Chrome is the most used Web browser today, Extensions (extensions) also play an important role in Website attack and testing. Did you know that Hackers often install a lot of Chrome Extensions to serve their hacking purposes.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
Ethical hacking experts from the International Institute for Cybersecurity (IICS) have listed the 11 best extensions to turn your web browser into a powerful hacking tool.
11 Extensions Most Used by Hackers on Chrome
IP ADDRESS AND DOMAIN INFORMATION
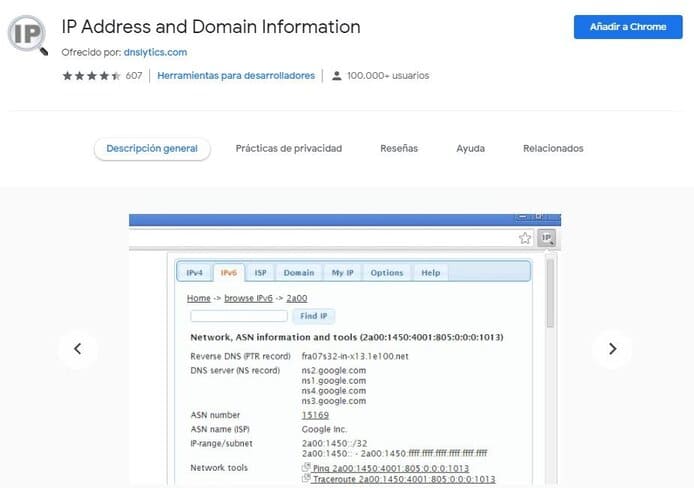
The first stage in any hacking mission is data collection. To do this, TCPIPutils.com will help us get data such as IP address, hosting provider, and other related information.
SHODAN
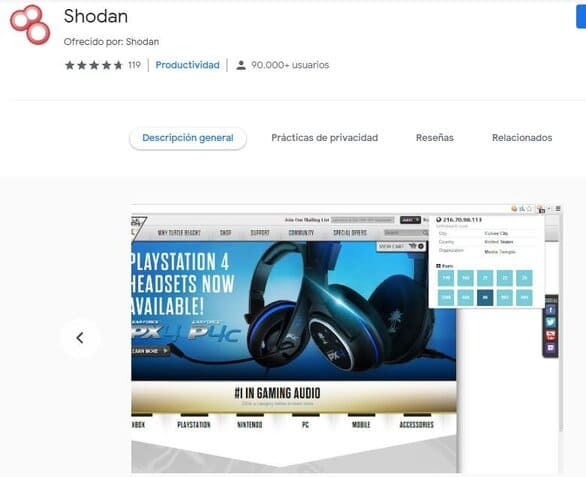
After gathering as much information as possible from the target, Extension used by Hacker followed by search engine Shodan, the tool will show you a list of open ports and services along with other data. You can try the free version of the tool available in Chrome and on the official website.
PORT SCANNER
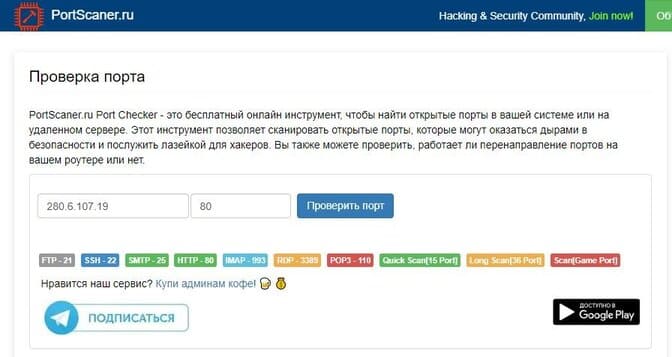
As the name of the utility, Port Scanner will scan open ports on a remote server for their current status. Users can scratch a completely different server, other than manually configuring the TCP port range in this tool.
PROXY SWITCHYOMEGA
Port scanning sometimes doesn’t always go as expected, as many servers have sophisticated firewalls and other attack prevention systems. Anonymous proxies help users prevent intruders from entering your site; one of the best tools for this is Proxy SwitchyOmega (also known as Proxy SwitchySharp) which provides a simple and convenient solution to fend off attackers.
EDITTHISCOOKIE

All websites currently use temporary identifiers (cookies) to track user activity. The developers of EditThisCookie have created a tool for easy cookie management, allowing users to clearly define the tracking purpose of each website.
