OSINT stands for “open source intelligence”. This concept refers to finding information that you can legally access, through legal means. OSINT is primarily performed online, but it can also be performed offline. Pentesters use OSINT to research their targets, and threat intelligence experts use OSINT to learn about cyber threats. OSINT is an important tool for both red and blue teams.
| Join the channel Telegram belong to AnonyViet 👉 Link 👈 |

Below are some of the most popular tools for OSINT.
10 OSINT tools that hackers need to know
Shodan
Shodan is a search engine for exploitable network devices on the internet, such as servers and IoT devices. Exploitable means publicly accessible. It is possible to place a server, IoT peripheral or network device on the internet and configure it to be relatively private and difficult to fingerprint. But if a device is connected to the Internet without careful security configuration, you can find it through Shodan with the right searches.
Using Shodan without a premium account will return a very limited number of search results. A premium account is a lot more useful if the type of OSINT cyber research you do requires exploring servers, network devices, and IoT peripherals (such as cameras).
Maltego
Maltego runs as a dedicated application for Windows, Mac and Linux desktops, allowing users to access multiple data sources for OSINT, journalistic research and forensics purposes. There are over 58 data sources in Maltego as of this writing, including Google Maps geocoding, AlienVault OTX, ATII Hades Darkweb Intelligence, Blockchain.info, Crowdstrike, VirusTotal, and many others. I hope the number of data sources integrated into Maltego will increase over time.
The value that Maltego provides to researchers is not only in its vast collection of data sources but also in the way its platform can show users data patterns and trends through visual charts Highly customizable. Up to one million entities can be plotted in the chart that Maltego creates.
Of course, you can take advantage of all of Maltego's features but it's not free, although they will let you see a demo before you decide to sign up. But if you don't want to pay, the free Maltego Community Edition can still be very useful.
Google Dorks
Google Dorks is not an app. Rather, it is a technique that uses the Google search engine that everyone uses every day. Don't go looking for the official Google Dorks app, it doesn't exist. But there are developers who have developed open source software tools for Google Dorking that you can try, such as Pagodo and GoogleDorker.
A typical Google Dorking strategy starts by using simple search queries and then moves on to more complex queries. Most people just type strings of text into Google searches, such as “weather forecast” or “abc xyz”. But there are a number of search operators that can be used in Google searches to return more results than you intended. For example, you can try “site:anonyviet.com” to search specifically on your site, or use quotation marks around a search term to return only results that use the search term. look for that exact thing. Google offers a list of tips for refining your Google searches here.
A lot of websites are very poorly configured when it comes to cybersecurity. Google's web crawling bots are most effective on the web when they have access to explore. So, Google Dorking can be a technique to find data such as email addresses, login information, and bank numbers that have not been properly secured.
Recon-ng
Recon-ng is an open source web reconnaissance tool. Its power will be increased by the modules you can install to it. If you use Recon-ng effectively, you can save a lot of time in OSINT research.
Recon-ng can be run from the command line. If you want to make Recon-ng useful for your purposes, select the Marketplace option from the main menu and explore what's available. There are a huge number of modules you can try out, with more being improved and added continuously.
If you're comfortable with the command line and you want OSINT to work much more efficiently, Recon-ng may become one of your favorite tools.
Ahmia.fi
Ahmia.fi is a search engine specifically for finding sites on the Tor Network, although the search engine itself is also accessible on the “clearnet”. But you will need Tor Browser to open your Tor search results.
Many marketplaces and forums are located on the Tor Network, so making effective use of the Ahmia.fi search engine can be a great method for your OSINT forensics work.
Wayback Machine
Where are the old dead websites now? Wayback Machine is a search engine of over 632 billion websites and growing, many originating in the 1990s.
Archive.org is using the Wayback Machine to archive as much of the web as possible. You can also use their website to manually host websites that are currently online. If and when websites and web servers are deleted or taken offline, an archived copy can be found through the Wayback Machine.
