Recently there is a technique to extract Certificates from well-known software to implant in your own software, the purpose of this is to avoid being detected by Antivirus as well as the Windows Defender SmartScreen feature that mistakenly warns as malware. . In this article, I will Demo how to implant the Certificate of Unikey application into the self-built .exe application and check if it works properly.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
This method is spread on Hacker forums, mistakenly aiming to bypass Antivirus. However, in this article, I only guide to research, avoid abuse and violate the law.
Note: The inclusion of the certificate in the App is only a small part of it bypass antivirus, not just having a certificate can bypass it. Today’s antiviruses also recognize behavior, half-encryption…
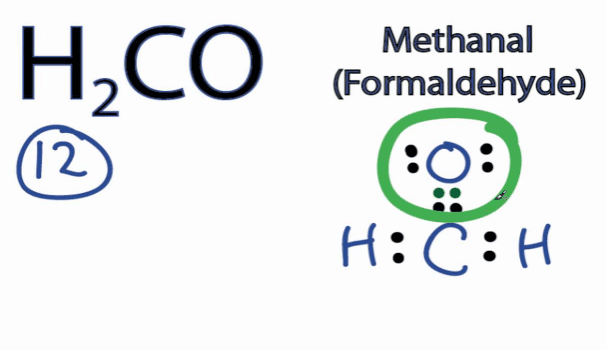
Create executable file with Go Lang
Create a Go Lang file with the function of opening any link. This file is mainly used to test whether it can be executed after the Certificate is implanted.
To do this, you download and install Go Lang on your computer
Open notepad copy the code below and save it as File: anonyviet.goat the directory D:\, so we will have the path D:\anonyviet.go
package main
import (
"fmt"
"log"
"os"
"os/exec"
"runtime"
)
func main() {
baseURL := "https://anonyviet.com/"
if len(os.Args) == 2 {
baseURL = os.Args[1]
}
openBrowser(baseURL)
}
func openBrowser(targetURL string) {
var err error
switch runtime.GOOS {
case "linux":
err = exec.Command("xdg-open", targetURL).Start()
// TODO: "Windows Subsytem for Linux" is also recognized as "linux", but then we need
// err = exec.Command("rundll32.exe", "url.dll,FileProtocolHandler", targetURL).Start()
case "windows":
err = exec.Command("rundll32.exe", "url.dll,FileProtocolHandler", targetURL).Start()
case "darwin":
err = exec.Command("open", targetURL).Start()
default:
err = fmt.Errorf("unsupported platform %v", runtime.GOOS)
}
if err != nil {
log.Fatal(err)
}
}
Open CMD and type the command:
D:\ go build anonyviet.go
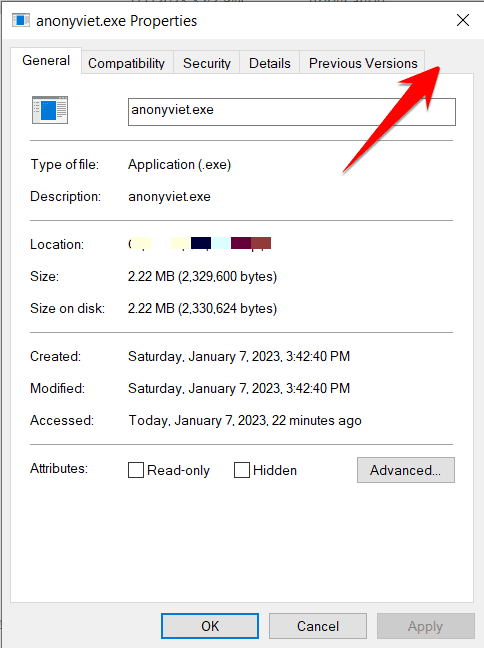
If you see a file in D drive, anonyviet.exe is to create the executable file. Now you right click -> Properties will not see Tab Digital Signatures, because there is no Certificate. You try to execute the file anonyviet.exe See if it shows up on the website.
Import Certificate into Executable File
In this Lab article, I will give an example to extract the Certificate of the software Unikey Pham Kim Long’s file into the newly created anonyviet.exe file above.
On Kali Linux execute the following commands:
git clone https://github.com/anonyvietofficial/Mangle.git cd Mangle go build Mangle.go mv Mangle /usr/local/bin/
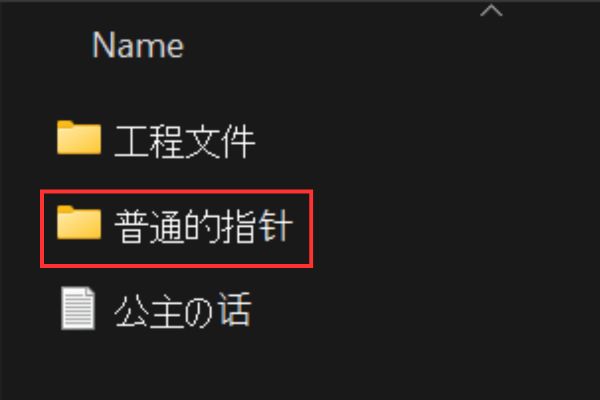
Proceed to Copy files UnikeyNT.exe and anonviet.exe to the Mangle folder.