THE EXPLOIT DATABASE
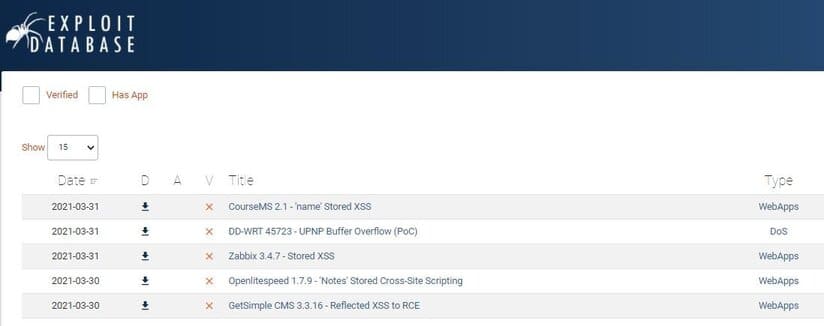
Once the crawl is complete, it’s time to start finding vulnerabilities. This extension provides access to Offensive Security’s mining database. By default, updates are checked every 5 minutes, and all new vulnerabilities are sorted by date, type, author, and description.
GOOGLE HACKING DATABASE (GHDB)
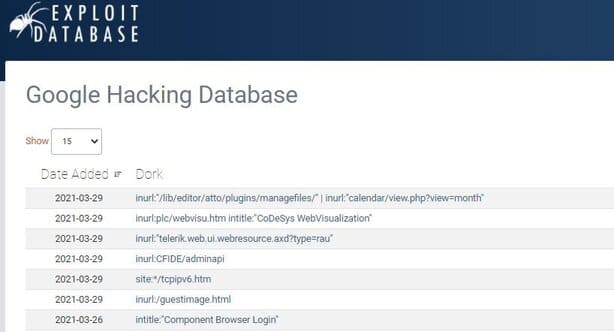
This is a Chrome application that allows you to quickly find network computers and web platforms with known security vulnerabilities through Google.
It has a separate section that covers typical queries for network cameras, video surveillance systems, and printers. In addition, built-in account search features and specific errors are also added.
XSS RAYS

This tool allows ethical hackers to perform penetration testing using cross-site scripting (XSS) attacks, including vulnerability scanners, script analyzers, form injectors, and other tools. reverse translation tool.
This tool can perform advanced keyword searches on HTML pages, scripts and external handlers.
HPP FINDER
This extension will comprehensively evaluate the web page in the current tab looking for items in the web application that are affected by known bugs. HPP Finder uses a method discovered more than 5 years ago, however, the vulnerability found is still in the basic vulnerabilities of RFC3986 so it is still relevant at this time.
REQUEST MAKER
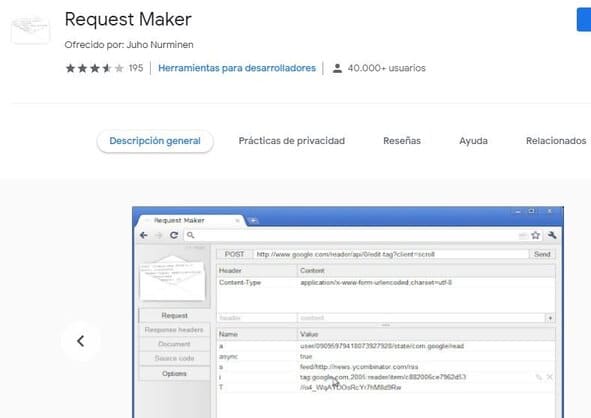
This extension allows you to send normal or modified requests to a specific server to analyze response packets. Request Maker is launched from Add-ons using the Options menu, as well as includes ancillary features.
IMACROS FOR CHROME
This extension saves you time by automating everyday tasks. For example, when performing penetration testing, you often need to repeat the same actions on different pages of your website. Using iMacros, you can record and replay them with default settings, since typical tasks are already in the sample database.
PANIC BUTTON PLUS
It may be time for you to delete all logs of hacking activities on your device, you can do this easily by using the right tool. Panic Button will help you to remove all these profiles with just a few clicks. If at one point you need to delete information, you can specify an easy-to-remember command to prevent other users from stealing your information.