access of their children, when the managers of a company want to check the working attitude of employees or … couples want to monitor each other. . In Vietnam, we sometimes hear about keyloggers lying in the machines of the net stores – not because the machine is infected with malware, but because someone wants to “test their skills”, some people even let them know. that it is the innkeepers who direct this. The truth of the rumors as well as the legitimacy of cases that touch personal privacy – even when parents want to spy on their children is still a matter of debate. But the need to manage employees of large organizations through keyloggers is real, and there are even lines of specialized hardware products for this job.
As mentioned above, most keyloggers on popular computers are distributed through malware. If the user’s computer has been compromised, this piece of malicious code can have the function of a compact keylogger software – or it can act as a Trojan, downloading and installing the keylogger package. silently, even with many other malicious software. Often the malware will also automatically set up a channel to send the information that the keylogger collects to the “owner”. It can be said that keyloggers are one of the most popular tools for hackers because they can obtain all kinds of user information using this method.
In addition to the malware intrusion channel, most of the remaining keylogger infections come from our relatives. The two most easily related subjects, as mentioned earlier, are of course parents and… lovers (or spouses). Parents who feel the need to carefully control their child’s access to the vast Internet of the world often use packages of parental controls, where it’s usually not difficult to find functionality similar to keyloggers. . And of course, in today’s online world, a jealous girl with a little English will take less than 30 minutes for Google to release a keylogger (or even more multifunctional software) to monitor. See if you can sneakily “eat pho” outside.
And in the case of bosses who direct the installation of keyloggers on employees’ machines, it should be remembered that analyzing the results obtained by keyloggers, especially with a large number of machines, is not a small effort and resource. . In most cases, if you find that you are “in the spotlight”, check yourself to see if you have done anything to be placed in the category of “suspect” to disclose information of the company or not. The laws related to this tracking also vary by country and geographic region. At the same time, some companies also require employees not to work personally in an office environment, so such tracking is still considered by some to be legal and reasonable – because, anyway, if you enter individuals on these machines means that the employee himself has violated the regulations, can not blame anyone else.
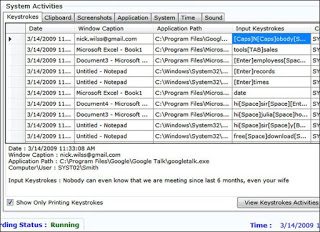
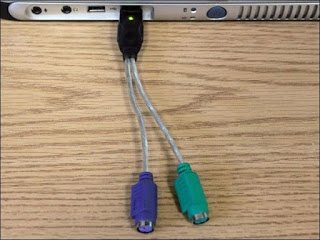
Hardware keylogger (see illustration)
With the advancement of technology today, creating a keylogger in the form of a hardware device is no longer too difficult. As we all know, the PC keyboard is usually connected to the case via a USB cable (or some models still use the PS2 port). Connecting dedicated keylogger hardware is as simple as disconnecting the keyboard from the case, plugging in the compact keylogger device. This device is of course then serialized to the case to ensure that the user can still enter data normally without any detection, especially in some office environments where the case is normally closed. It’s closed and sometimes only IT staff have the key to access. Even in the net shop, or for careless users who never touch the dusty case under their desk, this method is still very effective. With this approach, no security software installed on the computer can help us detect that the input data from the keyboard is being recorded silently, because this device does not notify the operating system. about its presence.
Although usually does not have the advantage of software installed by malware that can send data obtained over the network. But the person who installs the keylogger device just needs to come back for a few days, unplug the device and plug the keyboard back in to have a relatively large amount of user data in hand. The most important thing is that it does not leave any “soft” traces that security software, connection analysis, etc. can detect.
Sometimes, these devices can even be disguised as adapters that look very “gentle” like in the photo above.
How it works
Keylogger in the form of software often runs in the background on the computer, recording every keystroke that the user enters. Sometimes to avoid sending data so often that tracking is “noticed” by the user, these software packages can be designed to send only strings of data that appear useful – such as a string The number “looks” like a credit card code.
To increase efficiency, keyloggers are also often combined with some other type of tracking software, so that an intruder can distinguish the information that the user enters when chatting nonsense from the information entered. while logged in to your online banking account. The first string of characters a user enters after starting a “chat program, email client or online game” is also important – because this is usually the username and password string used to log into that service’s account. .
For cases that need to be “taken care of” more meticulously, the keylogger installer will often have to use a tool to scan through the entire log file to record everything the user has entered during the time being monitored. , from which to filter out information such as Google search content, comment in a certain topic … on the internet. Often, the monitoring software packages provided for parents and offices also include a screen capture utility. Thereby providing full information and evidence of what the “victim” did during the use of the machine.
Protect yourself against keyloggers (see illustration)

At its core, keylogger software has always been classified as malicious code – malware. So we can detect keyloggers on the machine with commonly used scanning tools. Most importantly, choose the right security software – it doesn’t have to be powerful and expensive, it just needs to have a clear name and reputation. Avast, AVG, Avira all have free and effective solutions for general users. If you are not careful, it is possible that the software that assigns “anti-virus” or “anti-malware” that you indiscriminately downloaded from some source on the network is the culprit to install the keylogger on your computer, or more gently. then it will bring tons of bloatware – unwanted software – as well as annoying ads onto the device.
Avoid Keyloggers
first). If you are really worried and unsure about the existence of keyloggers or beyond, the management software installed on your computer by others, it is best to always take advantage of the virtual keyboard function available on the services. banking services, online payment channels or online games. Don’t let a beautiful day after logging into the game be indignant to realize that your character has been “undressed”, while the culprit is not a stranger but the parents…
2). Here is a trick to break “Keylogger” in Windows 10 (Disable KeyLogger on Windows 10)
1. Run CMD with Admin rights
2. Enter the following commands in turn:
sc delete DiagTrack sc delete dmwappushservice echo "" > C:\ProgramData\Microsoft\Diagnosis\ETLLogs\AutoLogger\AutoLogger-Diagtrack-Listener.etl