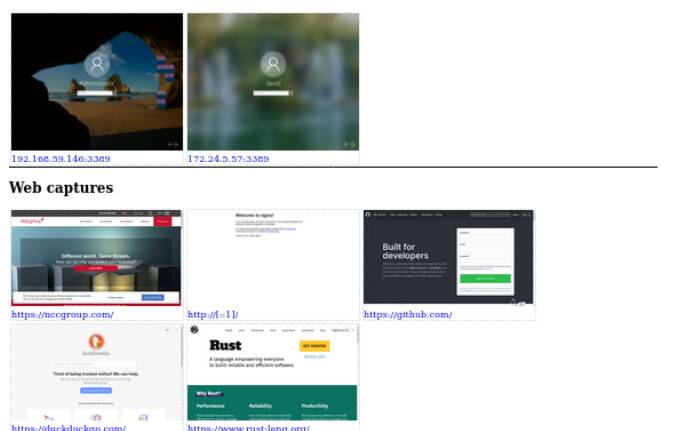
Scrying is a new tool for capturing RDP, Web and VNC screenshots. This tool is still a work in progress and can be used but it is not complete.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |
RDP, Web and VNC are services Remote Desktop help control the computer remotely, if the account is exposed, it is considered that the Hacker has full rights to use your computer.
The web screenshot feature is based on whether Chromium or Google Chrome is installed.
Since Eyewitness has recently stopped supporting RDP, there are no CLI tools that take RDP screenshots. Nessus still works, but it’s a bit difficult to get the image out and it can’t export the file.
So this is a good opportunity for the author to write a new tool that is more powerful than the previous ones.
Install Crying
For the web screenshot feature, the tool has to depend on whether you have Chromium or Google Chrome installed.
Download the latest release at github. Debian versions are available for the distributions to use (install using the sudo dpkg -i scrying* .deb) and binaries for Windows, Mac, and Linux.
Use
Find a website, RDP server or VNC server:
$ scrying -t http:
$ scrying -t rdp:
$ scrying -t 2001:db8::5 --mode web
$ scrying -t 2001:db8::5 --mode rdp
$ scrying -t 192.0.2.2
$ scrying -t vnc:
Crying will automatically get the screenshot from the nmap output:
$ nmap -iL targets.txt -p 80,443,8080,8443,3389 -oX targets.xml
$ scrying --nmap targets.xml
Choose a different output folder for the images:
$ scrying -t 2001:db8::3 --output-dir /tmp/scrying_outputs
Run the targets file:
$ cat targets.txt
http:
rdp:
2001:db8::5
$ scrying -f targets.txt
Run using web proxy:
$ scrying -t http:
$ scrying -t http:
The image file will be saved as PNG in the following folder structure:
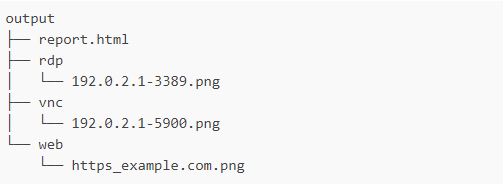
Check the results at file output/report.html
Feature
Features with a check mark next to them represent that the feature has already been completed, other features are in development:
- Automatically decide if the input is a web address or an RDP server
- Automatically create output directory if it doesn’t already exist
- Save images with consistent and unique name in server/IP
- Full support for IPv6 and IPv4 characters as well as hostnames
- Read the targets from the file and decide if they are RDP or HTTP or use hints
- Parsing the target intelligently from the results of Nmap and Nessus
- HTTP – use Chromium/Chrome in headless mode
- Cross-platform support – tested on Linux, Windows and Mac
- Generate HTML reports for easy viewing of results
- VNC
- RDP
- Stream video – tracking
- timestamp option in filename
- Read target from msf service -o csv . output
- OCR on RDP username, directly or on the images folder
- NLA/auth to check credentials
- Parse JSON Dirble output to get a screenshot of the entire web page
Command syntax
USAGE:
scrying [FLAGS] [OPTIONS] <--file <FILE>...|--nmap <NMAP XML FILE>...|--nessus <NESSUS XML FILE>...|--target <TARGET>...>
FLAGS:
-s, --silent Suppress most log messages
--test-import Exit after importing targets
-v, --verbose Increase log verbosity
-h, --help Prints help information
-V, --version Prints version information
OPTIONS:
-f, --file <FILE>... Targets file, one per line
-l, --log-file <LOG FILE> Save logs to the given file
-m, --mode <MODE>
Force targets to be parsed as `web`, `rdp`, `vnc` [default: auto] [possible values:
web, rdp, vnc, auto]
--nessus <NESSUS XML FILE>... Nessus XML file
--nmap <NMAP XML FILE>... Nmap XML file
-o, --output <OUTPUT DIR> Directory to save the captured images in [default: output]
--proxy <PROXY>
Default SOCKS5 proxy to use for connections e.g. socks5://[::1]:1080
--rdp-proxy <RDP PROXY>
SOCKS5 proxy to use for RDP connections e.g. socks5://[::1]:1080
--rdp-timeout <RDP TIMEOUT>
Seconds to wait after last bitmap before saving an image [default: 2]
-t, --target <TARGET>... Target, e.g. http://example.com, rdp://[2001:db8::4]
--threads <THREADS> Number of worker threads for each target type [default: 10]
--web-proxy <WEB PROXY>
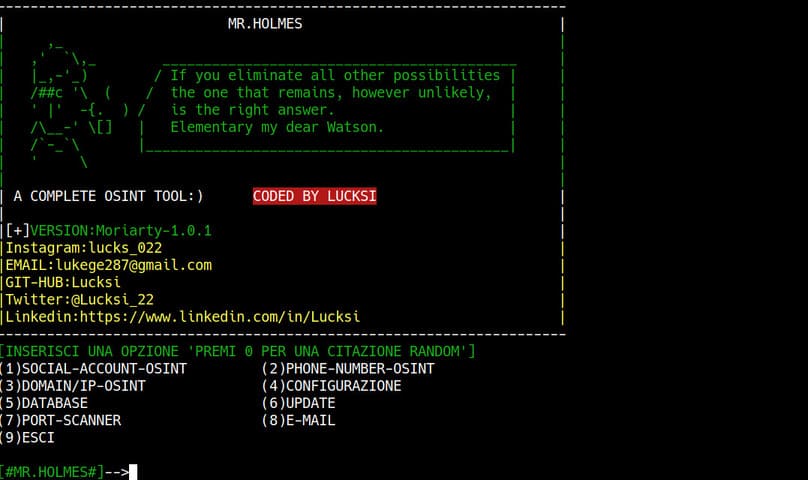
HTTP/SOCKS Proxy to use for web requests e.g. http://[::1]:8080You can also view the article Tools OSINT – Tracing criminals on the Internet, collecting the best intelligence.