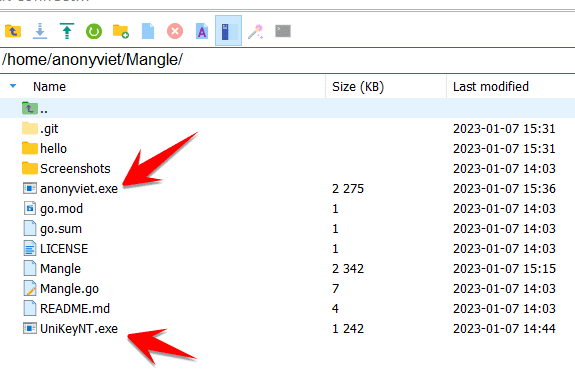
Now we will proceed to extract the Certificate from UnikeyNT.exe luxurious anonyviet.exe and give it a new name anonyviet_ok.exethe command is as follows:
Mangle -C /home/anonyviet/Mangle/UniKeyNT.exe -I anonyviet.exe -O anonyviet_ok.exe
You refer to the following parameters:
- -C: file path to extract Certificate
- -I: path of your executable
- -M: Edit PE file to remove Go . indicators
- -O: set a new file name
- -S: increase file size (in MB)
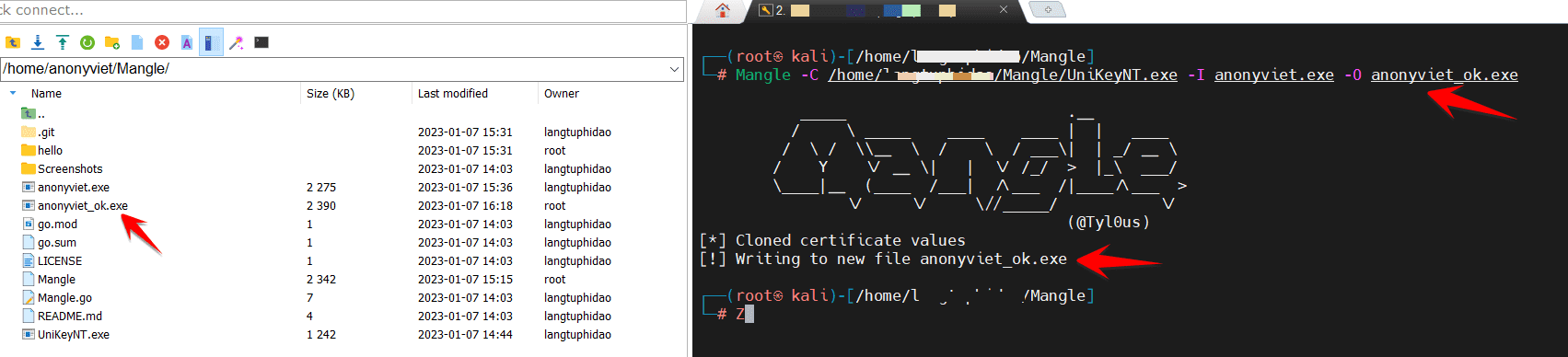
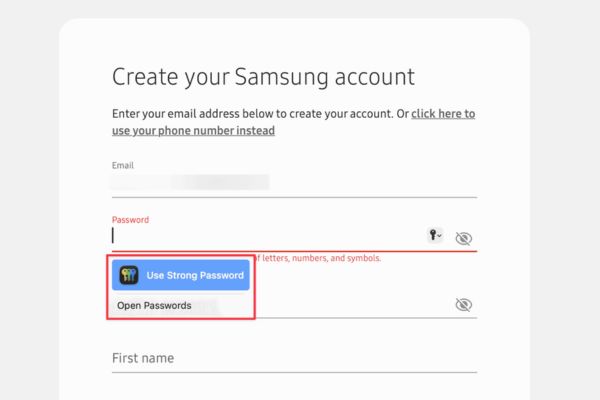
Now you see the file anonyviet_ok.exe has appeared, this is the file that has been implanted with the Certificate of UnikeyNT.exe. Please copy this file to your Windows machine, check in Properties to see if there is a tab Digital Signatures no.
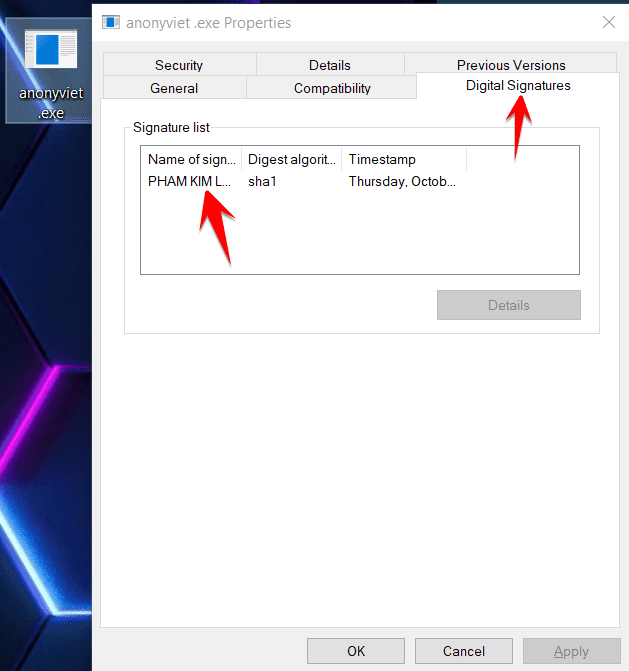
You can double click on the Name of sign to view this certificate information. Now try to execute it, it still runs normally.!
How Mangle works to implant certificates in App
Mangle also has the ability to get the whole chain and all attributes from the code signing certificate from one exe, dll file and copy it to another file. The information includes signing date, access signature and other attributes.
Mangle can delete known Indicators of Compromise (IoC) strings and replace them with random characters, change files by increasing size to avoid EDR, and can copy code signing certificates from legal file. In doing so, Mangle keeps the payloads away from Antivirus.
Currently Magle can only copy Certificates to .exe files built from Go Lang, in the future maybe the author will upgrade to be able to transplant other executable files.
Also you can use some other tools similar to SigThief written in Python is also quite easy to use.