How to track anyone's IP using Canarytokens is a skill you should know if you are interested in cybersecurity. IP is the unique network address of each device connected to the internet, it can reveal a lot of information about the user such as location, operating system, browser, service provider, and even domain name. By monitoring IP, you can detect suspicious activity, prevent attacks, or protect your data.
| Join the channel Telegram belong to AnonyViet 👉 Link 👈 |
In this article, AnonyViet will introduce you how IP tracking with Canarytokens, a free and easy-to-use security tool.
What are Canarytokens?
Canarytokens are digital traps, they work by tracking certain actions, such as someone reading a file, performing a database query, running a process, etc. It's similar like images in emails, but instead of tracking opens, it tracks actions on your system.
You can use Canarytokens to set up these traps in regular computer systems, just like placing alarms throughout the house.
Why should you care about Canarytokens?
Sometimes hackers infiltrate computer networks, and by the time you discover it, it's too late. Canarytokens are a quick solution that helps you know instantly if someone is 'riddled' in your system.
Types of Canarytokens
There are different types of Canarytokens that you can use to track different actions on. Here are some examples:
- Web bug / URL token: Warn when a URL is accessed
- DNS token: Warn when hostname is requiredAWS keys: Warn when using AWS keys
- Azure Login Certificate: Warning when using Azure Service Principal certificate to log in
- Sensitive command token: Warning when running suspicious Windows commands
- Microsoft Word document: Receive notifications when documents are opened in Microsoft Word
- Microsoft Excel document: Get notified when a document is opened in Microsoft Excel
- Kubeconfig token: Warning when using Kubeconfig
- WireGuard VPN: Warning when WireGuard VPN client configuration is used
- Cloned website: Activate a warning when your website is cloned
- QR code: Generate QR code for physical tokens
- MySQL dump: Get notified when the MySQL dump is loaded
- Windows folder: Receive notifications when Windows Folder is found in Windows Explorer
- Log4Shell: Warning when log4j log lines are vulnerable to CVE-2021–44228
- Fast redirect: Warn when a URL is accessed, User is redirected
- Slow redirect: Warning when a URL is accessed, Users are redirected (More information is stolen)
- Custom image web bug: Notify when an image you upload is viewed
- Acrobat Reader PDF document: Get notified when a PDF document is opened in Acrobat Reader
- Custom exe/binary: Gives a warning when an EXE or DLL is executed
- Microsoft SQL Server: Receive notifications when MS SQL Server databases are accessed
- SVN: Warn when someone checks out the SVN repository
- Unique email address: Warning when an email is sent to a unique address
How to track anyone's IP using Canarytokens
To use Canarytokens for IP tracking, you need to follow these steps:
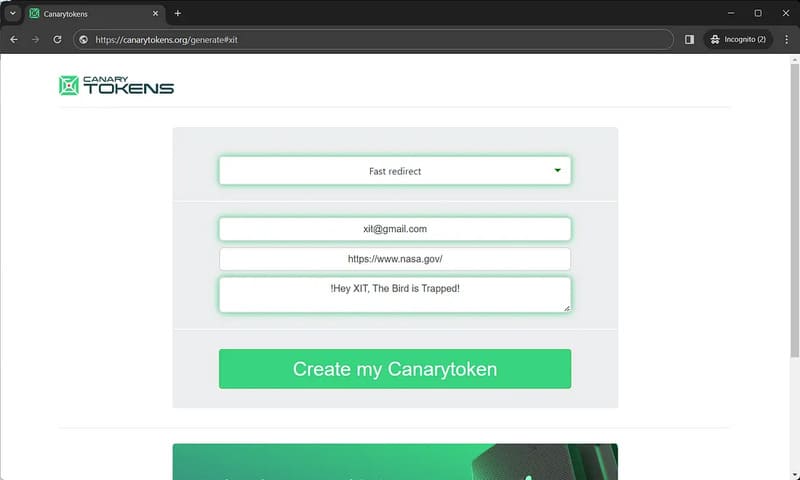
Step 1: Visit website canarytokens.org and choose the type of Canarytoken you want.
