In fact, this method is just a fake web trick to deceive the victim, but it is performed on BackTrack, so the use will be very simple, BackTrack 5 R3 almost does it from start to finish to help me and I just need to do it. just enter and enter. And if you want to understand how BackTrack works, inbox, I will send documents to read… 🙂
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
That said, you can see how simple it is, first you run Backtrack, boot live or VMware, in my article, I use VMware to test it easily.
First, we must be able to access the facebook page, but in order to enter, we must change the DNS to Google’s DNS to enter. We open the terminal and type the following command to edit DNS
gedit /etc/resolv.conf
You change the IP address line to 8.8.8.8 and save it
Open the browser and test, ok to continue, if not, check the file /etc/resolv.conf because sometimes you forget to save or save failed.
Next, open a new Terminal window and run the command line:
cd /pentest/exploits/set
./set
It will activate the tool panel to hack out as shown in the picture, enter the number 1 and enter (Social-engineer attack)
In the second table, we enter the number 2 and enter (Website attack vector)
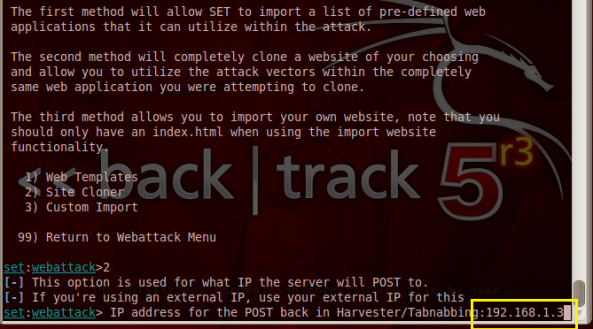
In the third table, we enter the number 4 and enter (Tabnabling Attack methodos)
In the 4th table, we enter the number 2 and enter (Site clonner)
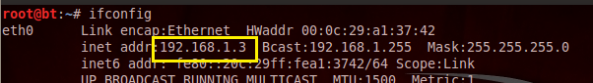
At this point, it will force me to enter the IP address to be a Webserver, I will enter the IP address of the BackTrack machine itself, if you want to know the IP address, you can open another terminal panel and type the command ifconfig let’s see.
Now I will enter the IP address of the BackTrack machine as 192.168.1.3
After entering the IP and enter, it will ask to enter the website address you want to fake, now enterhttp://www.facebook.comit will run a bit like in the picture and show the Enter line, we just need to enter one more time to start the fake web execution process.
I switch to another virtual machine running win 7, run the browser and type in the domain name 192.168.1.3, at this time the facebook login page will appear, I will enter the ID and password to test, email: mrlonely909@yahoo.com, password: mrlonely909. Click login and you’re done
We switch back and forth to the BackTrack device, now we will see the login information the other side has sent here and appear exactly as shown in the picture.
So you understand how it works, the article I guide only runs in the Lan network, if you want to test with other users, you just need to NAT the public IP address to the webserver address (which is the host computer). backtrack) and send the link of that public IP address to the victim.
If you want the victim to be less suspicious, you can find a free domain name with the keyword facebook in it to make the victim less suspicious, point the domain name to your public IP and Nat public IP to the webserver IP is done. You can use it for Gmail or some other similar site.
In the end, the most important is still how you seduce the victim, this depends on each person’s ability…^^
Wishing you success and a new year full of luck, everything is as you wish, and a successful code.
The article is for reference and knowledge sharing, not recommended to do bad things, hope you consider it, thanks.