I personally found websites archived from 1994 to 2021 through this tool. And what's really cool is that you can often use links in archived sites to go to the archives of those other sites.
theHarvester
theHarvester is another useful open source spy tool that you can install from GitHub. It can be used to get email addresses, servers, subdomains, employee names, and open internet ports from various public sources such as search engines, PGP key servers, and Shodan.
Once Harvester is installed, you can easily run the application from your command line. There is a particularly rich set of options for exploring data in DNS servers. DNS servers have all kinds of information that is very useful because they associate domain names with specific IP addresses.
Some of my favorite data sources you can explore with Harvester include LinkedIn, Bing, Google, and VirusTotal.
TinEye
TinEye is a powerful tool for online image research. If you have an image on your local device, you can upload it to TinEye and see if and how the image is used on other websites.
The most obvious use case is if you have a photo of someone whose identity you don't know and you want to find out who they are. But there are many other use cases, such as “where was this photo taken?” or “what app is this a screenshot of?”
Conversely, if you have the URL of the image on the web, you can conduct research that way as well.
TinEye is also useful for maintaining your privacy. For example, perhaps you should protect your child's privacy. TinEye can notify you if and when your child's photos are shared online.
OSINT Framework
The OSINT Framework is the perfect web application if you're not sure which OSINT data source you'll need to use to find the information you want. So the OSINT Framework presents you with a giant tree of potential data sources that you can explore.
Do you want to analyze malicious files, usernames, geolocations, IP addresses, domains, IRC, Dark Web, metadata, threat intelligence, phone numbers or maybe something else? other? Keep clicking through the chart tree until you find the source you need.
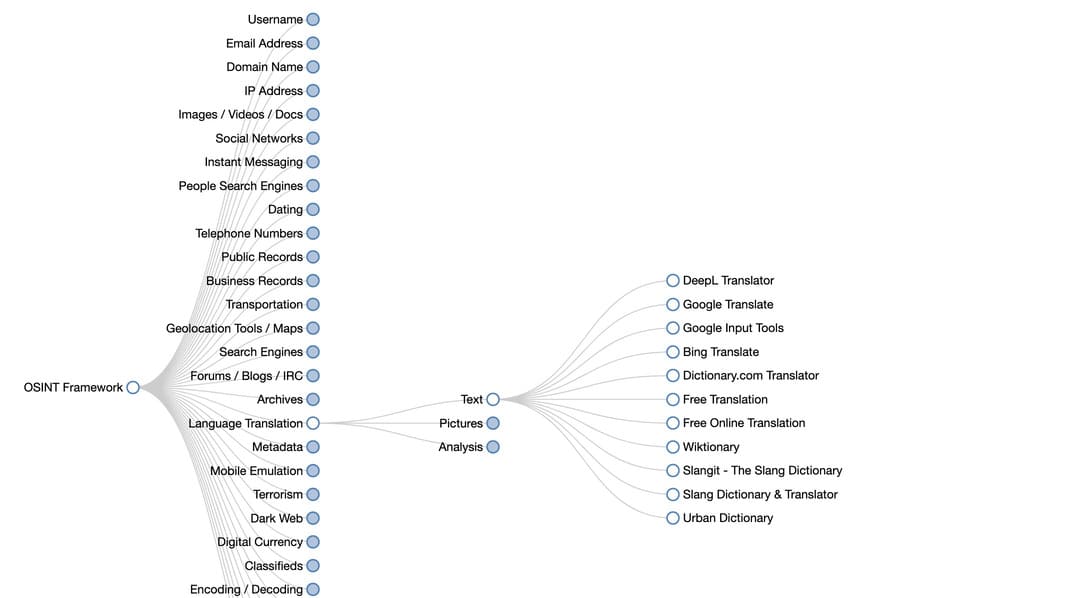
The OSINT Framework can be your first step in the entire OSINT process.