Step 2: Enter your email to receive notifications > Paste the URL link
Like creating a secret link that will trigger an alarm if someone interacts with it. In this article, I will use Fast redirect as an example.
Step 3: You then place the generated Canarytoken link in an email, a document, or even an embedded image and send it to the target.
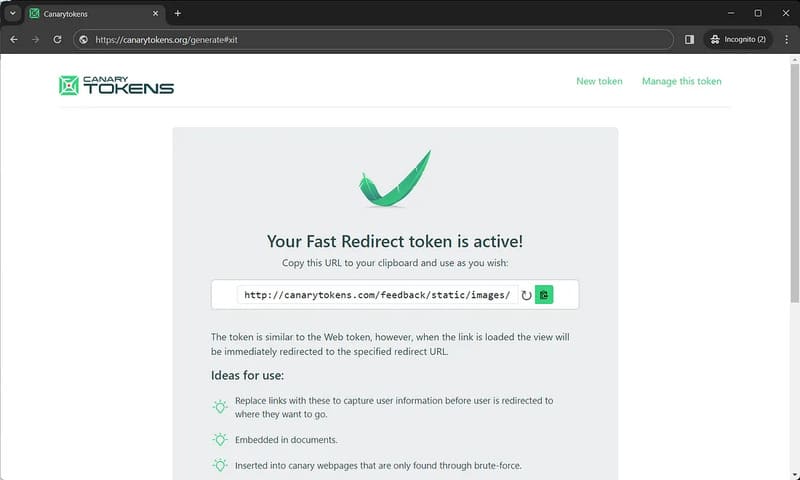
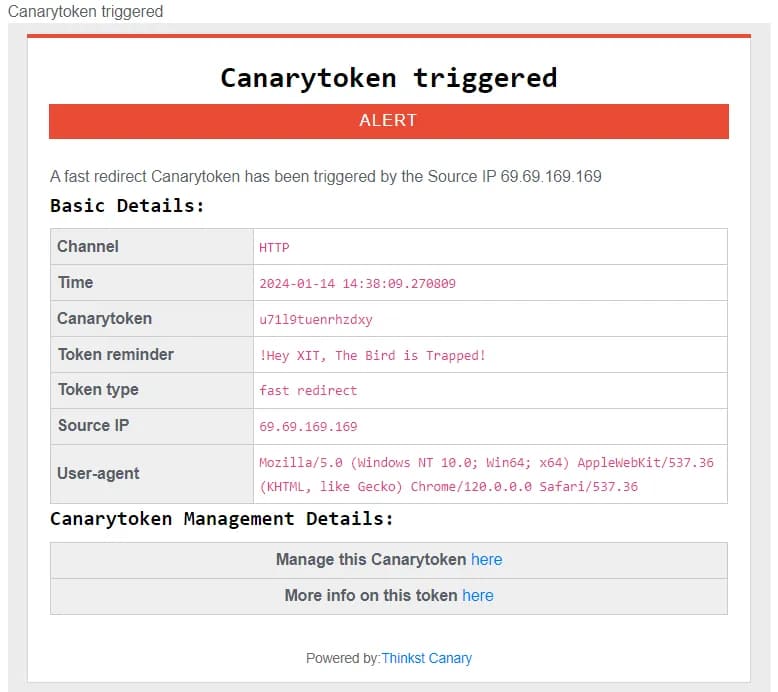
If the target visits a URL/File, as in the example above, the token will be fired and sent via email or webhook as below:
Epilogue
How to track anyone's IP using Canarytokens is a simple and effective method to improve network security. By creating and distributing Canarytokens, you can collect valuable information about the target, such as IP, time, device, etc. You can use this information for defense and investigation. , or retaliate against intruders. Good luck!